Sophos, the world’s leading cyber security firm, has recently released its annual report. The State of Ransomware 2023 report found a slight decrease in the rate of ransomware attacks in Asia Pacific and Japan (APJ) last year.
According to the latest survey, 68 percent of organizations have fallen victim to ransomware, up from 72 percent the previous year. Of the 71 percent of organizations exposed to ransomware surveyed, 49 percent paid a ransom to encrypt information or data, which is slightly lower than last year’s rate of 55 percent, but higher than the 2023 global average of 47 percent.
By infosecbulletin
/ Saturday , July 27 2024
Google fixed a bug in Chrome's Password Manager that caused user credentials to vanish temporarily. A problem with Google Chrome's...
Read More
By infosecbulletin
/ Saturday , July 27 2024
India’s Communications Minister Chandra Sekhar Pemmasani confirmed a breach at the state-owned telecom operator BSNL on May 20 during a...
Read More
By infosecbulletin
/ Saturday , July 27 2024
Malware based threats increased by 30% in the first half of 2024 compared to the same period in 2023, according...
Read More
By infosecbulletin
/ Friday , July 26 2024
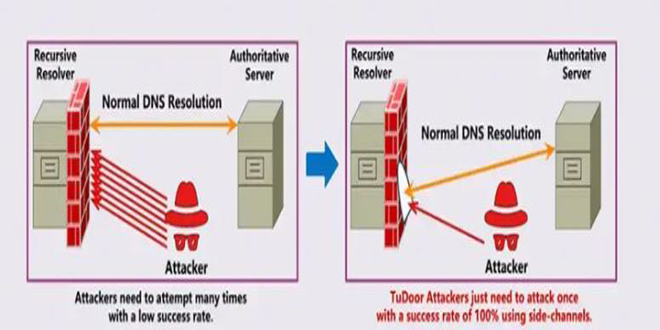
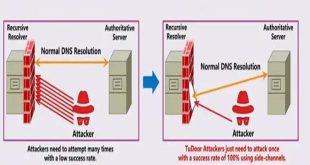
A new critical vulnerability in the Domain Name System (DNS) has been found. This vulnerability allows a specialized attack called...
Read More
By infosecbulletin
/ Friday , July 26 2024
A serious vulnerability, CVE-2023-45249 (CVSS 9.8), has been found in Acronis Cyber Infrastructure (ACI), a widely used software-defined infrastructure solution...
Read More
By infosecbulletin
/ Friday , July 26 2024
OpenAI is testing a new search engine "SearchGPT" using generative artificial intelligence to challenge Google's dominance in the online search...
Read More
By infosecbulletin
/ Thursday , July 25 2024
CISA released two advisories about security issues for Industrial Control Systems (ICS) on July 25, 2024. These advisories offer important...
Read More
By infosecbulletin
/ Thursday , July 25 2024
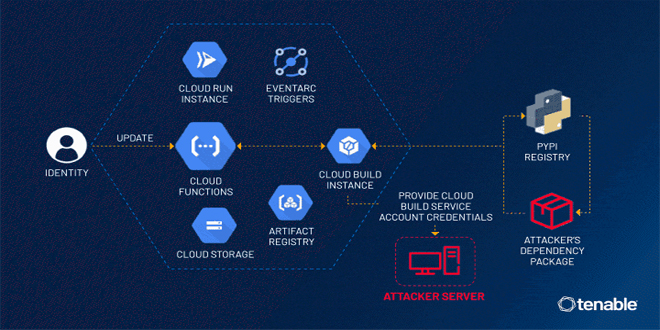
Tenable security researchers found a vulnerability in Google Cloud Platform's Cloud Functions service that could allow an attacker to access...
Read More
By infosecbulletin
/ Thursday , July 25 2024
BDG e-GOV CIRT's Cyber Threat Intelligence Unit has noticed a concerning increase in cyber-attacks against web applications and database servers...
Read More
By infosecbulletin
/ Thursday , July 25 2024
GitLab released a security update today to fix six vulnerabilities in its software. Although none of the flaws are critical,...
Read More
ALSO READ:
Elon Musk’s Neuralink gets permission to put chips in people’s heads
Global studies show that when an organization pays a ransom to decrypt their data, their costs double. While it costs $375,000 to back up the organization’s information, it costs $750,000 just to restore the data. Even after paying the ransom, it takes relatively long time to recover the data. 45 percent of organizations that backed up recovered their data within a week. On the other hand, 39 percent of organizations that paid the ransom required more time.
After analysis, the main causes of ransomware attacks for APJ organizations are attacks on vulnerable systems (in 37 percent cases) and compromised credentials (in 28 percent cases). These aspects of the attack are highlighted in the incident response section of Sophos’ 2023 Active Adversary Report for Business Leaders report.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind