Chronon simplifies data computation and serving for AI/ML apps. Users define data features, and Chronon handles batch and streaming computation, scalable backfills, low-latency serving, correctness, consistency, observability, and monitoring.
It allows you to utilize all of the data within your organization, from batch tables, event streams or services to power your AI/ML projects, without needing to worry about all the complex orchestration that this would usually entail.
By infosecbulletin
/ Saturday , July 27 2024
Google fixed a bug in Chrome's Password Manager that caused user credentials to vanish temporarily. A problem with Google Chrome's...
Read More
By infosecbulletin
/ Saturday , July 27 2024
India’s Communications Minister Chandra Sekhar Pemmasani confirmed a breach at the state-owned telecom operator BSNL on May 20 during a...
Read More
By infosecbulletin
/ Saturday , July 27 2024
Malware based threats increased by 30% in the first half of 2024 compared to the same period in 2023, according...
Read More
By infosecbulletin
/ Friday , July 26 2024
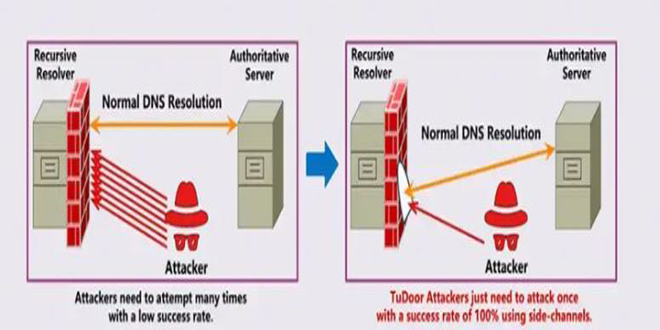
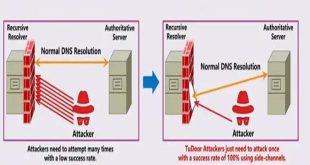
A new critical vulnerability in the Domain Name System (DNS) has been found. This vulnerability allows a specialized attack called...
Read More
By infosecbulletin
/ Friday , July 26 2024
A serious vulnerability, CVE-2023-45249 (CVSS 9.8), has been found in Acronis Cyber Infrastructure (ACI), a widely used software-defined infrastructure solution...
Read More
By infosecbulletin
/ Friday , July 26 2024
OpenAI is testing a new search engine "SearchGPT" using generative artificial intelligence to challenge Google's dominance in the online search...
Read More
By infosecbulletin
/ Thursday , July 25 2024
CISA released two advisories about security issues for Industrial Control Systems (ICS) on July 25, 2024. These advisories offer important...
Read More
By infosecbulletin
/ Thursday , July 25 2024
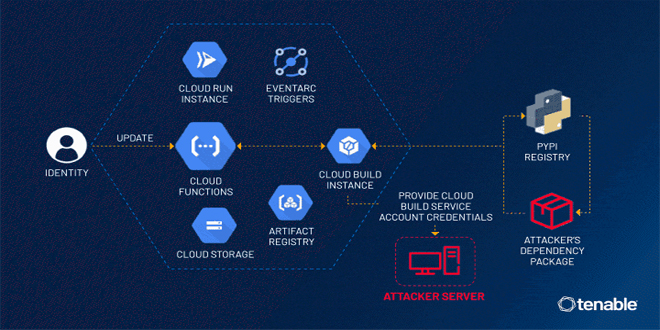
Tenable security researchers found a vulnerability in Google Cloud Platform's Cloud Functions service that could allow an attacker to access...
Read More
By infosecbulletin
/ Thursday , July 25 2024
BDG e-GOV CIRT's Cyber Threat Intelligence Unit has noticed a concerning increase in cyber-attacks against web applications and database servers...
Read More
By infosecbulletin
/ Thursday , July 25 2024
GitLab released a security update today to fix six vulnerabilities in its software. Although none of the flaws are critical,...
Read More
Key features:
Gather data from different sources like event streams, DB table snapshots, change data streams, service endpoints, and warehouse tables categorized as slowly changing dimensions, fact, or dimension tables.
Results can be produced in both online and offline situations. In online contexts, they can serve as scalable, low-latency endpoints for serving features. In offline scenarios, they can be stored as hive tables to generate training data.
Real-time or batch accuracy: Choose between Temporal or Snapshot accuracy for configuring the results. Temporal accuracy updates feature values in real-time for online contexts and produces point-in-time correct features offline. Snapshot accuracy updates features once a day at midnight.
Train models faster by using raw data to fill in training sets instead of waiting months to accumulate feature logs.
Utilize the robust Python API, which offers various data source types, freshness, and contexts as high-level abstractions. These are composed of intuitive SQL primitives such as group-by, join, and select, which are further enhanced with powerful features.
Automate feature monitoring by creating monitoring pipelines to assess the quality of training data, measure the difference between training and serving data, and track changes in features over time. Chronon is free on GitHub.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind