Microsoft Patch Tuesday security updates for November 2023 addressed 63 new vulnerabilities in Microsoft Windows and Windows Components; Exchange Server; Office and Office Components; ASP.NET and .NET Framework; Azure; Mariner; Microsoft Edge (Chromium-based), Visual Studio, and Windows Hyper-V.
The IT giant has addressed vulnerabilities with different severity ratings. Three are Critical, 56 are Important, and four are Moderate.
By infosecbulletin
/ Saturday , July 27 2024
Google fixed a bug in Chrome's Password Manager that caused user credentials to vanish temporarily. A problem with Google Chrome's...
Read More
By infosecbulletin
/ Saturday , July 27 2024
India’s Communications Minister Chandra Sekhar Pemmasani confirmed a breach at the state-owned telecom operator BSNL on May 20 during a...
Read More
By infosecbulletin
/ Saturday , July 27 2024
Malware based threats increased by 30% in the first half of 2024 compared to the same period in 2023, according...
Read More
By infosecbulletin
/ Friday , July 26 2024
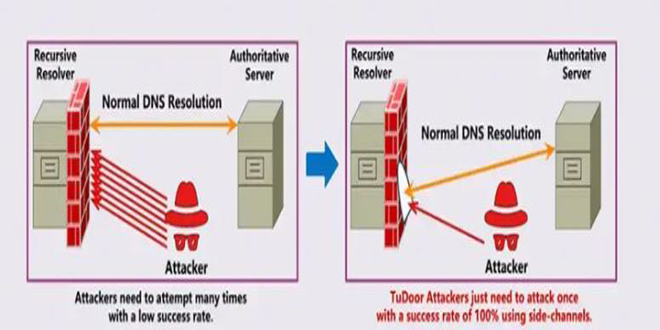
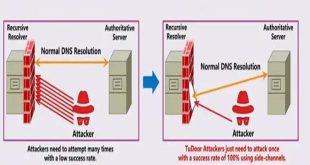
A new critical vulnerability in the Domain Name System (DNS) has been found. This vulnerability allows a specialized attack called...
Read More
By infosecbulletin
/ Friday , July 26 2024
A serious vulnerability, CVE-2023-45249 (CVSS 9.8), has been found in Acronis Cyber Infrastructure (ACI), a widely used software-defined infrastructure solution...
Read More
By infosecbulletin
/ Friday , July 26 2024
OpenAI is testing a new search engine "SearchGPT" using generative artificial intelligence to challenge Google's dominance in the online search...
Read More
By infosecbulletin
/ Thursday , July 25 2024
CISA released two advisories about security issues for Industrial Control Systems (ICS) on July 25, 2024. These advisories offer important...
Read More
By infosecbulletin
/ Thursday , July 25 2024
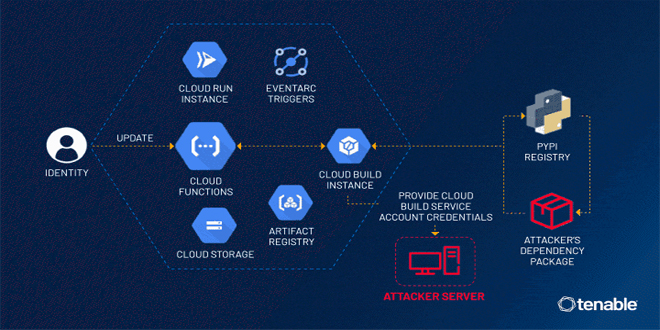
Tenable security researchers found a vulnerability in Google Cloud Platform's Cloud Functions service that could allow an attacker to access...
Read More
By infosecbulletin
/ Thursday , July 25 2024
BDG e-GOV CIRT's Cyber Threat Intelligence Unit has noticed a concerning increase in cyber-attacks against web applications and database servers...
Read More
By infosecbulletin
/ Thursday , July 25 2024
GitLab released a security update today to fix six vulnerabilities in its software. Although none of the flaws are critical,...
Read More
Three of these vulnerabilities are actively exploited in attacks in the wild:
CVE-2023-36033 – Windows DWM Core Library Elevation of Privilege Vulnerability
Attackers can use a vulnerability in the Windows Desktop Manager (DWM) to gain higher privileges. By exploiting this flaw, they can obtain SYSTEM privileges. If combined with a remote code execution bug, this can fully compromise a system.
CVE-2023-36036 – Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability
A flaw in this driver can be abused by an attacker to get SYSTEM privileges. This driver is used to manage files stored in the cloud and is loaded by default on many versions of Windows, making it an easy target for attacks. The post by ZDI mentions that this bug is probably used together with a code execution bug in attacks.
CVE-2023-36025 – Windows SmartScreen Security Feature Bypass Vulnerability
An attacker can use this flaw to bypass Windows Defender SmartScreen checks and other prompts. This flaw can be used in phishing campaigns to avoid warnings about opening a malicious document.
ALSO READ:
Juniper Patches Over 30 Vulnerabilities in Junos OS
The main issue fixed by Microsoft’s Patch Tuesday security updates for November 2023 is a Remote Code Execution vulnerability in Windows PGM (Pragmatic General Multicast). This flaw, identified as CVE-2023-36397 (CVSS 9.8), allows an attacker to execute code with higher privileges without needing user interaction.
The full list of vulnerabilities addressed by Microsoft for November 2023 is available here.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind