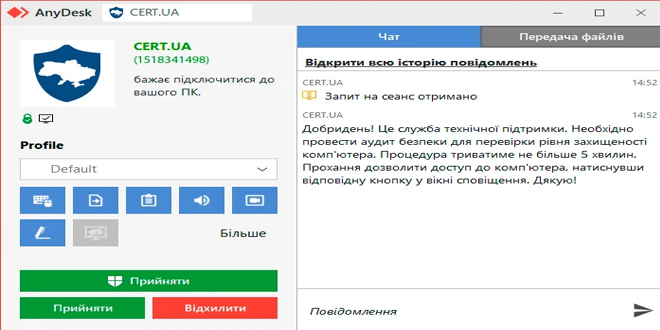
Attackers are pretending to be Ukraine’s Computer Emergency Response Team (CERT-UA) using AnyDesk to access target computers.
“Unidentified individuals are sending connection requests via AnyDesk under the pretext of conducting a ‘security audit to verify the level of protection,’ using the name ‘CERT.UA,’ the CERT-UA logo, and the AnyDesk ID “1518341498” (which may vary),” CERT-UA explained on Friday.
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
By infosecbulletin
/ Monday , June 16 2025
SafetyDetectives’ Cybersecurity Team discovered a public post on a clear web forum in which a threat actor claimed to have...
Read More
By infosecbulletin
/ Sunday , June 15 2025
WestJet, Canada's second-largest airline, is looking into a cyberattack that has affected some internal systems during its response to the...
Read More
By infosecbulletin
/ Saturday , June 14 2025
Resecurity found 7.4 million records of Paraguayan citizens' personal information leaked on the dark web today. Last week, cybercriminals attempted...
Read More
By infosecbulletin
/ Friday , June 13 2025
HashiCorp has revealed a critical vulnerability in its Nomad tool that may let attackers gain higher privileges by misusing the...
Read More
By infosecbulletin
/ Friday , June 13 2025
SoftBank has disclosed that personal information of more than 137,000 mobile subscribers—covering names, addresses, and phone numbers—might have been leaked...
Read More
By infosecbulletin
/ Friday , June 13 2025
Serious security vulnerabilities in Trend Micro Apex One could allow attackers to inject malicious code and elevate their privileges within...
Read More
The requests appear to be haphazardly sent, with the attackers relying on users to accept them without skepticism: “It is evident that attackers are once again resorting to social engineering methods based on trust and the use of authority.”
To send a connection request, the attacker must know the target’s AnyDesk ID and the remote access software must be operational on their device.
They think the attackers may have obtained the targets’ AnyDesk IDs by compromising other computers where remote access was previously allowed.
AnyDesk and other remote access tools are often leveraged by a variety of attackers to gain access to target computers.
Ukraine’s national CERT uses remote access tools to help users combat and manage cyber incidents. These interventions are done only through pre-approved communication channels. A connection requests out of the blue should, therefore, raise potential targets’ suspicions.
The team is unsure if the targets are government workers, company employees, or private individuals. They advise anyone receiving such connection requests to report them to relevant cyber protection units or CERT-UA.
OWASP Reveils Top 10 Smart Contract Vulnerabilities for 2025
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind