RansomHub targets Bangladeshi Confidence group of companies limited. The rapidly growing RansomHub ransomware group set time to release the data. The time remaining 4 days to release while publishing the report.
According to the RansomHub ransomware group post, they are going to publish 350GB of confidence group data after the specified countdown. According to National Attack Surface (NAS), The exact nature of the stolen data and the specific servers that were compromised remain unknown.
Confidence Group of Companies Limited, established in 1991, is a key player in mid-tech manufacturing in Bangladesh. It operates in various sectors, including cement production, power generation, and the production of Spun Pre-stressed Concrete poles. The conglomerate comprises eight business entities and is led by Chairman Rezaul Karim and Vice-Chairman Imran Karim.
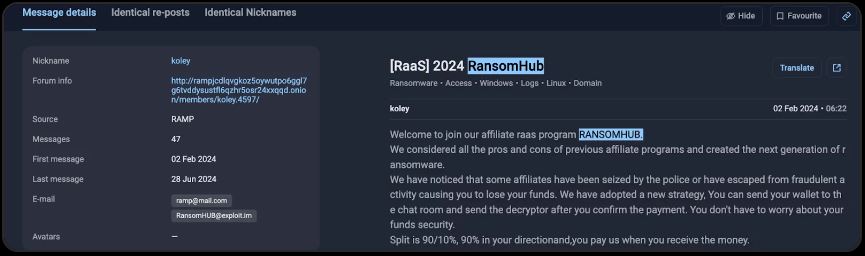
RansomHub launched its affiliate RaaS program in February 2024 and introduced itself on the RAMP dark web forum on February 2 under the username “koley.” They invited partners by promising 90% of the ransom payments to affiliates and keeping 10% for RansomHub.
Symantec’s analysis shows that RansomHub is very similar to Knight ransomware, suggesting that Knight may have inspired its development. However, the original creators of Knight are not linked to RansomHub, as Knight’s source code was sold on underground forums after its creators disbanded earlier this year. It’s likely that others bought and improved the code before releasing RansomHub.
RansomHub is a ransomware group that uses a double-extortion method by encrypting files and stealing sensitive data to force victims to pay large ransoms. They mainly target the healthcare, finance, and government sectors in the U.S., U.K., Spain, France, and Italy. Their tactics involve using compromised domain accounts and public VPNs to gain access, followed by data theft and extensive encryption. Their recent launch of a RaaS affiliate program and focus on high ransom demands show their aggressive and evolving strategies.
According to NAS Since February 2024 RansomHub has already victimized 315 companies worldwide, marking it as a serious and growing global cybersecurity threat.
Recently cyber attack increased alarmingly in Bangladesh. Organizations working on cyber security reported on ransomware attack on Globe Pharmaceuticals, Lumma C2 malware attack in several websites and 32.4% government websites faces cyber attack.
Organizations need to improve cybersecurity by implementing strong access controls, monitoring networks closely, and developing effective incident response strategies.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














