NGINX team released important updates for their web server software and is advising users to upgrade as soon as possible. The updates fix four important vulnerabilities in the HTTP/3 implementation, especially affecting configurations using the “ngx_http_v3_module.”
CVE-2024-32760:
A vulnerability in NGINX Plus or NGINX OSS causes HTTP/3 QUIC module to be misconfigured, leading to potential termination of NGINX worker processes or other issues.
By infosecbulletin
/ Saturday , July 27 2024
Google fixed a bug in Chrome's Password Manager that caused user credentials to vanish temporarily. A problem with Google Chrome's...
Read More
By infosecbulletin
/ Saturday , July 27 2024
India’s Communications Minister Chandra Sekhar Pemmasani confirmed a breach at the state-owned telecom operator BSNL on May 20 during a...
Read More
By infosecbulletin
/ Saturday , July 27 2024
Malware based threats increased by 30% in the first half of 2024 compared to the same period in 2023, according...
Read More
By infosecbulletin
/ Friday , July 26 2024
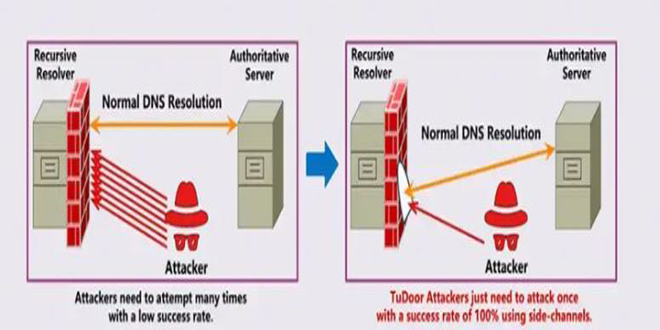
A new critical vulnerability in the Domain Name System (DNS) has been found. This vulnerability allows a specialized attack called...
Read More
By infosecbulletin
/ Friday , July 26 2024
A serious vulnerability, CVE-2023-45249 (CVSS 9.8), has been found in Acronis Cyber Infrastructure (ACI), a widely used software-defined infrastructure solution...
Read More
By infosecbulletin
/ Friday , July 26 2024
OpenAI is testing a new search engine "SearchGPT" using generative artificial intelligence to challenge Google's dominance in the online search...
Read More
By infosecbulletin
/ Thursday , July 25 2024
CISA released two advisories about security issues for Industrial Control Systems (ICS) on July 25, 2024. These advisories offer important...
Read More
By infosecbulletin
/ Thursday , July 25 2024
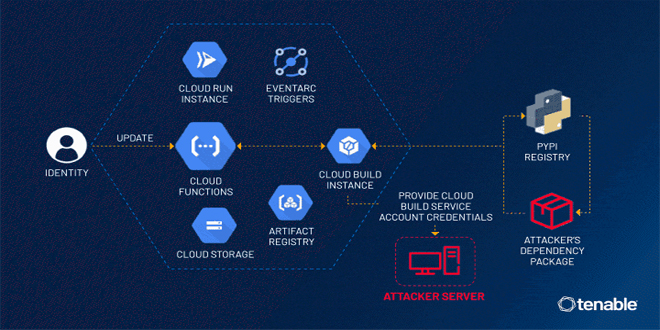
Tenable security researchers found a vulnerability in Google Cloud Platform's Cloud Functions service that could allow an attacker to access...
Read More
By infosecbulletin
/ Thursday , July 25 2024
BDG e-GOV CIRT's Cyber Threat Intelligence Unit has noticed a concerning increase in cyber-attacks against web applications and database servers...
Read More
By infosecbulletin
/ Thursday , July 25 2024
GitLab released a security update today to fix six vulnerabilities in its software. Although none of the flaws are critical,...
Read More
CVE-2024-31079:
Vulnerabilities in NGINX can cause termination of worker processes due to a specific type of HTTP/3 request. Exploiting this issue involves timing the requests during the connection draining process, making it difficult for attackers to manipulate.
CVE-2024-35200:
A vulnerability caused by certain HTTP/3 requests, leading to NGINX worker process termination.
CVE-2024-34161:
NGINX Plus and NGINX OSS can experience a memory leakage problem when using the HTTP/3 QUIC module on networks with a Maximum Transmission Unit (MTU) of 4096 or more without fragmentation, potentially causing previously freed memory to leak due to undisclosed QUIC packets.
EzoicNGINX Plus users got an update called Release 32 (R32) with security patches and bug fixes, based on nginx 1.25.5.
The Medium severity vulnerabilities in NGINX’s HTTP/3 capabilities can pose a significant risk to websites and applications.
To ensure the security and stability of web services, administrators and users should update their NGINX installations to the latest versions, nginx 1.27.0 and 1.26.1, promptly.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind