Research is regularly published about Asian APT groups targeting organizations from different industries. These campaigns and incidents don’t only happen in one region.
Research like this usually includes detailed information about the tools used by APT actors, the vulnerabilities they exploit, and sometimes even specific attribution. Despite the abundance of these reports, companies often lack preparation to fend off such attackers.
By infosecbulletin
/ Tuesday , October 22 2024
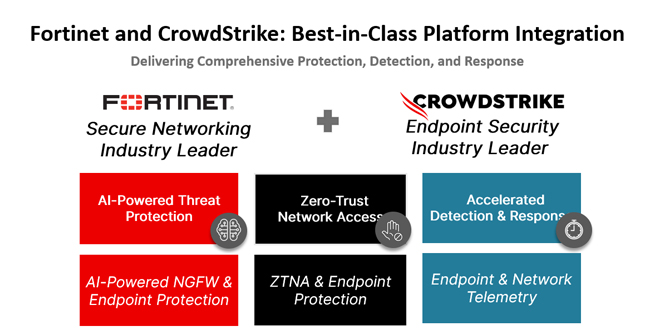
In today's rapidly changing cybersecurity environment, organizations encounter numerous complex threats targeting endpoints and networks. CrowdStrike and Fortinet have partnered...
Read More
By infosecbulletin
/ Tuesday , October 22 2024
Sophos, based in the UK, is to acquire Secureworks, a Nasdaq-listed company, for $859 million in cash from Dell Technologies....
Read More
By infosecbulletin
/ Monday , October 21 2024
The Internet Archive was breached again, this time through their Zendesk email support platform, following warnings that threat actors had...
Read More
By infosecbulletin
/ Sunday , October 20 2024
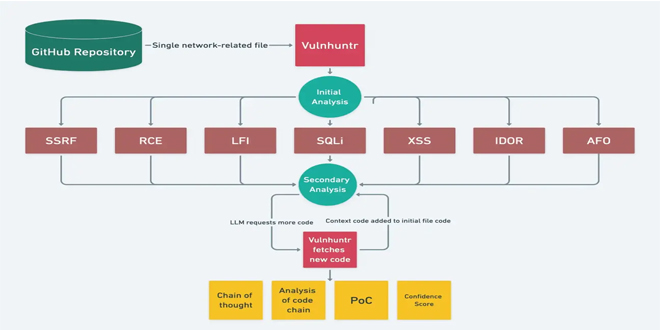
In today's changing cybersecurity environment, it's essential to find vulnerabilities in code. Vulnhuntr, an open-source tool on GitHub, uses Large...
Read More
By infosecbulletin
/ Friday , October 18 2024
Bitdefender said a vulnerability has been identified in Bitdefender Total Security HTTPS scanning functionality where the software fails to properly...
Read More
By infosecbulletin
/ Thursday , October 17 2024
Cybersecurity threats have surged to extraordinary heights, as Microsoft’s latest Digital Defense Report reveals that its customers are confronted with...
Read More
By infosecbulletin
/ Thursday , October 17 2024
VMware has issued a warning about a remote code execution vulnerability, CVE-2024-38814, with a CVSS score of 8.8, in its...
Read More
By infosecbulletin
/ Thursday , October 17 2024
Mandiant researchers found that over 90 zero-day vulnerabilities and more than 40 known vulnerabilities were exploited in the wild. Vulnerabilities...
Read More
By infosecbulletin
/ Wednesday , October 16 2024
Oracle's October 2024 Critical Patch Update has fixed 334 security vulnerabilities in its products. The CPU affects 28 Oracle product...
Read More
By infosecbulletin
/ Wednesday , October 16 2024
Google has released Chrome 130, fixing 17 security vulnerabilities. The update (version 130.0.6723.58/.59 for Windows and Mac, and 130.0.6723.58 for...
Read More
ALSO READ:
Exploring engagement of political parties on Facebook in Bangladesh
Cybersecurity professionals need advanced tools and techniques to combat threats. Along with expertise and experience, they also require infrastructure, asset management, vulnerability management, network segmentation, audits, and data security tools. Unprepared infrastructure is often the main reason Asian APT groups can carry out successful attacks.
Securlist report on Asian APT groups reveals their valuable intelligence. These groups attack many countries and industries. Our analysis of hundreds of attacks shows a common pattern and limited techniques used in various stages of the Cyber Kill Chain. Unfortunately, security teams struggle to detect these attacks in their own infrastructure.
Intended audience of this report:
The report provide the cybersecurity community with the best-prepared intelligence data to effectively counteract Asian APT groups. This report will be the most helpful to the following:
SOC analysts
Cyber Threat Intelligence analysts
Threat Hunting experts
Digital Forensics (DFIR) experts
Cybersecurity experts
Domain administrators
C-Level executives responsible for cybersecurity at their companies
This material is a knowledge library about the main approaches used by Asian APT groups for hacking infrastructure. The report contains detailed information about the attackers’ tactics, techniques, and procedures (TTPs) based on the MITRE ATT&CK methodology.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind