Ivanti on Tuesday declare to patch for several products, including fixes for critical vulnerabilities in Endpoint Manager (EPM). Ivanti resolved six out of the ten security defects resolved in EPM are critical-severity SQL Injection bugs. Tracked as CVE-2024-29822 through CVE-2024-29827, the bugs impact the Core server of Ivanti EPM 2022 SU5 scoring CVSS score of 9.
The vendor released hot fixes for EPM 2022 SU5 which resolve four other SQL injection vulnerabilities in EPM 2022 SU5 and prior releases that could also be exploited to execute arbitrary code from the network, without authentication. Ivanti also announced patches for a high-severity unrestricted file upload bug in the web component of Ivanti Avalanche.
By infosecbulletin
/ Saturday , July 27 2024
India’s Communications Minister Chandra Sekhar Pemmasani confirmed a breach at the state-owned telecom operator BSNL on May 20 during a...
Read More
By infosecbulletin
/ Saturday , July 27 2024
Malware based threats increased by 30% in the first half of 2024 compared to the same period in 2023, according...
Read More
By infosecbulletin
/ Friday , July 26 2024
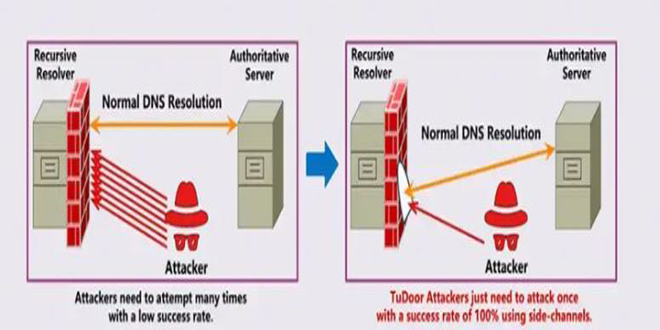
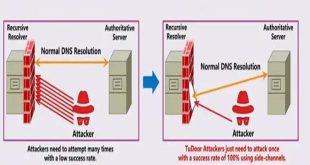
A new critical vulnerability in the Domain Name System (DNS) has been found. This vulnerability allows a specialized attack called...
Read More
By infosecbulletin
/ Friday , July 26 2024
A serious vulnerability, CVE-2023-45249 (CVSS 9.8), has been found in Acronis Cyber Infrastructure (ACI), a widely used software-defined infrastructure solution...
Read More
By infosecbulletin
/ Friday , July 26 2024
OpenAI is testing a new search engine "SearchGPT" using generative artificial intelligence to challenge Google's dominance in the online search...
Read More
By infosecbulletin
/ Thursday , July 25 2024
CISA released two advisories about security issues for Industrial Control Systems (ICS) on July 25, 2024. These advisories offer important...
Read More
By infosecbulletin
/ Thursday , July 25 2024
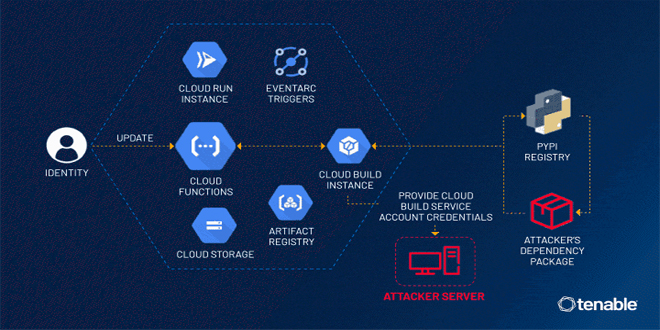
Tenable security researchers found a vulnerability in Google Cloud Platform's Cloud Functions service that could allow an attacker to access...
Read More
By infosecbulletin
/ Thursday , July 25 2024
BDG e-GOV CIRT's Cyber Threat Intelligence Unit has noticed a concerning increase in cyber-attacks against web applications and database servers...
Read More
By infosecbulletin
/ Thursday , July 25 2024
GitLab released a security update today to fix six vulnerabilities in its software. Although none of the flaws are critical,...
Read More
By infosecbulletin
/ Thursday , July 25 2024
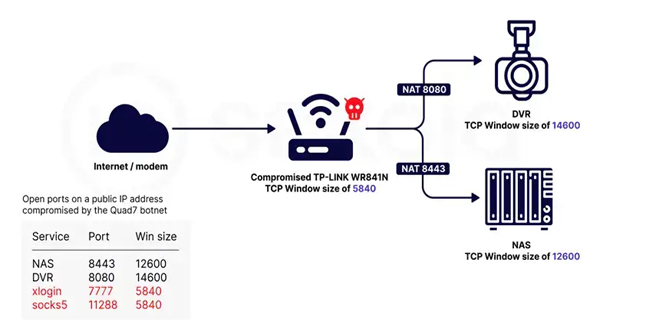
Sekoia.io and Intrinsec analyzed the Quad7 (7777) botnet, which uses TCP port 7777 on infected routers to carry out brute-force...
Read More
Ivanti said, “It is highly recommended to download the Avalanche installer and update to the latest Avalanche 6.4.3.602. The installation will apply a fix for the single CVE but will also include previously released CVE fixes and security hardenings,”.
Patches were rolled out for five other high-severity vulnerabilities as well: an SQL injection and an unrestricted file upload bug in Neurons for ITSM, a CRLF injection flaw in Connect Secure, and two local privilege escalation issues in the Secure Access client for Windows.
In addition, patches have been shipped for five other high-severity vulnerabilities: an SQL injection (CVE-2024-22059) and an unrestricted file upload bug (CVE-2024-22060) in Neurons for ITSM, a CRLF injection flaw in Connect Secure (CVE-2023-38551), and two local privilege escalation issues in the Secure Access client for Windows (CVE-2023-38042) and Linux (CVE-2023-46810).
Ivanti said that there is no evidence of the flaws being exploited in the wild or that they were “introduced into our code development process maliciously” via a supply chain attack.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind