Bangladesh Bank has alerted all scheduled banks to enhance their cybersecurity measures to protect sensitive financial data and ICT systems due to increasing cyber threats in the banking sector.
Key Areas of Concern and Required Actions:
Operating System & Software Patching:
Ensure all servers and critical systems are regularly updated and patched to mitigate known vulnerabilities.
Privileged Access Management:
Strictly limit administrative and root-level access, enforce access segregation, and apply the principle of least privilege.
Data Backup:
Implement a robust 3-2-1 backup strategy, ensuring offsite and encrypted backups with regular restore tests.
Data Encryption:
Enforce encryption for data at rest, in transit, and during processing.
Multi-Factor Authentication (MFA):
Mandatory for accessing all critical systems.
Threat Monitoring & Detection:
Utilize advanced threat detection systems such as:
Security Information and Event Management (SIEM)
Network Intrusion Detection Systems (NIDS)
Endpoint Detection and Response (EDR)
User and Entity Behavior Analytics (UEBA)
Email Security:
Deploy anti-phishing and spoofing protection using DMARC, SPF, and DKIM protocols.
Incident Response Preparedness:
Maintain a robust Incident Response Plan (IRP) and regularly test response playbooks for DDoS, ransomware, phishing, and insider threats.
Remote Access Control:
Enforce strict controls over VPNs and privileged accounts, including audit logging and periodic reviews.
Web Application Security:
Perform regular application-level vulnerability scans and integrate secure coding practices.
Load Balancing and Redundancy:
Adopt load balancer solutions for high availability and traffic management.
Fallback and Continuity Planning:
Develop and routinely update Fallback, Business Continuity (BCP), and Disaster Recovery (DRP) plans.
Bangladesh Bank stresses the need for proactive cybersecurity due to changing digital threats. All banks must submit compliance reports after implementing these measures. The central bank will keep monitoring progress and provide guidance as necessary.
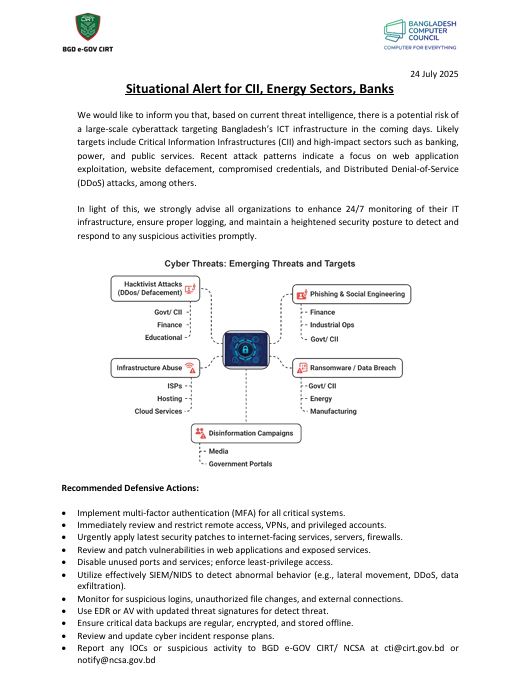
Prior to that, 0n 24 july, BGD e-GOV CIRT alert for a potential risk of cyber attack . In its situational alert, CIRT said, based on current threat intelligence, there is a potential risk of a large-scale cyberattack targeting Bangladesh’s ICT infrastructure in the coming days.
CIRT mentioned that the cyber attack focuses on Critical Information Infrastructures (CII) and high-impact sectors such as banking, power, and public services.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














