Fortinet reported that in the second half of 2023, the average time form the disclosure of a vulnerability to its active exploitation in the wild decreased to just 4.76 days a 43% reduction compared to the 1st half of the year.
Fortinet’s 2H Global landscape report indicate that hackers to rush to infiltrates’ the networks to deploy malicious payloads giving less chance to the organization to patch the vulnerable system.
Derek Manky, Chief Security Strategist at Fortinet’s FortiGuard Labs said, “The pressure on already stretched cyber-defense resources has intensified with the time-to-exploit decreasing significantly to just 4.76 days,”.
“The ability to quickly sift through a prioritized list of vulnerabilities, effectively managing these ‘ticking time bombs,’ is now more critical than ever.”
According to the report, more than 6,00,000 network sensors capture threat event of live production environment across the globe where 41% organizations detected actively exploitation less than one month old. Threat actor leveraging this narrow window to breach the systems through unpatched vulnerabilities.
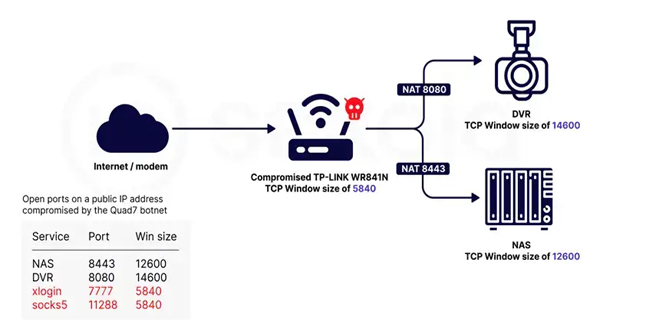
Fortinet observed in the 2nd half of 2023, Hackers were in the target of IOT devices and vendors like D-link, Zyxel, Mikro Tik and Dasan. Caitlin Condon, senior manager of security research at Rapid7 said, “A large number of vulnerabilities are being exploited before security teams have any time to implement patches or other mitigations,”.
In 2023, There were some widely exploited vulnerabilities which impacted a range of famous software platforms and applications like
PaperCut NG (CVE-2023-27350) – Exploited by LockBit ransomware
Google Chrome (CVE-2023-0699) – Exploited by LockBit ransomware
Fortra GoAnywhere (CVE-2023-0669) – Exploited by Cl0p ransomware
MOVEit Transfer (CVE-2023-34362) – Exploited by Cl0p ransomware
Citrix NetScaler ADC and Gateway (CVE-2023-4966) – Exploited by LockBit ransomware.
Security experts are recommended that organizations use a combination of scanning and detection technologies, thoroughly list all public-facing assets, and priorities patching based on actual threat activity. Click here to read out the Fortinet’s Global Threat Landscape Report 2H 2023.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind