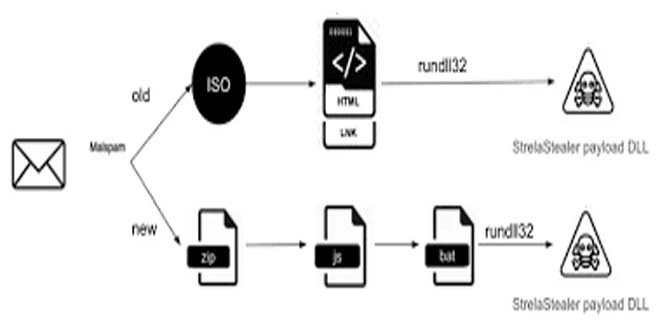
StrelaStealer malware steals email login data from popular email clients and sends it to the attacker’s server. The attacker can then use this information to launch more attacks. Since its first appearance in 2022, the threat actor has carried out many email campaigns and shows no sign of stopping.
Unit42 researchers have found a wave of big StrelaStealer campaigns affecting more than 100 organizations in the EU and U.S. These campaigns involve spam emails with attachments that activate the StrelaStealer’s DLL payload.
By infosecbulletin
/ Wednesday , June 4 2025
IBM has issued a security advisory for vulnerabilities in its QRadar Suite Software and Cloud Pak for Security platforms. These...
Read More
By infosecbulletin
/ Wednesday , June 4 2025
As Bangladesh prepares for the extended Eid-ul-Adha holidays, the BGD e-GOV Computer Incident Response Team (CIRT) has issued an urgent...
Read More
By infosecbulletin
/ Tuesday , June 3 2025
In March 2025, the Threatfabric mobile Threat Intelligence team identified Crocodilus, a new Android banking Trojan designed for device takeover....
Read More
By infosecbulletin
/ Tuesday , June 3 2025
Qualcomm has issued security patches for three zero-day vulnerabilities in the Adreno GPU driver, affecting many chipsets that are being...
Read More
By infosecbulletin
/ Monday , June 2 2025
Roundcube Webmail has fixed a critical security flaw that could enable remote code execution after authentication. Disclosed by security researcher...
Read More
By infosecbulletin
/ Sunday , June 1 2025
A hacker known as "303" claim to breach the company's systems and leaked sensitive internal data on a dark web...
Read More
By infosecbulletin
/ Sunday , June 1 2025
CISA and ACSC issued new guidance this week on how to procure, implement, and maintain SIEM and SOAR platforms. SIEM...
Read More
By infosecbulletin
/ Saturday , May 31 2025
The Qualys Threat Research Unit (TRU) found two local information-disclosure vulnerabilities in Apport and systemd-coredump. Both issues are race-condition vulnerabilities....
Read More
By infosecbulletin
/ Saturday , May 31 2025
New ransomware payment reporting rules take effect in Australia yesterday (May 30) for all organisations with an annual turnover of...
Read More
By infosecbulletin
/ Saturday , May 31 2025
Global makers of surveillance gear have clashed with Indian regulators in recent weeks over contentious new security rules that require...
Read More
Attackers change email attachment file formats to evade detection. This prevents detection from previously generated signatures or patterns. The malware author frequently updates the DLL payload with improved obfuscation and anti-analysis techniques. This makes analysis more difficult for analysts and security products.
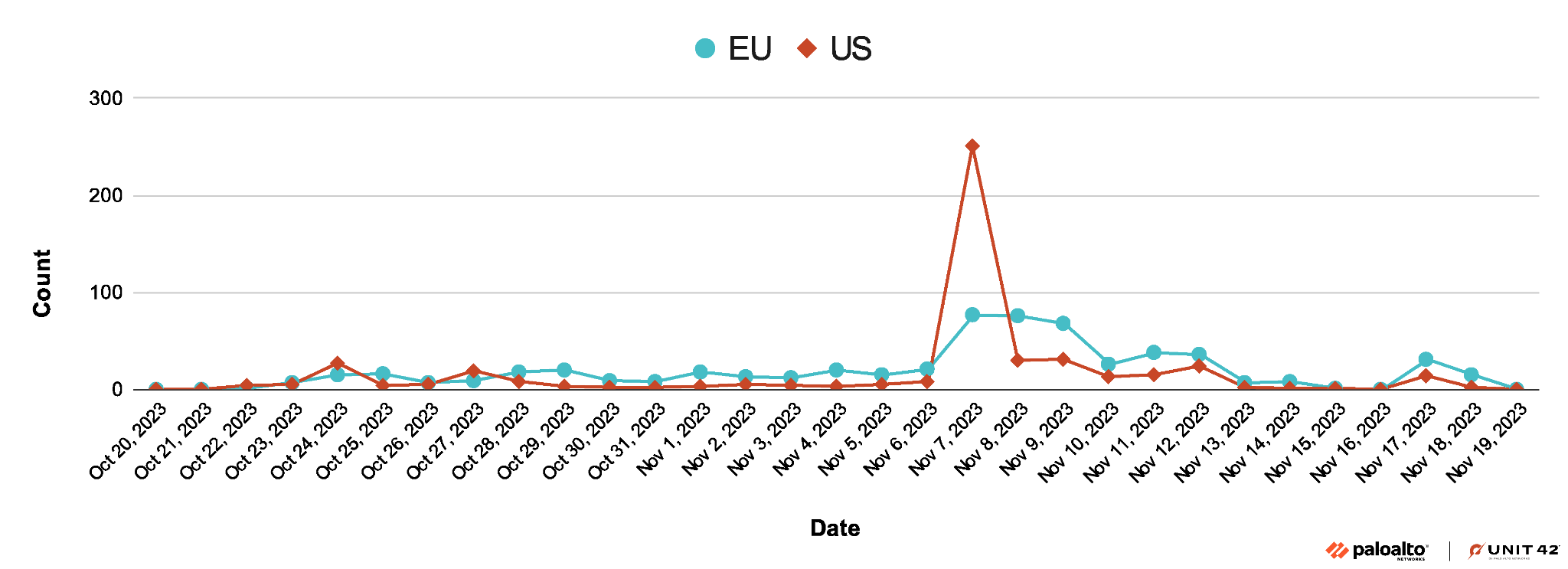
Last Large-Scale Campaign of 2023:
StrelaStealer has been causing multiple large-scale campaigns. The most recent campaign in November 2023 targeted organizations in the U.S. and EU. Figure 1 shows the timeline of this campaign.
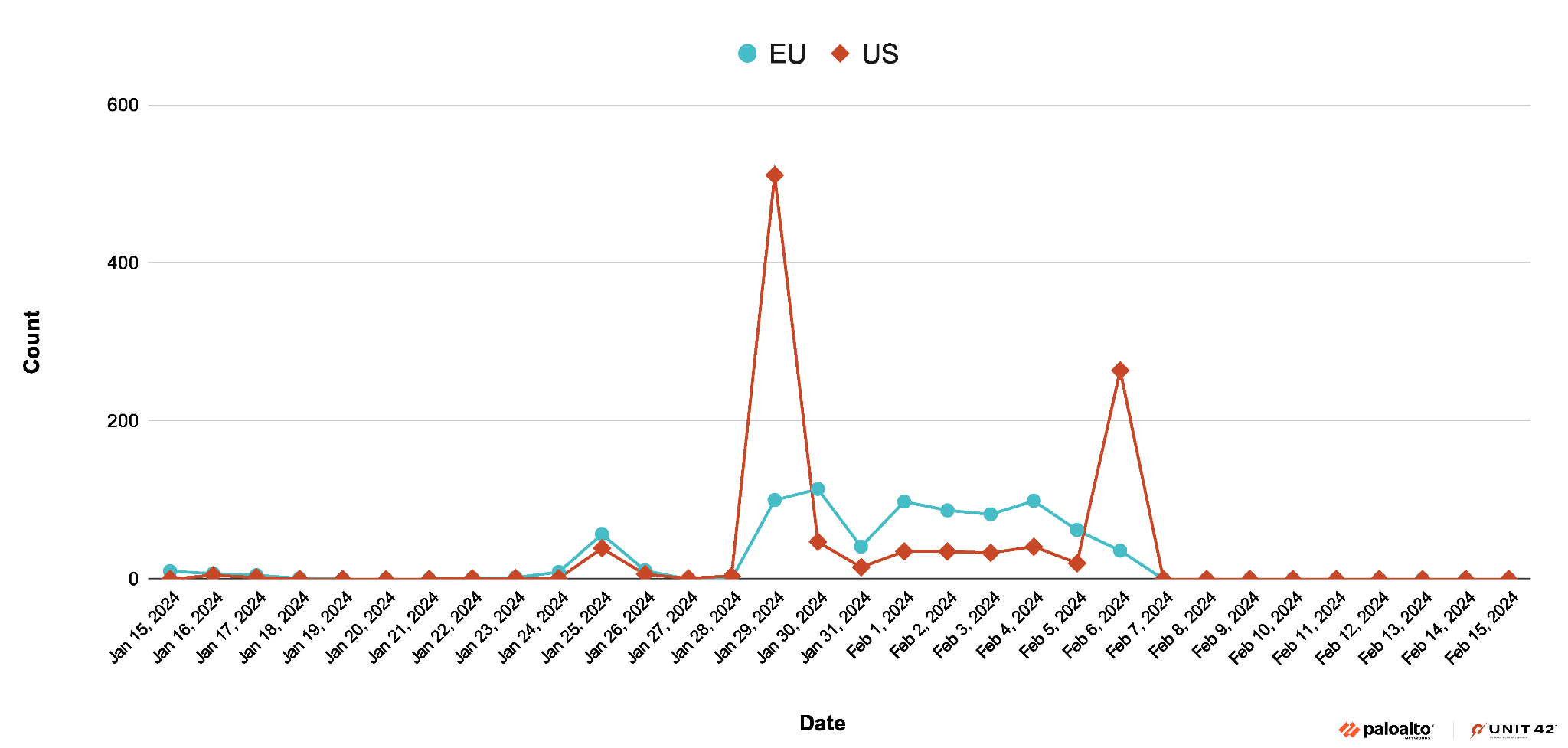
Recent Large-Scale Campaign in 2024
In January 2024, the StrelaStealer threat actors started a big campaign targeting organizations in the same areas as before. The campaign peaked on Jan. 29, 2024.
The language of the StrelaStealer spam email seen during this campaign is localized and the subject line has the pattern of Factura/Rechnung/invoice####. Figure 3, below, is a sample email in German.
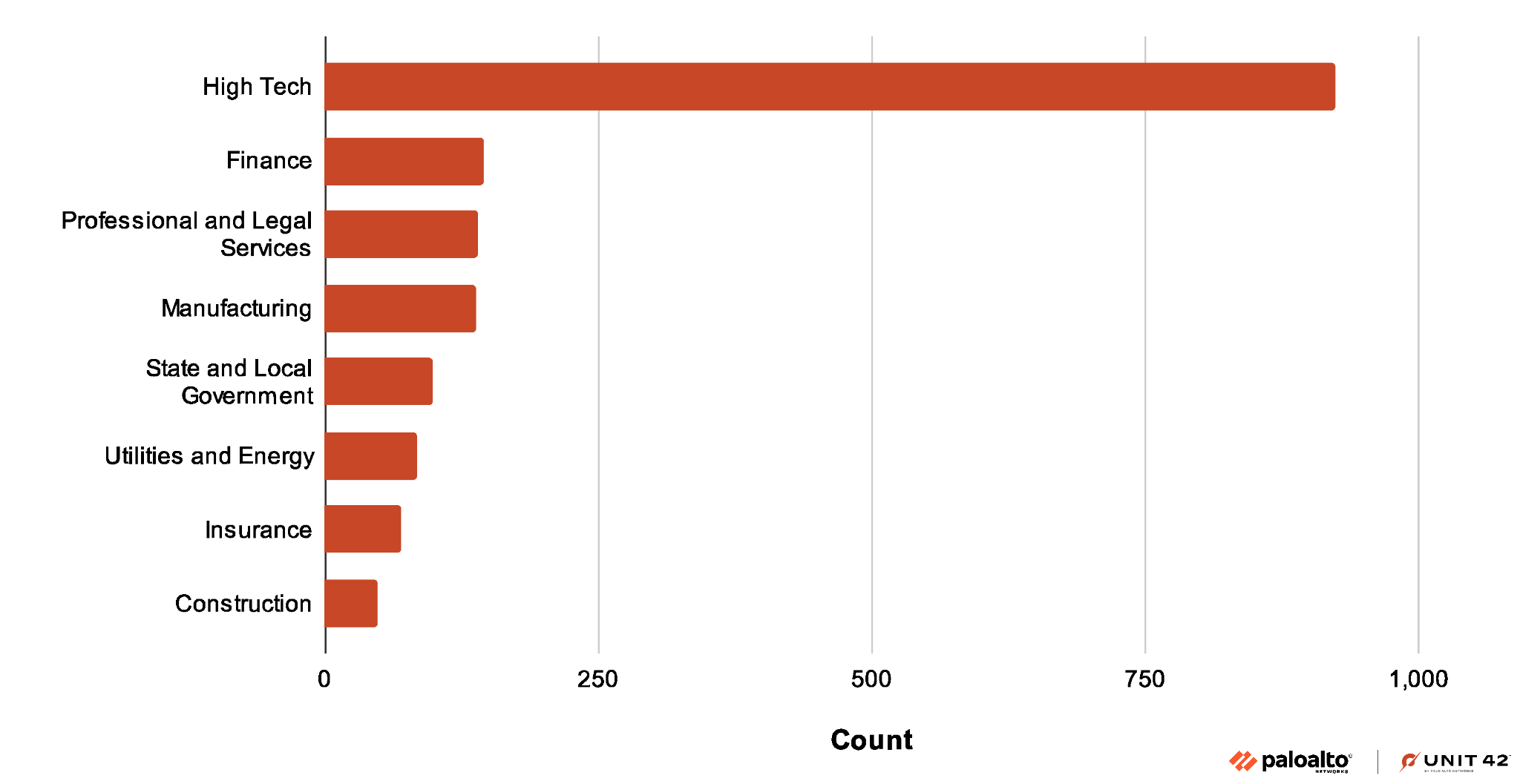
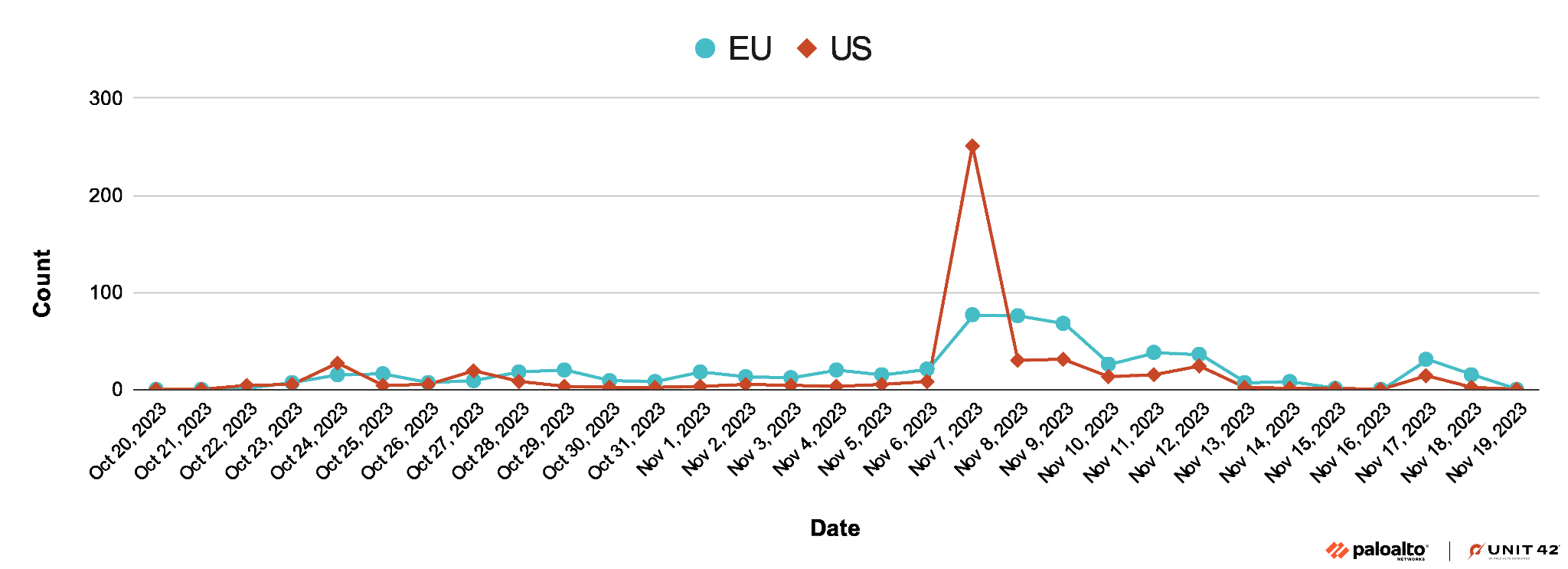 Figure 4 shows that while this recent campaign seems to target organizations in many industries, organizations in the high tech industry have been the largest target.
Figure 4 shows that while this recent campaign seems to target organizations in many industries, organizations in the high tech industry have been the largest target.
For the technical analysis click here.
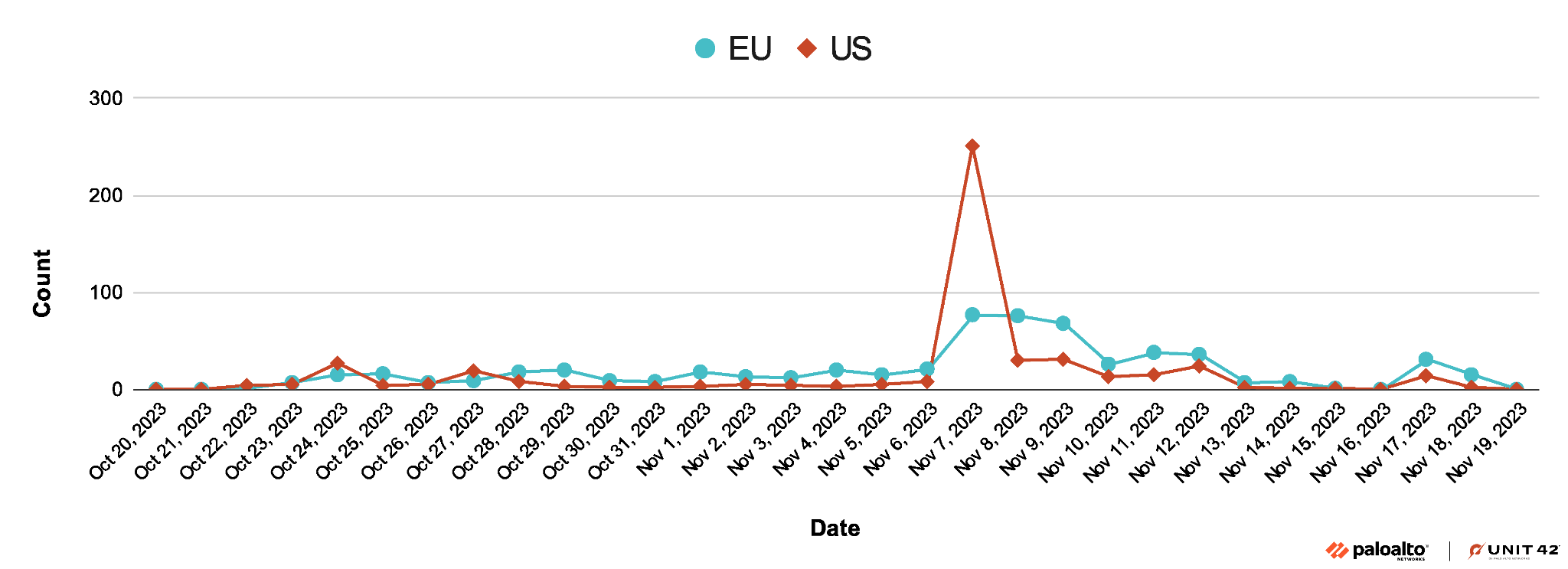
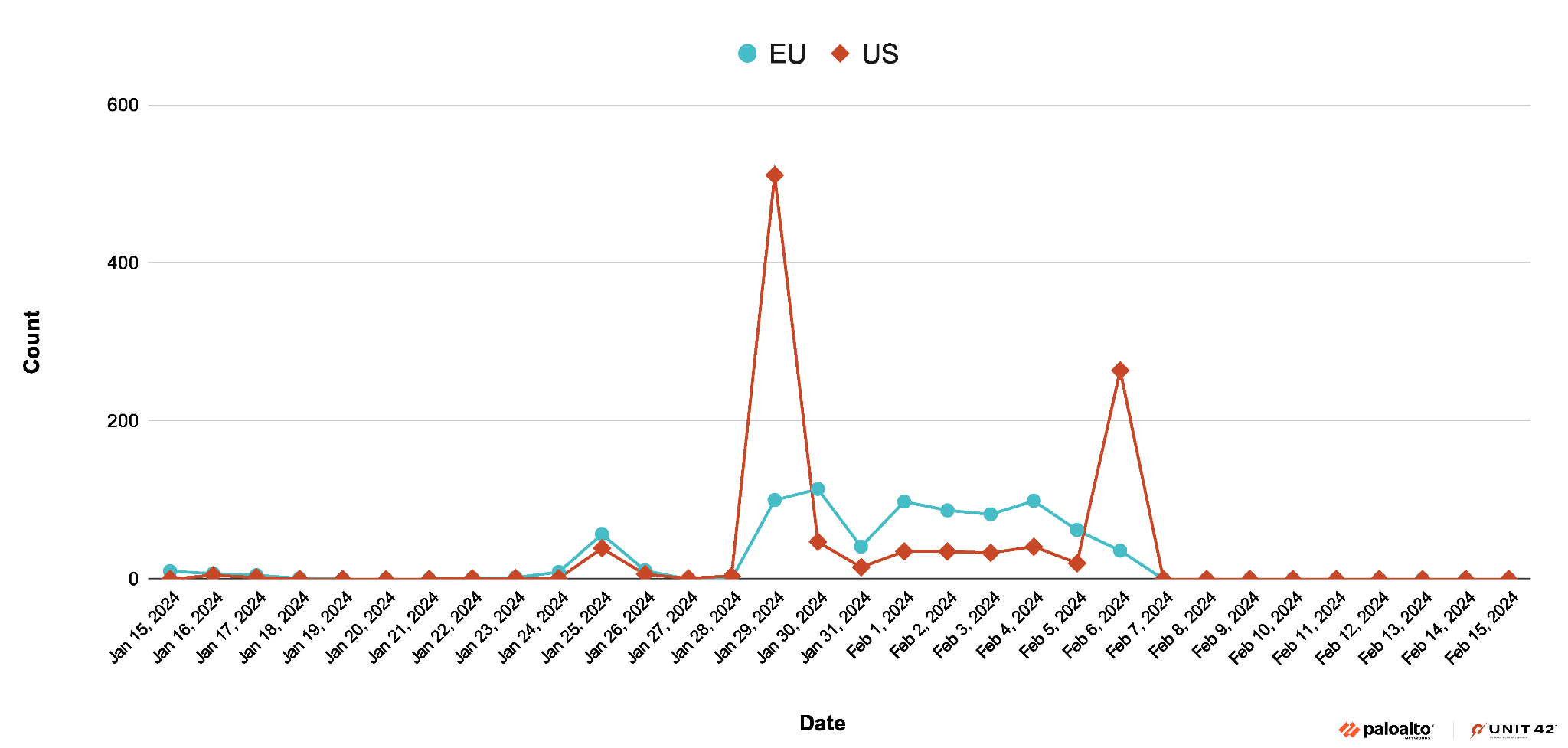
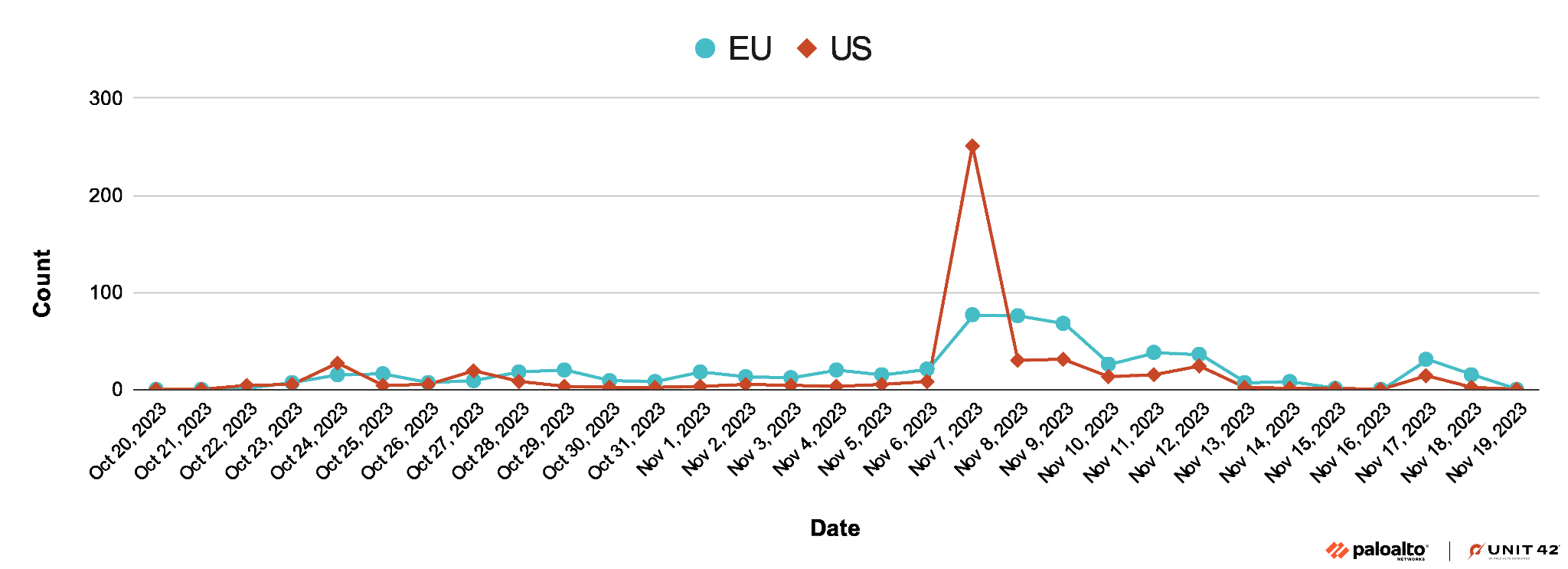 Figure 4 shows that while this recent campaign seems to target organizations in many industries, organizations in the high tech industry have been the largest target.
Figure 4 shows that while this recent campaign seems to target organizations in many industries, organizations in the high tech industry have been the largest target.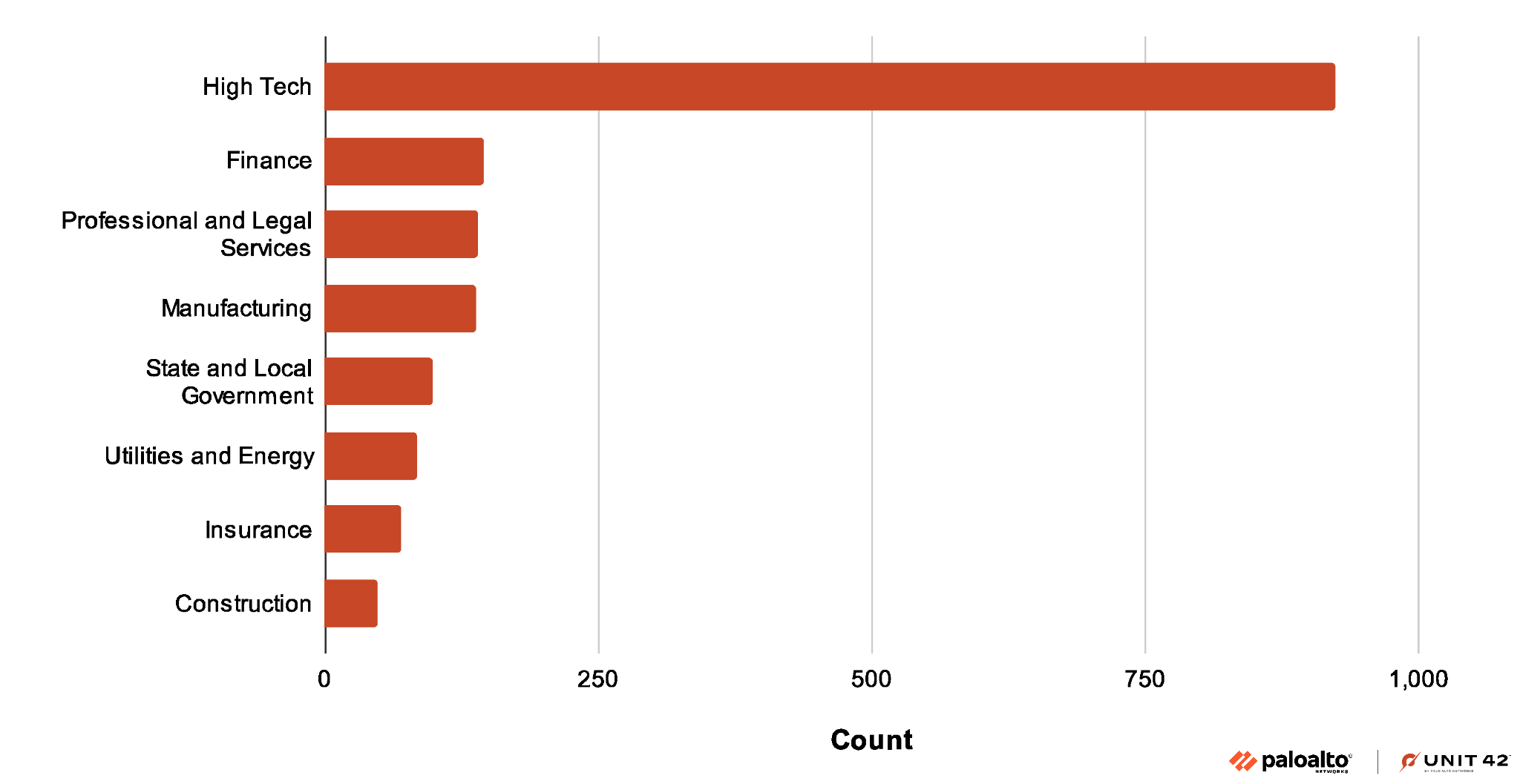
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind