Tenable security researchers found a vulnerability in Google Cloud Platform’s Cloud Functions service that could allow an attacker to access other services and sensitive data without permission. Tenable has given the vulnerability the name ConfusedFunction.
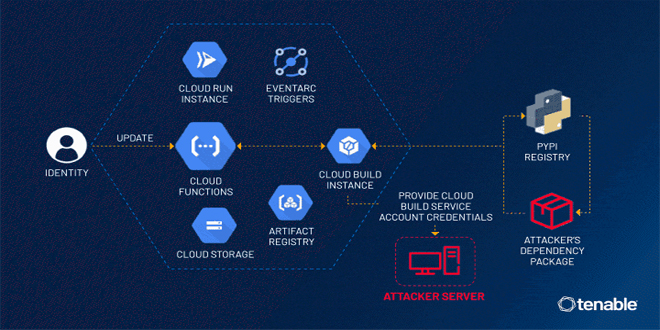
“An attacker could escalate their privileges to the Default Cloud Build Service Account and access numerous services such as Cloud Build, storage (including the source code of other functions), artifact registry and container registry,” the exposure management company said in a statement.
“This access allows for lateral movement and privilege escalation in a victim’s project, to access unauthorized data and even update or delete it.”
“Cloud Functions is a serverless platform for creating single-purpose functions triggered by specific Cloud events, eliminating the need to manage servers or update frameworks.”
Tenable found an issue related to the creation of a Cloud Build service account, which is automatically linked to a Cloud Build instance when a Cloud Function is created or updated.
This service account has too many permissions, which can lead to potential malicious activity. An attacker with access can exploit this by creating or updating a Cloud Function to gain higher privileges using this vulnerability.
The permission allows access to Google Cloud services created alongside Cloud Function, such as Cloud Storage, Artifact Registry, and Container Registry. In a potential attack, ConfusedFunction could be used to expose the Cloud Build service account token through a webhook.
Google has updated the default behavior of Cloud Build to use the Compute Engine default service account and prevent misuse. It’s important to mention that these changes only affect new instances, not existing ones.
“The ConfusedFunction vulnerability highlights the problematic scenarios that may arise due to software complexity and inter-service communication in a cloud provider’s services,” Tenable researcher Liv Matan said.
“While the GCP fix has reduced the severity of the problem for future deployments, it didn’t completely eliminate it. That’s because the deployment of a Cloud Function still triggers the creation of the aforementioned GCP services. As a result, users must still assign minimum but still relatively broad permissions to the Cloud Build service account as part of a function’s deployment.”
Outpost24 identified a medium-severity cross-site scripting (XSS) flaw in the Oracle Integration Cloud Platform that could allow for the injection of malicious code into the application.
The flaw, which is rooted in the handling of the “consumer_url” parameter, was resolved by Oracle in its Critical Patch Update (CPU) released earlier this month.
Source: thehackernews, tenable
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind