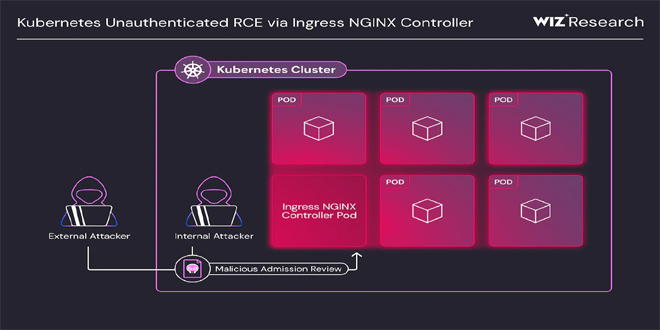
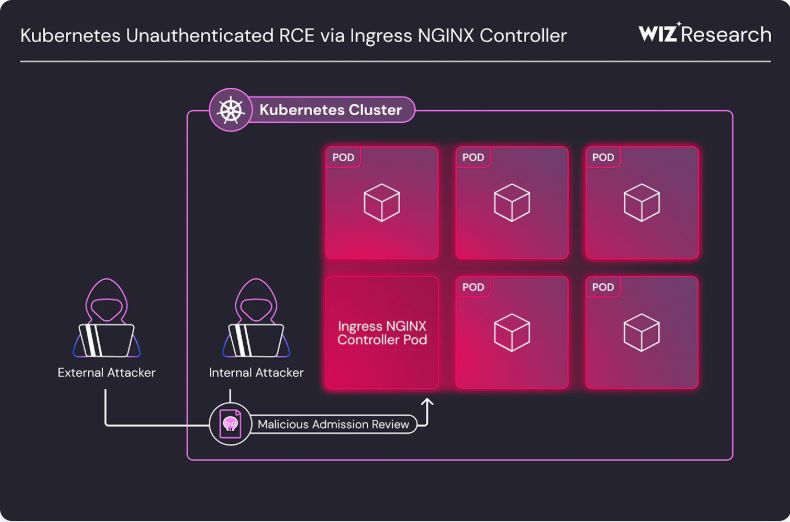
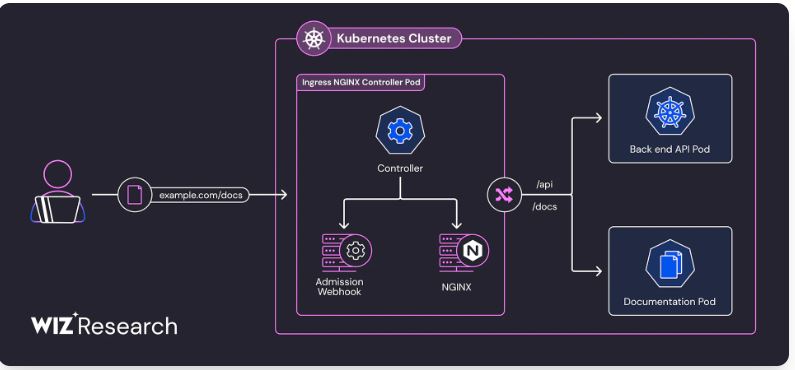
Kubernetes users of the Ingress NGINX Controller are advised to fix four newly found remote code execution ( RCE) vulnerabilities, which have a CVSS score of 9.8.
Wiz Security named four vulnerabilities “IngressNightmare” that affect the admission controller of the popular open-source software used for directing external traffic to Kubernetes services and pods.
By infosecbulletin
/ Monday , June 23 2025
A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication...
Read More
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
By infosecbulletin
/ Monday , June 16 2025
SafetyDetectives’ Cybersecurity Team discovered a public post on a clear web forum in which a threat actor claimed to have...
Read More
By infosecbulletin
/ Sunday , June 15 2025
WestJet, Canada's second-largest airline, is looking into a cyberattack that has affected some internal systems during its response to the...
Read More
By infosecbulletin
/ Saturday , June 14 2025
Resecurity found 7.4 million records of Paraguayan citizens' personal information leaked on the dark web today. Last week, cybercriminals attempted...
Read More
By infosecbulletin
/ Friday , June 13 2025
HashiCorp has revealed a critical vulnerability in its Nomad tool that may let attackers gain higher privileges by misusing the...
Read More
By infosecbulletin
/ Friday , June 13 2025
SoftBank has disclosed that personal information of more than 137,000 mobile subscribers—covering names, addresses, and phone numbers—might have been leaked...
Read More
Wiz Research claimed the flaws impact 43% of all cloud environments, including many Fortune 500 companies. Because the software’s admission controllers are typically exposed to the public internet, they are at “critical risk” of attack, it warned.
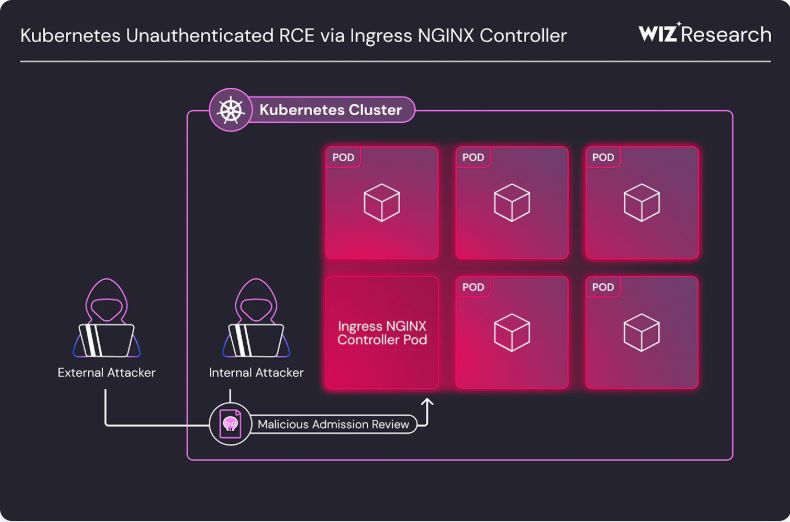
The vulnerabilities are CVE-2025-1097, CVE-2025-1098, CVE-2025-24514, and CVE-2025-1974. The first three allow an attacker to inject arbitrary NGINX configuration directives, potentially leading to remote code execution when combined with the fourth vulnerability.
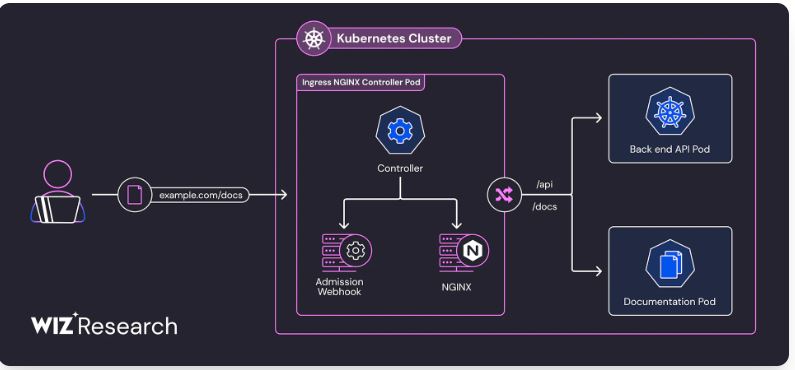
“When the Ingress-NGINX admission controller processes an incoming ingress object, it constructs an NGINX configuration from it and then validates it using the NGINX binary. Our team found a vulnerability in this phase that allows injecting an arbitrary NGINX configuration remotely, by sending a malicious ingress object directly to the admission controller through the network,” Wiz Security explained.
“During the configuration validation phase, the injected NGINX configuration causes the NGINX validator to execute code, allowing remote code execution (RCE) on the Ingress NGINX Controller’s pod.”
The admission controller has high-level permissions and full network access, so exploiting these vulnerabilities could let an attacker run any code, access all cluster secrets, and fully control a targeted cluster, it added.
Kubernetes admins should upgrade to Ingress NGINX Controller versions 1.12.1 and 1.11.5, and make sure the admission webhook endpoint is not publicly accessible.
The security vendor has provided mitigations for those unable to upgrade to patched versions right away.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind