The web development community was affected by a supply chain attack on the popular Polyfill.io JavaScript library last week. Polyfill.js supports modern tools on older web browsers for cross-compatibility.
In February 2024, the Polyfill.io domain and GitHub account were acquired by Funnull, a Chinese CDN company. This raised concerns about the service’s legitimacy. Malware injected through cdn.polyfill.io has been redirecting users to malicious sites, affecting over 100,000 websites, including high-profile platforms like JSTOR, Intuit, and the World Economic Forum. The malware is sophisticated and hard to detect and combat, using different evasion techniques.
Several companies have reacted to this situation. Cloudflare and Fastly provided secure alternative endpoints for users. Google stopped displaying ads for e-commerce sites using Polyfill.io. The uBlock Origin website blocker added the domain to its filter list. Andrew Betts, the creator of Polyfill.io, advised website owners to remove the library as it is no longer needed for modern browsers.
On June 27, Namecheap, the domain registrar for polyfill.io, took down the harmful domain, which reduces the immediate threat.
Latest report indicates, Censys has identified a significant number of web hosts using the polyfill.io CDN. As of the latest data, 384,773 hosts were found to include references to “https://cdn.polyfill[.]io” or “https://cdn.polyfill[.]com” in their HTTP responses.
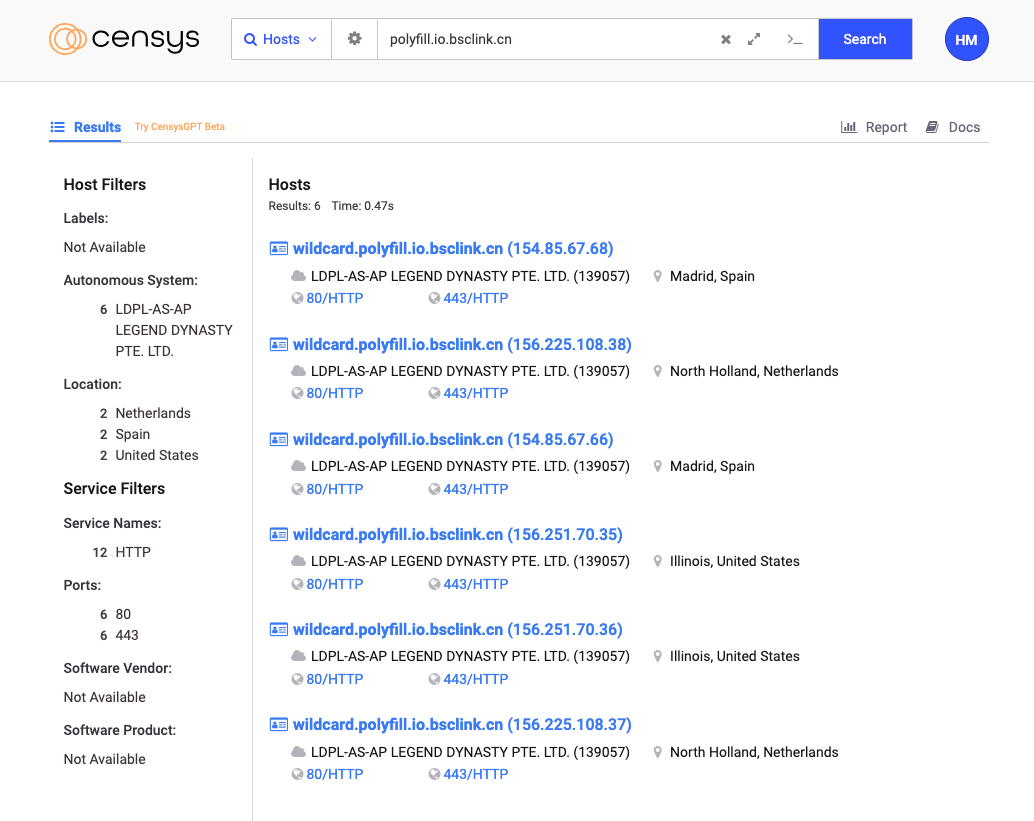
A notable concentration of these hosts, approximately 237,700, are located within the Hetzner network (AS24940), primarily in Germany. This is not surprising – Hetzner is a popular web hosting service, and many website developers leverage it.
Domains tied to major companies like Warner Bros, Hulu, Mercedes-Benz, and Pearson have many hosts referring to a malicious polyfill endpoint. The most common hostname associated with hosts presenting the endpoint is ns-static-assets.s3.amazonaws.com, which suggests widespread usage among Amazon S3 static website hosting users.
The website “www.feedthefuture.gov” appears in these top results. This shows that polyfill.io is used in many sectors, including government websites. Censys found 182 affected hosts with a “.gov” domain.
View the following report breaking down hostnames on sites using this endpoint.
Estimates of affected websites vary widely, but it’s clear that this supply chain attack has had a widespread impact. Sansec reported 100,000 affected websites, while Cloudflare suggested “tens of millions”.
Cloudflare and Fastly made new secure options to help users stay safe without breaking websites. Censys found 216,504 hosts using these new options, up from 80,312 last Friday, June 28th.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind