Zimperium researchers have found a new version of FakeCall malware for Android that threatens financial security. This malware redirects users’ calls to their banks to the attacker’s phone number, aiming to steal sensitive information and funds.
FakeCall is a banking trojan used for voice phishing, misleading victims into giving sensitive information through fake calls that mimic banks.
The new version has enhanced evasion techniques and data theft abilities, mainly aimed at South Korean users.
Earlier versions of FakeCall deceived users into contacting scammers by displaying a fake bank screen with a real bank number. The latest version sets itself as the default call handler, gaining control over all outgoing calls.
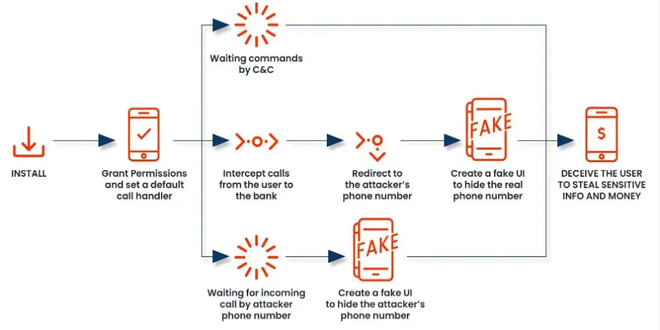
The latest Zimperium report reveals that a malicious app prompts users to make it the default call handler during installation through an Android APK.
The Android call handler manages incoming and outgoing calls, allowing users to dial, connect, and end calls. The malware prompts the user to set it as the default call handler, allowing it to intercept and control incoming and outgoing calls.
It has a fake call interface that looks like a real Android dialer, showing trusted contact names and details, making it hard for victims to realize it’s a deception.
This malware is dangerous because it can secretly redirect calls to financial institutions to the attacker’s phone number.
“When the compromised individual attempts to contact their financial institution, the malware redirects the call to a fraudulent number controlled by the attacker,” explains the new Zimperium report.
“The malicious app will deceive the user, displaying a convincing fake UI that appears to be the legitimate Android’s call interface showing the real bank’s phone number.”
The victim won’t realize they’re being manipulated because the malware’s fake interface looks like a real banking site. This lets the attacker steal sensitive information or access the victim’s financial accounts without permission.
“This receiver functions primarily as a listener, monitoring Bluetooth status and changes. Notably, there is no immediate evidence of malicious behavior in the source code, raising questions about whether it serves as a placeholder for future functionality.” reads the report.
Zimperium has released a list of indicators of compromise (IoC) for the latest malware version.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind