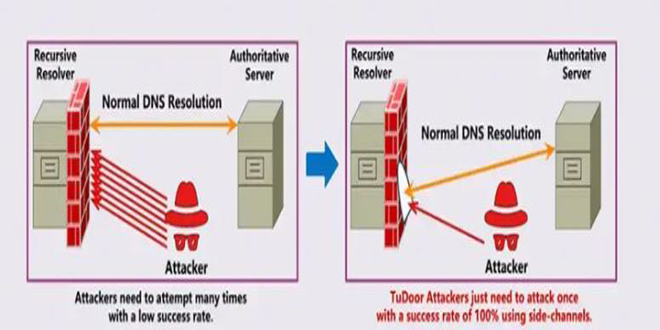
A new critical vulnerability in the Domain Name System (DNS) has been found. This vulnerability allows a specialized attack called “TuDoor” that can poison DNS caches, cause denial-of-service (DoS) attacks, and deplete resources, posing a significant threat to internet security.
Specialists have conducted experiments that confirm the feasibility of the TuDoor attack, revealing its serious implications in real-world scenarios. A striking total of 24 widely used DNS programs, including BIND, PowerDNS, and Microsoft DNS, have been found vulnerable to TuDoor. In less than a single second, attackers can execute cache poisoning or DoS attacks against these vulnerable resolvers using just a handful of precisely fabricated packets.
By F2
/ Tuesday , June 24 2025
The U.S. House of Representatives has banned congressional staff from using WhatsApp on government devices due to security concerns, as...
Read More
By F2
/ Tuesday , June 24 2025
Kaspersky found a new mobile malware dubbed SparkKitty in Google Play and Apple App Store apps, targeting Android and iOS....
Read More
By F2
/ Tuesday , June 24 2025
OWASP has released its AI Testing Guide, a framework to help organizations find and fix vulnerabilities specific to AI systems....
Read More
By F2
/ Tuesday , June 24 2025
In a major milestone for the country’s digital infrastructure, Axentec PLC has officially launched Axentec Cloud, Bangladesh’s first Tier-4 cloud...
Read More
By infosecbulletin
/ Monday , June 23 2025
A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication...
Read More
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
By infosecbulletin
/ Monday , June 16 2025
SafetyDetectives’ Cybersecurity Team discovered a public post on a clear web forum in which a threat actor claimed to have...
Read More
Researchers tested 16 Wi-Fi router models, 6 operating systems, 42 DNS services, and about 1.8 million open DNS resolvers. The study found that TuDoor could exploit 7 routers, 18 DNS services, and 424,652 open DNS resolvers.
The researchers followed best practices for responsible disclosure by informing all affected vendors of the vulnerabilities. 18 vendors, such as BIND, Chrome, Cloudflare, and Microsoft, confirmed the findings and discussed ways to fix the issues. 33 CVE identifiers were assigned to the vulnerabilities, and an online tool for their detection was suggested.
Collaboration among researchers, developers, and users is crucial to ensure a secure digital environment. We need constant vigilance to address new vulnerabilities like TuDoor. By working together, we can achieve innovation and protection simultaneously.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind