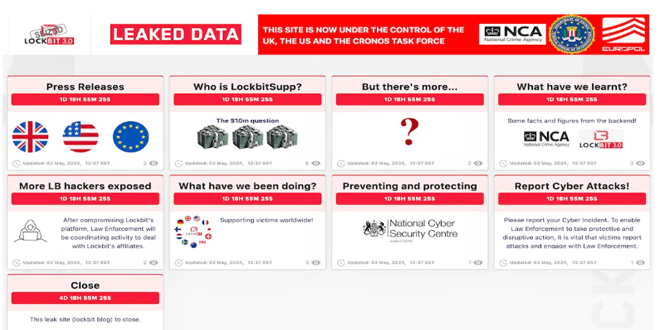
New information about the Lockbit ransomware gang might be coming soon. The gang’s old dark web leak site was taken down by law enforcement in February, but it has now reappeared, hinting at the release of new information in a few days.
Several parts of the site were updated on May 2, all promising more information to be dropped on May 7, including an answer to the “$10m question – who is LockbitSupp”. LockbutSupp is the gang’s apparent leader, and the law enforcement agencies involved in the site takedown have already suggested the individual is based in Russia, and had “engaged with law enforcement”.
By infosecbulletin
/ Saturday , July 27 2024
India’s Communications Minister Chandra Sekhar Pemmasani confirmed a breach at the state-owned telecom operator BSNL on May 20 during a...
Read More
By infosecbulletin
/ Saturday , July 27 2024
Malware based threats increased by 30% in the first half of 2024 compared to the same period in 2023, according...
Read More
By infosecbulletin
/ Friday , July 26 2024
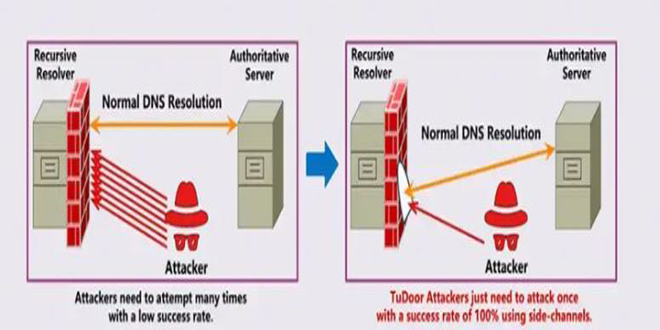
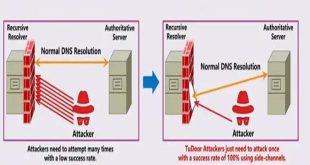
A new critical vulnerability in the Domain Name System (DNS) has been found. This vulnerability allows a specialized attack called...
Read More
By infosecbulletin
/ Friday , July 26 2024
A serious vulnerability, CVE-2023-45249 (CVSS 9.8), has been found in Acronis Cyber Infrastructure (ACI), a widely used software-defined infrastructure solution...
Read More
By infosecbulletin
/ Friday , July 26 2024
OpenAI is testing a new search engine "SearchGPT" using generative artificial intelligence to challenge Google's dominance in the online search...
Read More
By infosecbulletin
/ Thursday , July 25 2024
CISA released two advisories about security issues for Industrial Control Systems (ICS) on July 25, 2024. These advisories offer important...
Read More
By infosecbulletin
/ Thursday , July 25 2024
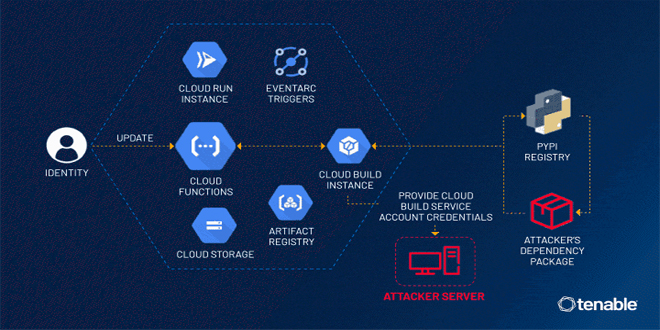
Tenable security researchers found a vulnerability in Google Cloud Platform's Cloud Functions service that could allow an attacker to access...
Read More
By infosecbulletin
/ Thursday , July 25 2024
BDG e-GOV CIRT's Cyber Threat Intelligence Unit has noticed a concerning increase in cyber-attacks against web applications and database servers...
Read More
By infosecbulletin
/ Thursday , July 25 2024
GitLab released a security update today to fix six vulnerabilities in its software. Although none of the flaws are critical,...
Read More
By infosecbulletin
/ Thursday , July 25 2024
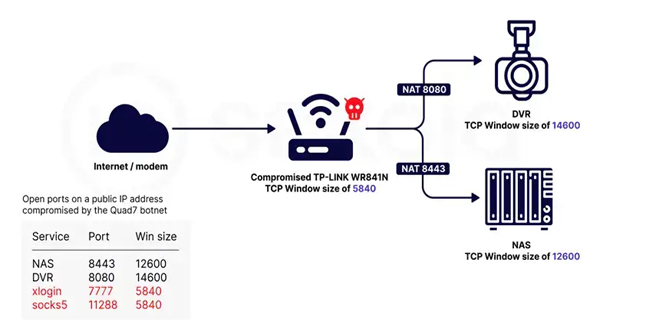
Sekoia.io and Intrinsec analyzed the Quad7 (7777) botnet, which uses TCP port 7777 on infected routers to carry out brute-force...
Read More
NCA will reveal information about Lockbit’s partners and share details from the gang’s backend systems soon. The seized site reveals more LB hackers.
“What have we learnt?” says another. “Some facts and figures from the backend.” And, again a date of May 7 is given for when these details will be shared.
Prior to that In February, the U.K. National Crime Agency (NCA) confirmed that it got LockBit’s source code and gathered intelligence about its activities and affiliates as part of Operation Cronos.
“Some of the data on LockBit’s systems belonged to victims who had paid a ransom to the threat actors, evidencing that even when a ransom is paid, it does not guarantee that data will be deleted, despite what the criminals have promised,” the agency said that time.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind