It has come to the attention of researchers that the LockBit 3.0 builder has suffered from a leak, which now allows anyone to create various versions of the LockBit ransomware according to their own preferences. This poses a serious security risk that should not be taken lightly.
LockBit” is a ransomware-as-a-service (RaaS) group that has been active since September 2019. LockBit has developed several variants: LockBit 1.0, LockBit 2.0, LockBit 3.0, and LockBit Green.
Lockbit 3, also known as Lockbit Black, was detected for the first time in 2019. Due to its complex architecture and encryption methods, it evades traditional scan engines.
Securelist’s investigation team, GERT, detected the intrusion attempt of the Lockbit 3 variant and shared the detailed report on their blog.
What is New in LockBit 3?
Lockbit Black is a highly complex ransomware variant with undocumented kernel-level Windows functions and strong protection against reverse engineering.
Many security experts confirmed the leakage of a builder for LockBit 3.0 in September 2022, and various groups started to abuse the builder.
Kaspersky’s protection system detected the lockbit threat as “Trojan.Win32.Inject.aokvy”.The techniques and intrusion attempts are identical to those of other ransomware groups listed by Kaspersky.
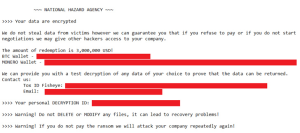
However, the ransom demand procedure was significantly different from the one that this threat actor was known to use. The attacker used a different ransom note with a title from the National Hazard Agency, a previously unknown group.
“The ransom note used in this case directly described the amount to be paid to obtain the keys and directed communications to a Tox service and email, unlike the Lockbit group, which uses its own communication and negotiation platform.”
Many other threat groups started abusing exfiltrated builders to create their own ransomware notes and communications channels.
Kaspersky’s telemetry found 396 LockBit samples, 312 of which were generated using the leaked builder, and Ransom notes in 77 pieces that didn’t mention “LockBit.”
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














