The cyber threat landscape is rapidly changing, with a notable increase in ransomware activity in …
Read More »CVE-2024-55591 and CVE-2025-24472
New SuperBlack ransomware exploits Fortinet flaws
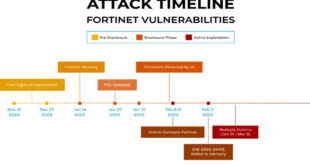
Forescout Research- Vedere Labs identified a series of intrusion based on two Fortinet vulnerabilities which began with the exploitation of FortiGate firewall appliance dubbed SuperBlack. Researchers track this between late january and early March. Fortinet disclosed two authentication bypass vulnerabilities: CVE-2024-55591 in January and CVE-2025-24472 in February. When Fortinet first …
Read More » InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind