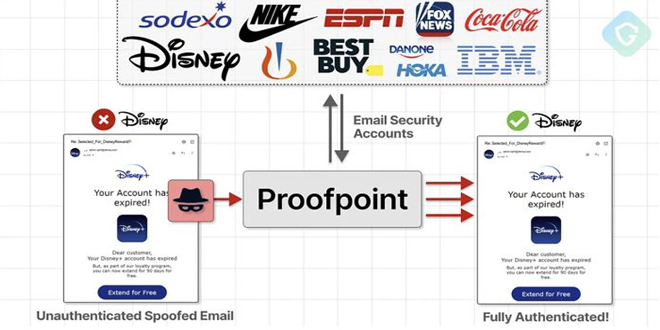
A scam campaign linked to an unknown threat actor is using an email routing misconfiguration in Proofpoint’s defenses to send millions of fake emails pretending to be from companies like Best Buy, IBM, Nike, and Walt Disney. Guardio Labs named the campaign EchoSpoofing.
It started in January 2024. The threat actor took advantage of a loophole and sent around three million emails per day on average. In early June, the number of emails reached a peak of 14 million as the company Proofpoint started to take action against it.
By F2
/ Tuesday , June 24 2025
The U.S. House of Representatives has banned congressional staff from using WhatsApp on government devices due to security concerns, as...
Read More
By F2
/ Tuesday , June 24 2025
Kaspersky found a new mobile malware dubbed SparkKitty in Google Play and Apple App Store apps, targeting Android and iOS....
Read More
By F2
/ Tuesday , June 24 2025
OWASP has released its AI Testing Guide, a framework to help organizations find and fix vulnerabilities specific to AI systems....
Read More
By F2
/ Tuesday , June 24 2025
In a major milestone for the country’s digital infrastructure, Axentec PLC has officially launched Axentec Cloud, Bangladesh’s first Tier-4 cloud...
Read More
By infosecbulletin
/ Monday , June 23 2025
A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication...
Read More
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
By infosecbulletin
/ Monday , June 16 2025
SafetyDetectives’ Cybersecurity Team discovered a public post on a clear web forum in which a threat actor claimed to have...
Read More
The Hacker News reported “These emails echoed from official Proofpoint email relays with authenticated SPF and DKIM signatures, thus bypassing major security protections — all to deceive recipients and steal funds and credit card details,”.
“The most unique and powerful part of this domain is the spoofing method – leaving almost no chance to realize this is not a genuine email sent from those companies,” Guardio Labs researcher Nati Tal told.
“This EchoSpoofing concept is really powerful. It’s kind of strange it is being used for large-scale phishing like this instead of a boutique spear-phishing campaign – where an attacker can swiftly take any real company team member’s identity and send emails to other co-workers – eventually, through high-quality social engineering, get access to internal data or credentials and even compromise the entire company.
The technique utilizes an SMTP server on a virtual private server (VPS) to send messages, ensuring compliance with authentication and security measures like SPF and DKIM. Click here to read the full report.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind