DragonForce ransomware targets organizations in Saudi Arabia. An attack on a major Riyadh real estate and construction firm led to the theft of more than 6TB of sensitive data.
Resecurity’s new advisory reports that threat actors announced a breach on February 14, 2025, demanding ransom before releasing stolen information. The deadline for payment was given as February 27, just before Ramadan.
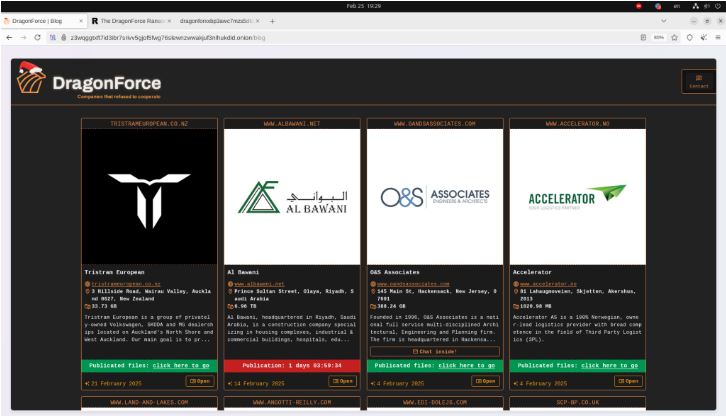
After the ransom deadline passed, DragonForce released the stolen data on a separate leak site.
The ransomware group uses a Ransomware-as-a-Service (RaaS) model to expand its affiliate network, offering tools to cybercriminals for a share of ransom payments. Its DLS includes advanced CAPTCHA systems to hinder automated tracking by cybersecurity firms.
DragonForce has been active since December 2023, starting with the Heart of Texas Region MHMR Center as its first target. The group has since improved its methods, using advanced encryption, TOR for communication, and secure payment options like Bitcoin and private chat systems.
Ransom Payment Collection and Affiliate Network:
They recruit partners on the RAMP underground forum and offer some of the best commission rates in the cybercrime market—up to 80% of ransom proceeds.
Affiliates use TOR-based instant messaging (TOX) and must show they can access victim networks. To improve security, DragonForce has strengthened its vetting process following a previous leak of affiliate URLs.
Tools, Tactics and Exploited Vulnerabilities:
DragonForce uses phishing and exploits weaknesses in RDP and VPN to gain access.
The group uses dual extortion tactics by encrypting victim data and threatening to publish stolen information if ransoms aren’t paid. DragonForce has also released audio recordings of ransom negotiations to pressure victims.
“The combination of wealthy targets, cybersecurity gaps and geopolitical factors make the Middle East an attractive region for ransomware groups to exploit, making these attacks more profitable,” Resecurity wrote.
“The DragonForce ransomware targeting KSA and the associated data leak from the recent victim in KSA underscore the urgent need for enhanced cybersecurity measures to protect vital national assets and sensitive information.”
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














