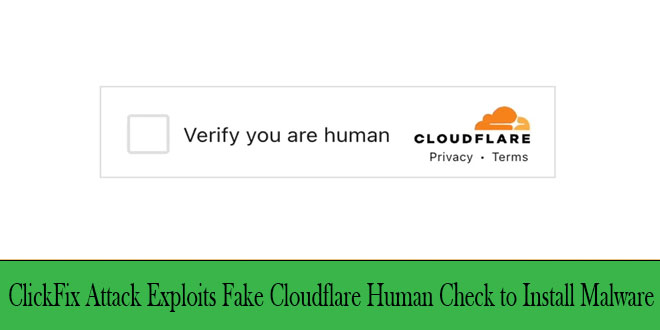
A new social engineering attack uses familiar security checks to trick users into downloading malware via fake Cloudflare verification pages.
The ClickFix attack technique marks a worrying shift in phishing methods, moving away from traditional file downloads to tricking users into running harmful commands on their own devices.
By infosecbulletin
/ Wednesday , September 17 2025
A threat actor claims to have breached Link3, a major IT solutions and internet service provider based in Bangladesh. The...
Read More
By infosecbulletin
/ Wednesday , September 17 2025
Check point, a cyber security solutions provider hosts an event titled "securing the hyperconnected world in the AI era" at...
Read More
By infosecbulletin
/ Tuesday , September 16 2025
Cross-Site Scripting (XSS) is one of the oldest and most persistent vulnerabilities in modern applications. Despite being recognized for over...
Read More
By infosecbulletin
/ Monday , September 15 2025
Every day a lot of cyberattack happen around the world including ransomware, Malware attack, data breaches, website defacement and so...
Read More
By infosecbulletin
/ Monday , September 15 2025
A critical permission misconfiguration in the IBM QRadar Security Information and Event Management (SIEM) platform could allow local privileged users...
Read More
By infosecbulletin
/ Monday , September 15 2025
Australian banks are now using bots to combat scammers. These bots mimic potential victims to gather real-time information and drain...
Read More
By infosecbulletin
/ Saturday , September 13 2025
F5 plans to acquire CalypsoAI, which offers adaptive AI security solutions. CalypsoAI's technology will be added to F5's Application Delivery...
Read More
By infosecbulletin
/ Saturday , September 13 2025
The Villager framework, an AI-powered penetration testing tool, integrates Kali Linux tools with DeepSeek AI to automate cyber attack processes....
Read More
By infosecbulletin
/ Saturday , September 13 2025
Samsung released its monthly Android security updates, addressing a vulnerability exploited in zero-day attacks. CVE-2025-21043 (CVSS score: 8.8) is a...
Read More
By infosecbulletin
/ Saturday , September 13 2025
Albania has appointed the first AI-generated government minister to help eliminate corruption. Diella, the digital assistant meaning Sun, has been...
Read More
The attack uses a fake Cloudflare Turnstile interface that looks real, featuring official branding, genuine wording, and dynamic Ray IDs to deceive victims.
Users often encounter fake verification pages displaying familiar messages like “Checking if the site connection is secure – Verify you are human,” which resemble real Cloudflare protection. This mimicry takes advantage of verification fatigue, where users quickly click through security prompts without careful scrutiny.
SlashNext researchers have identified a new threat that uses a clever method to evade traditional security measures.
The technique is very effective because it relies on user trust in established security providers and doesn’t need complex exploits or zero-day vulnerabilities.
The attack tricks users into running harmful code by pretending to be a normal verification process.
The campaign has been seen spreading different types of malware, including information stealers like Lumma and Stealc, and remote access trojans like NetSupport Manager.
The attack succeeds by using legitimate system tools with harmful parameters, allowing it to bypass traditional security filters instead of relying on suspicious downloads.
This method bypasses many endpoint protection tools that scan downloaded files. To read the full report click here.
Fortinet flaws now exploited in Qilin ransomware attacks
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind