In the advent of Eid ul-Adha holidays, Bangladesh Government’s Computer Incident Response Team (BGD e-GOV CIRT) would like to ensure the security of the critical information infrastructures (CII), banks and financial institutions, health care and all sorts of government and private organizations by sharing a list of top threats to be vigilant for any suspicious activities in their infrastructure to prevent any sort of intrusion or disruption to their IT operations and services.
CERT said on a situational alart on 26 june monday that, We bring your kind attention to combat cyber threats during EID vacation focused with the below mentioned threat considerations:
- Top targeted Organization Type:
- Govt & Military
- Law Enforcement Agencies
- Banking and NBFI
- Pharmaceuticals
- Retail and Industrial Organizations
- Energy and education sectors
Top detected attack types:
-
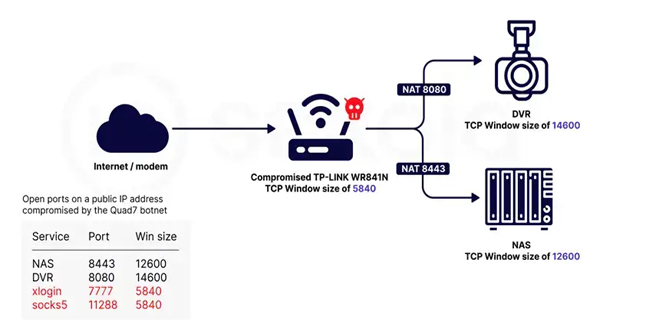
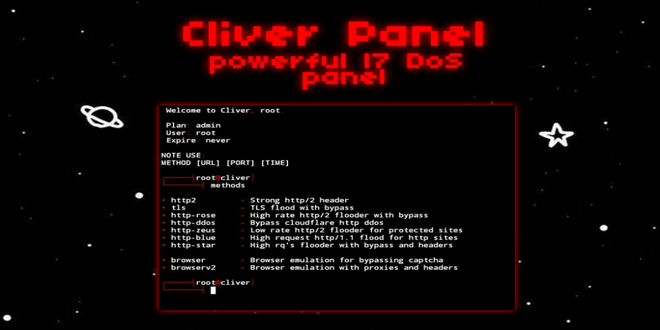
- DDOS – Being the most observed attack type in Bangladesh cyberspace
- Ransomware – Bangladesh witnessed a rise in ransomware incidents in 2nd quarter of 2023
- Web Defacements – using web shell injection technique
- Phishing – Observed sophisticated phishing campaigns using AI tools
- Credential theft – ‘Redline stealer’ is the most found stealer in targeted entities
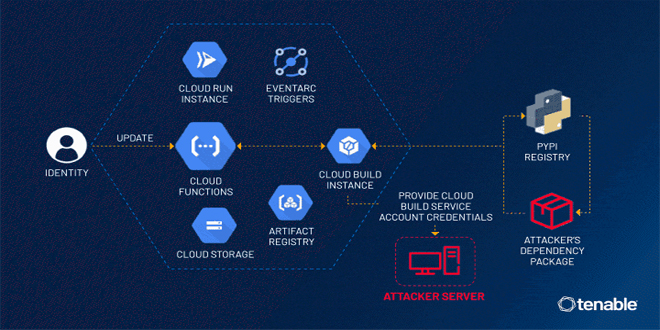
- APT campaigns – emerging groups are launching campaigns actively
- Top Threat Actors
- South Asian based underground hackers
- Script kiddies with credential harvesting expertise
- Ransomware and APT Threat Actors such as ‘Money Message’ and ‘Akira’
All government, military and financial institutions are requested to take the following measures to ensure their infrastructures’ security:
- Ensure strict network and user activity monitoring 24/7, especially during non-office hours, and watch out for any indication of data exfiltration, any sort of repeated patterns that may indicate attempts of lateral movement, discovery, or command and control behavior.
- Mobile users should be cautious while browsing internet and refrain from accessing untrusted sites or downloading files from it.
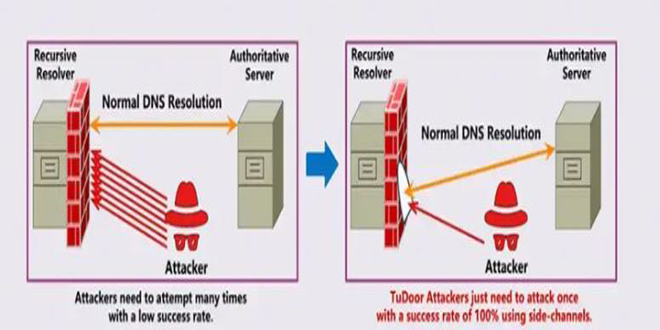
- Ensure vital services as such DNS, NTP as well as network middleboxes are securely configured and are not exposed on the internet.
- Educate users to abide by password policy best practices, and to refrain from using corporate emails on other platforms.
- Ensure proper Information and Cyber Security awareness training among all the employees, customers, and consumers to report issues, if they observe any anomalies and/ or suspicious activities.
- Conduct Vulnerability Assessment and Penetration Testing (VAPT) for all the systems on regular basis.
- Ensure appropriate controls and minimize attack surface by assessing need-to-know basis.
- Enhance your capability to combat growing cyber threats.
- Configure and harden web application as per OWASP guideline
(https://onwasp.onrg/www-pronject-web-security-testing-guide/v41/)
- Report or inform BGD e-GOV CIRT regarding the detection of IOCs and/ or any suspicious activities you observe within your environment, to work in collaboration through https://www.cirt.gov.bd/incident-reporting/ or [email protected]
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind