A recent report from Elastic reveals that threat actors misuse Amazon Web Services (AWS) Simple Notification Service (SNS) for malicious activities like data exfiltration and phishing. The research highlights potential abuse methods and ways to detect them.
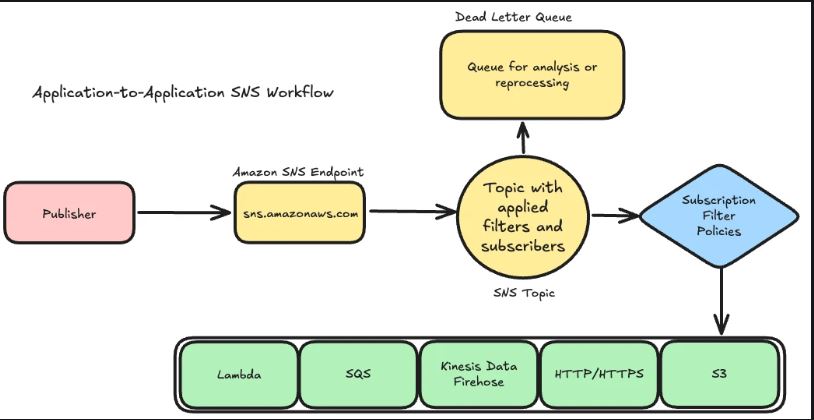
AWS SNS is a web service that enables users to send and receive notifications from the cloud. “This research was the result of a recent internal collaboration that required us to leverage SNS for data exfiltration during a whitebox exercise. During this collaboration, we became intrigued by how a simple publication and subscription (pub/sub) service could be abused by adversaries to achieve various actions on objectives,” the report states.
The report explains how adversaries can exploit SNS for data theft by creating an SNS topic to receive stolen information. They can subscribe an external source, like email, to this topic. Once data is sent to the SNS topic, it is automatically distributed to the subscribed source.
The report provides an example workflow:
An attacker gains access to an EC2 instance and discovers sensitive data.
They leverage IMDSv2 and STS with the AWS CLI to obtain temporary credentials.
The attacker creates a topic in SNS and attaches an external email address as a subscriber.
Sensitive information is published to the topic, often encoded in Base64.
The external email address receives the exfiltrated data.
The report explains that compromised AWS environments with pre-configured SNS services can be used for smishing (SMS phishing) and phishing attacks. Attackers can exploit legitimate SNS topics and subscribers to send fraudulent messages internally and externally.
The report discusses a tool called SNS Sender that adversaries use for mass SMS phishing. It allows them to send bulk phishing messages by connecting to AWS SNS APIs with stolen AWS credentials. By using valid access keys, attackers can bypass security measures and send messages undetected.
The report outlines the challenges adversaries encounter, including initial access, session establishment, and needing proper IAM role permissions. It also highlights their advantages, like blending in with AWS services, impersonating identities through IAM roles, evading egress monitoring, and the absence of specific detection for SNS abuse.
“By leveraging AWS SNS for data exfiltration, the adversary’s activity appears as legitimate usage of a native AWS flagship service,” the report states.
The report stresses the need to recognize potential abuses of cloud services like SNS and offers detection strategies. It also underscores the importance of security best practices, such as improving roles and access, to reduce these threats.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














