Avast researchers found a security flaw in the DoNex ransomware and its previous versions, which allowed them to create a tool to decrypt the files. They shared this discovery at the Recon 2024 conference. Avast released a free decryptor in March 2024 to help victims recover their files.
“All brands of the DoNex ransomware are supported by the decryptor.” reads the announcement. “DoNex uses targeted attacks on its victims and it was most active in the US, Italy, and Belgium based on our telemetry.”
By infosecbulletin
/ Tuesday , October 22 2024
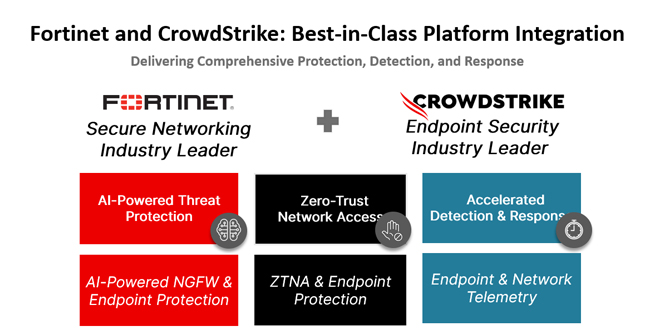
In today's rapidly changing cybersecurity environment, organizations encounter numerous complex threats targeting endpoints and networks. CrowdStrike and Fortinet have partnered...
Read More
By infosecbulletin
/ Tuesday , October 22 2024
Sophos, based in the UK, is to acquire Secureworks, a Nasdaq-listed company, for $859 million in cash from Dell Technologies....
Read More
By infosecbulletin
/ Monday , October 21 2024
The Internet Archive was breached again, this time through their Zendesk email support platform, following warnings that threat actors had...
Read More
By infosecbulletin
/ Sunday , October 20 2024
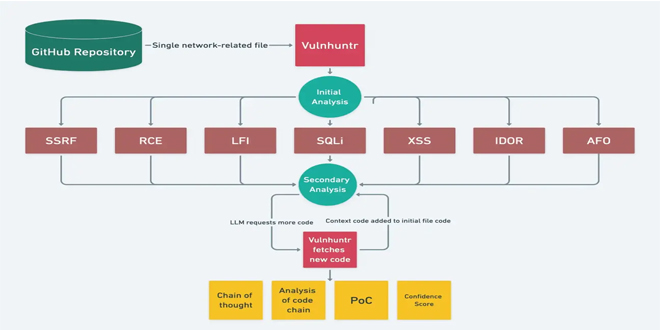
In today's changing cybersecurity environment, it's essential to find vulnerabilities in code. Vulnhuntr, an open-source tool on GitHub, uses Large...
Read More
By infosecbulletin
/ Friday , October 18 2024
Bitdefender said a vulnerability has been identified in Bitdefender Total Security HTTPS scanning functionality where the software fails to properly...
Read More
By infosecbulletin
/ Thursday , October 17 2024
Cybersecurity threats have surged to extraordinary heights, as Microsoft’s latest Digital Defense Report reveals that its customers are confronted with...
Read More
By infosecbulletin
/ Thursday , October 17 2024
VMware has issued a warning about a remote code execution vulnerability, CVE-2024-38814, with a CVSS score of 8.8, in its...
Read More
By infosecbulletin
/ Thursday , October 17 2024
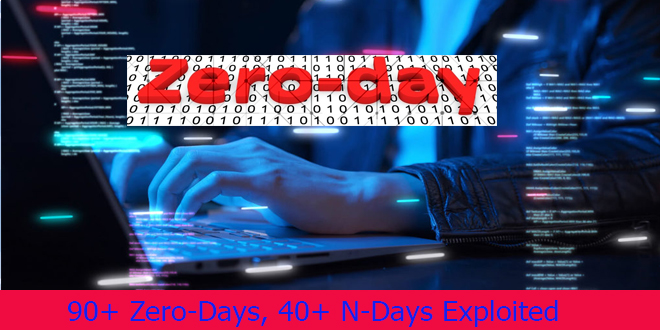
Mandiant researchers found that over 90 zero-day vulnerabilities and more than 40 known vulnerabilities were exploited in the wild. Vulnerabilities...
Read More
By infosecbulletin
/ Wednesday , October 16 2024
Oracle's October 2024 Critical Patch Update has fixed 334 security vulnerabilities in its products. The CPU affects 28 Oracle product...
Read More
By infosecbulletin
/ Wednesday , October 16 2024
Google has released Chrome 130, fixing 17 security vulnerabilities. The update (version 130.0.6723.58/.59 for Windows and Mac, and 130.0.6723.58 for...
Read More
The company has been working with the police to secretly give victims a tool to unlock their data and prevent the ransomware author from learning how it was created.
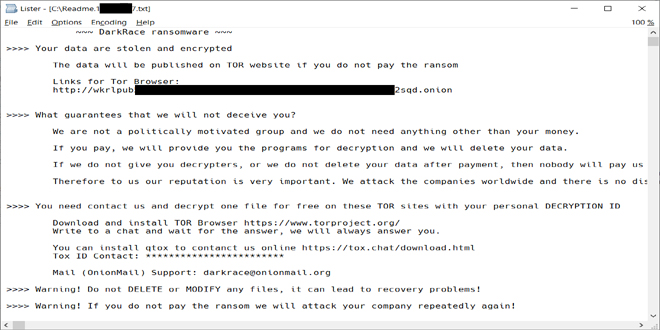
DoNex is a new version of Muse and DarkRace ransomware. It was first seen in April 2022.
When running, CryptGenRandom() creates an encryption key. The harmful code then uses the key to start the ChaCha20 symmetric key and encrypt files. After encrypting a file, the symmetric file key is encrypted with RSA-4096 and added to the end of the file. Files are chosen by their extension, and the extensions are listed in the ransomware XML config.
The ransomware encrypts small files completely. For files larger than 1MB, it uses intermittent encryption by splitting the files into separate blocks that are encrypted individually.
DoNex ransomware and its previous versions have XOR-encrypted configurations that include settings for whitelisted extensions, files, services to kill, and other encryption-related data.
The researchers suggest using the 64-bit version for better performance, as it requires a lot of memory for the password-cracking process. Experts advise making a backup of encrypted files before using the decryption tool, in case something goes wrong. The researchers also provided Indicators of Compromise (IOCs) for this threat.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind