Avast researchers found a security flaw in the DoNex ransomware and its previous versions, which allowed them to create a tool to decrypt the files. They shared this discovery at the Recon 2024 conference. Avast released a free decryptor in March 2024 to help victims recover their files.
“All brands of the DoNex ransomware are supported by the decryptor.” reads the announcement. “DoNex uses targeted attacks on its victims and it was most active in the US, Italy, and Belgium based on our telemetry.”
By infosecbulletin
/ Wednesday , September 17 2025
A threat actor claims to have breached Link3, a major IT solutions and internet service provider based in Bangladesh. The...
Read More
By infosecbulletin
/ Wednesday , September 17 2025
Check point, a cyber security solutions provider hosts an event titled "securing the hyperconnected world in the AI era" at...
Read More
By infosecbulletin
/ Tuesday , September 16 2025
Cross-Site Scripting (XSS) is one of the oldest and most persistent vulnerabilities in modern applications. Despite being recognized for over...
Read More
By infosecbulletin
/ Monday , September 15 2025
Every day a lot of cyberattack happen around the world including ransomware, Malware attack, data breaches, website defacement and so...
Read More
By infosecbulletin
/ Monday , September 15 2025
A critical permission misconfiguration in the IBM QRadar Security Information and Event Management (SIEM) platform could allow local privileged users...
Read More
By infosecbulletin
/ Monday , September 15 2025
Australian banks are now using bots to combat scammers. These bots mimic potential victims to gather real-time information and drain...
Read More
By infosecbulletin
/ Saturday , September 13 2025
F5 plans to acquire CalypsoAI, which offers adaptive AI security solutions. CalypsoAI's technology will be added to F5's Application Delivery...
Read More
By infosecbulletin
/ Saturday , September 13 2025
The Villager framework, an AI-powered penetration testing tool, integrates Kali Linux tools with DeepSeek AI to automate cyber attack processes....
Read More
By infosecbulletin
/ Saturday , September 13 2025
Samsung released its monthly Android security updates, addressing a vulnerability exploited in zero-day attacks. CVE-2025-21043 (CVSS score: 8.8) is a...
Read More
By infosecbulletin
/ Saturday , September 13 2025
Albania has appointed the first AI-generated government minister to help eliminate corruption. Diella, the digital assistant meaning Sun, has been...
Read More
The company has been working with the police to secretly give victims a tool to unlock their data and prevent the ransomware author from learning how it was created.
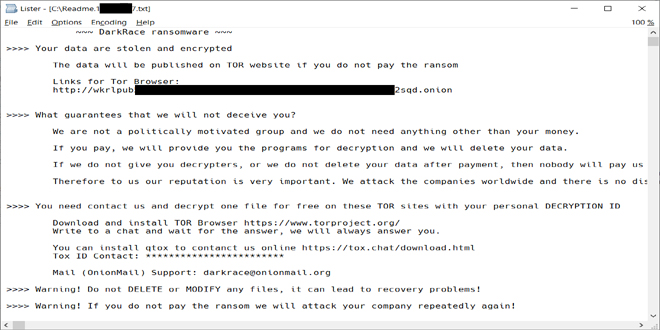
DoNex is a new version of Muse and DarkRace ransomware. It was first seen in April 2022.
When running, CryptGenRandom() creates an encryption key. The harmful code then uses the key to start the ChaCha20 symmetric key and encrypt files. After encrypting a file, the symmetric file key is encrypted with RSA-4096 and added to the end of the file. Files are chosen by their extension, and the extensions are listed in the ransomware XML config.
The ransomware encrypts small files completely. For files larger than 1MB, it uses intermittent encryption by splitting the files into separate blocks that are encrypted individually.
DoNex ransomware and its previous versions have XOR-encrypted configurations that include settings for whitelisted extensions, files, services to kill, and other encryption-related data.
The researchers suggest using the 64-bit version for better performance, as it requires a lot of memory for the password-cracking process. Experts advise making a backup of encrypted files before using the decryption tool, in case something goes wrong. The researchers also provided Indicators of Compromise (IOCs) for this threat.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind