In a sophisticated phishing campaign, uncovered cybercriminals are exploiting CrowdStrike’s recruitment branding to target developers and deploy the XMRig cryptominer.
This scam uses fake job offers to trick victims into downloading harmful software disguised as an “employee CRM application.”
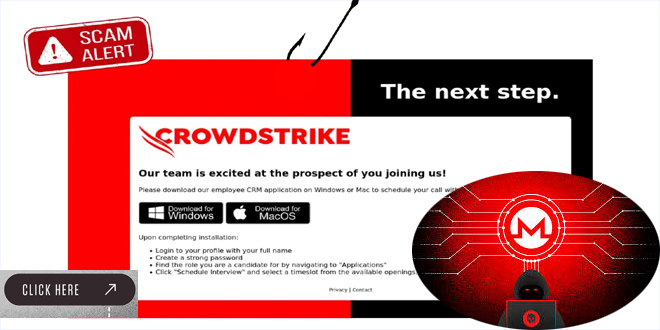
The attack starts with a phishing email pretending to be from CrowdStrike’s recruitment process. Recipients are sent to a fake website resembling CrowdStrike’s official hiring portal.
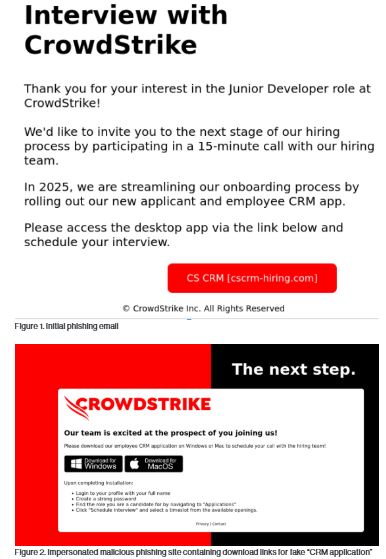
CrowdStrike analysis reveals that the site provides download options for both Windows and macOS, making it seem legitimate.
The Infection Process:
Victims unknowingly download a Rust-written Windows executable, regardless of their operating system. This advanced dropper uses various techniques to evade security measures:
Anti-debugging checks: The malware uses the IsDebuggerPresent Windows API to detect if a debugger is attached.
System requirements: It verifies that the host system has a minimum number of active processes and at least two CPU cores.
Anti-analysis measures: The dropper scans for common malware analysis and virtualization tools to avoid execution in monitored environments.
According to the CrowdStrike report, if the checks are successful, the malware shows a fake error message to appear legitimate while it continues harmful actions in the background.
The main focus of this campaign is XMRig, an open-source cryptocurrency mining software commonly misused by cybercriminals. When installed, it takes over the victim’s computer resources to mine Monero, a privacy-oriented cryptocurrency.
XMRig effectively uses both CPU and GPU resources to maximize mining potential on various hardware. However, this can cause significant performance issues on infected systems, possibly making them unresponsive.
This campaign reflects a growing trend of cryptojacking attacks on businesses and individuals. It demonstrates the use of advanced social engineering and malware evasion tactics, showing how cyber threats are evolving.
Organizations should use strong email filters, regularly train employees on security, and keep endpoint protection updated.
People, especially in the tech industry or job seekers, should be careful with unsolicited job offers and software download requests.
Protecting Against Cryptojacking:
To mitigate the risk of cryptojacking attacks, experts recommend to Use strong passwords and two-step verification, keeping software up to date, watching for strange network activity, and using security tools to block mining malware.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind