Organizations across all sectors and of all sizes are too frequently impacted by damaging ransomware incidents. Many of these incidents are perpetrated by ransomware threat actors using known vulnerabilities.
By urgently fixing these vulnerabilities, organizations can significantly reduce their likelihood of experiencing a ransomware event. In addition, organizations should implement other security controls as described on stopransomware.gov.
By infosecbulletin
/ Monday , May 20 2024
SonicWALL SSL-VPN provides secure remote access to an organization's internal network and resources through an encrypted SSL connection. This kind...
Read More
By infosecbulletin
/ Monday , May 20 2024
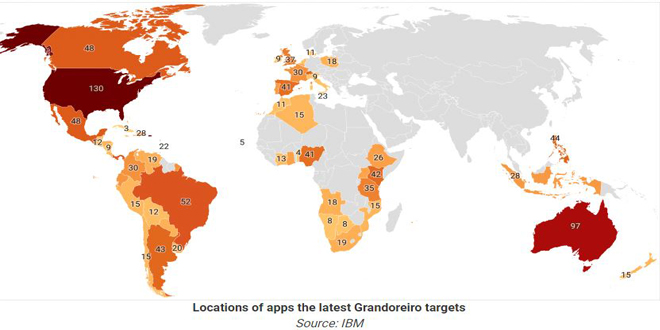
The banking trojan "Grandoreiro" is spreading widely through a phishing campaign in over 60 countries, aiming at customer accounts of...
Read More
By infosecbulletin
/ Saturday , May 18 2024
Australian police are investigating a big data breach in a healthcare company after a ransomware attack on Thursday. The website...
Read More
By infosecbulletin
/ Saturday , May 18 2024
he U.S. Cybersecurity and Infrastructure Security Agency (CISA) announced that two security flaws in D-Link routers have been added to...
Read More
By infosecbulletin
/ Saturday , May 18 2024
The "Antidot" Android Banking Trojan pretends to be a Google Play update app and targets Android users in different regions....
Read More
By infosecbulletin
/ Saturday , May 18 2024
CISA published a guide on using Encrypted Domain Name System (DNS) for federal civilian agencies to improve cybersecurity and meet...
Read More
By infosecbulletin
/ Friday , May 17 2024
Cyble Research and Intelligence Labs found that two cyber threat groups, Transparent Tribe (APT36) and SideCopy, are using advanced strategies...
Read More
By infosecbulletin
/ Friday , May 17 2024
Recorded Future's Insikt Group has discovered a major cyber threat campaign carried out by Russian-speaking hackers, possibly located in the...
Read More
By infosecbulletin
/ Friday , May 17 2024
ISA issued seventeen advisories about Industrial Control Systems (ICS) on May 16, 2024. These advisories give important information about security...
Read More
By infosecbulletin
/ Thursday , May 16 2024
Intel released 41 security advisories this Patch Tuesday, which contain information about over 90 vulnerabilities in their products. The company...
Read More
However, most organizations may be unaware that a vulnerability used by ransomware threat actors is present on their network. Through the Ransomware Vulnerability Warning Pilot (RVWP), which started on January 30, 2023, CISA is undertaking a new effort to warn critical infrastructure entities that their systems have exposed vulnerabilities that may be exploited by ransomware threat actors
As part of RVWP, CISA leverages existing authorities and technology to proactively identify information systems that contain security vulnerabilities commonly associated with ransomware attacks. Once CISA identifies these affected systems, our regional cybersecurity personnel notify system owners of their security vulnerabilities, thus enabling timely mitigation before damaging intrusions occur.
CISA accomplishes this work by leveraging its existing services, data sources, technologies, and authorities, including CISA’s Cyber Hygiene Vulnerability Scanning service and the Administrative Subpoena Authority granted to CISA under Section 2209 of the Homeland Security Act of 2002.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind