Organizations across all sectors and of all sizes are too frequently impacted by damaging ransomware incidents. Many of these incidents are perpetrated by ransomware threat actors using known vulnerabilities.
By urgently fixing these vulnerabilities, organizations can significantly reduce their likelihood of experiencing a ransomware event. In addition, organizations should implement other security controls as described on stopransomware.gov.
By infosecbulletin
/ Thursday , May 9 2024
Eclypsium recently found flaws in F5’s BIG-IP Next Central Manager, which could let attackers take control of the network. BIG-IP...
Read More
By infosecbulletin
/ Wednesday , May 8 2024
he UK government confirmed that hackers recently broke into the country's Ministry of Defence and accessed part of the Armed...
Read More
By infosecbulletin
/ Tuesday , May 7 2024
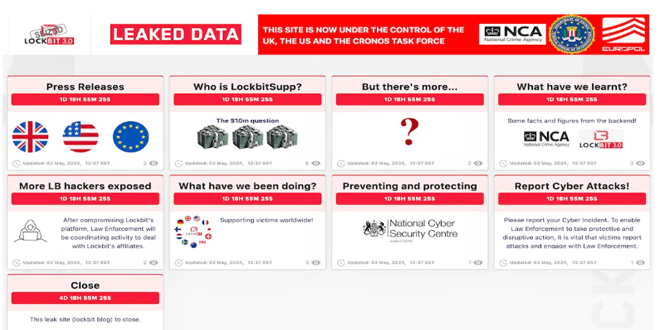
The UK, US, and Australia have imposed sanctions on the leader of the ransomware group LockBit, which is known worldwide....
Read More
By infosecbulletin
/ Tuesday , May 7 2024
Samsung has patched 25 vulnerabilities in its mobile devices. This is to strengthen them against code execution and privilege escalation...
Read More
By infosecbulletin
/ Tuesday , May 7 2024
A new law has been drafted to protect customers in electronic currency transactions. It will soon be presented to the...
Read More
By infosecbulletin
/ Tuesday , May 7 2024
The 2024 Olympic Games in Paris are coming soon. A recent cybersecurity assessment by Outpost24, a provider of cyber threat...
Read More
By infosecbulletin
/ Monday , May 6 2024
Researchers found multiple vulnerabilities in various applications and system components on Xiaomi devices. "The vulnerabilities in Xiaomi led to access...
Read More
By infosecbulletin
/ Monday , May 6 2024
New information about the Lockbit ransomware gang might be coming soon. The gang's old dark web leak site was taken...
Read More
By infosecbulletin
/ Monday , May 6 2024
The GAO reviewed NASA's cybersecurity practices and found that there is a need to update spacecraft acquisition policies and standards....
Read More
By infosecbulletin
/ Sunday , May 5 2024
Moshiul Islam Mishu, Founder & CEO of Enterprise Infosec Consultants (EIC), has been accepted into the Forbes Technology Council, the...
Read More
However, most organizations may be unaware that a vulnerability used by ransomware threat actors is present on their network. Through the Ransomware Vulnerability Warning Pilot (RVWP), which started on January 30, 2023, CISA is undertaking a new effort to warn critical infrastructure entities that their systems have exposed vulnerabilities that may be exploited by ransomware threat actors
As part of RVWP, CISA leverages existing authorities and technology to proactively identify information systems that contain security vulnerabilities commonly associated with ransomware attacks. Once CISA identifies these affected systems, our regional cybersecurity personnel notify system owners of their security vulnerabilities, thus enabling timely mitigation before damaging intrusions occur.
CISA accomplishes this work by leveraging its existing services, data sources, technologies, and authorities, including CISA’s Cyber Hygiene Vulnerability Scanning service and the Administrative Subpoena Authority granted to CISA under Section 2209 of the Homeland Security Act of 2002.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind