Microsoft Patch Tuesday security updates for November 2023 addressed 63 new vulnerabilities in Microsoft Windows and Windows Components; Exchange Server; Office and Office Components; ASP.NET and .NET Framework; Azure; Mariner; Microsoft Edge (Chromium-based), Visual Studio, and Windows Hyper-V.
The IT giant has addressed vulnerabilities with different severity ratings. Three are Critical, 56 are Important, and four are Moderate.
By infosecbulletin
/ Monday , May 12 2025
Google will pay about $1.4 billion to Texas to settle two lawsuits regarding location tracking and biometric data storage without...
Read More
By infosecbulletin
/ Friday , May 9 2025
YouTube has restricted access to at least four Bangladeshi television channels in India following a takedown request from the Indian...
Read More
By infosecbulletin
/ Friday , May 9 2025
Microsoft has fixed critical vulnerabilities in its core cloud services, including Azure Automation, Azure Storage, Azure DevOps, and Microsoft Power...
Read More
By infosecbulletin
/ Thursday , May 8 2025
The cyber threat landscape is rapidly changing, with a notable increase in ransomware activity in April 2025, driven by the...
Read More
By infosecbulletin
/ Thursday , May 8 2025
SonicWall has released patches for three security flaws in SMA 100 Secure Mobile Access appliances that could allow remote code...
Read More
By infosecbulletin
/ Thursday , May 8 2025
From April 2024 to April 2025, Flashpoint analysts noted that the financial sector was a major target for threat actors,...
Read More
By infosecbulletin
/ Thursday , May 8 2025
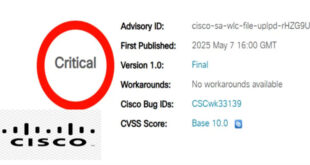
Cisco has issued a security advisory for a critical vulnerability in its IOS XE Software for Wireless LAN Controllers (WLCs)....
Read More
By infosecbulletin
/ Wednesday , May 7 2025
Attackers linked to the Play ransomware operation deployed a zero-day privilege escalation exploit during an attempted attack against an organization...
Read More
By infosecbulletin
/ Wednesday , May 7 2025
Hackers are exploiting an unauthenticated remote code execution vulnerability in the Samsung MagicINFO 9 Server to take control of devices...
Read More
By infosecbulletin
/ Tuesday , May 6 2025
CISA added the Langflow vulnerability, CVE-2025-3248 (CVSS score 9.8), to its Known Exploited Vulnerabilities catalog. Langflow is a popular tool...
Read More
Three of these vulnerabilities are actively exploited in attacks in the wild:
CVE-2023-36033 – Windows DWM Core Library Elevation of Privilege Vulnerability
Attackers can use a vulnerability in the Windows Desktop Manager (DWM) to gain higher privileges. By exploiting this flaw, they can obtain SYSTEM privileges. If combined with a remote code execution bug, this can fully compromise a system.
CVE-2023-36036 – Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability
A flaw in this driver can be abused by an attacker to get SYSTEM privileges. This driver is used to manage files stored in the cloud and is loaded by default on many versions of Windows, making it an easy target for attacks. The post by ZDI mentions that this bug is probably used together with a code execution bug in attacks.
CVE-2023-36025 – Windows SmartScreen Security Feature Bypass Vulnerability
An attacker can use this flaw to bypass Windows Defender SmartScreen checks and other prompts. This flaw can be used in phishing campaigns to avoid warnings about opening a malicious document.
ALSO READ:
Juniper Patches Over 30 Vulnerabilities in Junos OS
The main issue fixed by Microsoft’s Patch Tuesday security updates for November 2023 is a Remote Code Execution vulnerability in Windows PGM (Pragmatic General Multicast). This flaw, identified as CVE-2023-36397 (CVSS 9.8), allows an attacker to execute code with higher privileges without needing user interaction.
The full list of vulnerabilities addressed by Microsoft for November 2023 is available here.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind