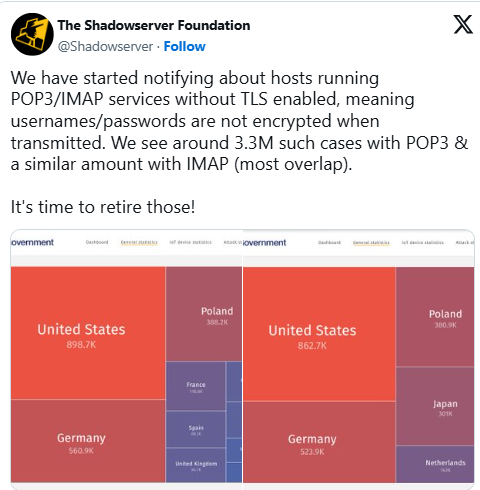
Around 3.3 million servers are running POP3/IMAP email services without encryption (TLS) enabled, the Shadowserver Foundation, a nonprofit security organization, has discovered. Most of these servers reside in the US, Germany, and Poland.
POP3 (Post Office Protocol version 3) is an aging protocol used by email clients to retrieve emails from a mail server. It is often used alongside the newer protocol IMAP (Internet Message Access Protocol).
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
By infosecbulletin
/ Monday , June 16 2025
SafetyDetectives’ Cybersecurity Team discovered a public post on a clear web forum in which a threat actor claimed to have...
Read More
By infosecbulletin
/ Sunday , June 15 2025
WestJet, Canada's second-largest airline, is looking into a cyberattack that has affected some internal systems during its response to the...
Read More
By infosecbulletin
/ Saturday , June 14 2025
Resecurity found 7.4 million records of Paraguayan citizens' personal information leaked on the dark web today. Last week, cybercriminals attempted...
Read More
By infosecbulletin
/ Friday , June 13 2025
HashiCorp has revealed a critical vulnerability in its Nomad tool that may let attackers gain higher privileges by misusing the...
Read More
By infosecbulletin
/ Friday , June 13 2025
SoftBank has disclosed that personal information of more than 137,000 mobile subscribers—covering names, addresses, and phone numbers—might have been leaked...
Read More
By infosecbulletin
/ Friday , June 13 2025
Serious security vulnerabilities in Trend Micro Apex One could allow attackers to inject malicious code and elevate their privileges within...
Read More
The Shadowserver Foundation tracks 3.3 million POP3/IMAP servers along the globe that do not have TLS encryption.
“It’s time to retire those services!” the organization warns.
“We have started notifying about hosts running POP3/IMAP services without TLS enabled, meaning usernames/passwords are not encrypted when transmitted. We see around 3.3M such cases with POP3 & a similar amount with IMAP (most overlap).”
Almost 900,000 of these servers are from the US, while Germany follows in second place with 523,000 servers. Poland and Japan are next on the list, with 381,800 and 301,800 unprotected servers, respectively.
Users of such email services should be aware that anyone with basic network monitoring tools can intercept their communications and steal their credentials.
“Note that regardless of whether TLS is enabled or not, service exposure may enable password-guessing attacks against the server,” the Shadowserver Foundation said.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














