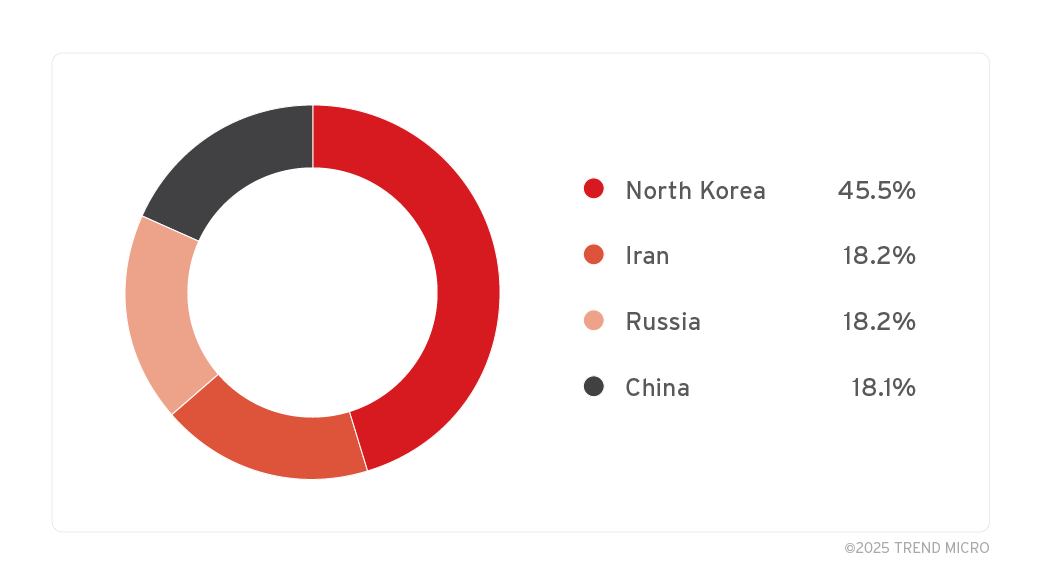
11 nation-state groups from North Korea, China, and Russia are exploiting a vulnerability in a common feature of Microsoft Windows. Researchers at the Zero Day Initiative (ZDI) have found several campaigns exploiting the bug in Windows shortcut (.lnk) files, dating back to 2017.

Microsoft hasn’t assigned a CVE number, but ZDI, a Trend Micro cybersecurity division, labeled it as ZDI-CAN-25373. The vulnerability is related to how Windows shows shortcut contents, based on ZDI’s findings. These shortcuts, or shell links, let users easily access files, folders, or applications elsewhere in the system.
“In attack campaigns that utilize .lnk files, threat actors will often change the icon to confuse and entice the victim into executing the shortcut,” the experts said in a report published on Tuesday.
“Since Windows always suppresses display of the .lnk extension, threat actors will often add a ‘spoof’ extension such as .pdf.lnk along with a matching icon to further trick users. A .lnk file will usually have an arrow on the lower-left side of the icon.”
Researchers estimated that there are likely many more exploitation attempts than those found. Microsoft claimed the tactics described by ZDI are of “limited practical use to attackers.”
Just 20% of the campaigns the researchers analyzed were focused on financial gain while about 70% were aimed at espionage and information theft.
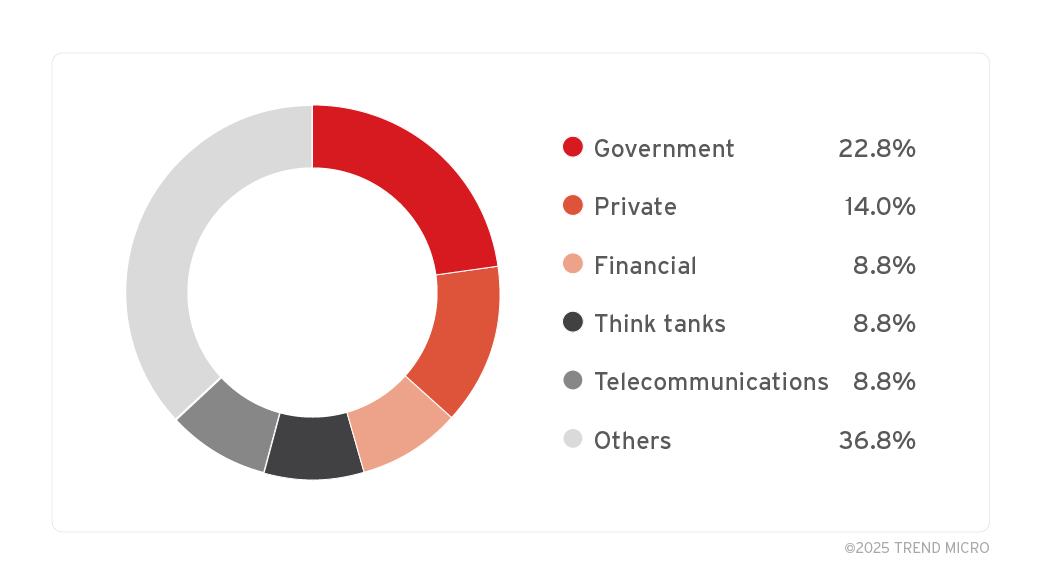
Hackers are mainly targeting government agencies, cryptocurrency firms, think tanks, telecom companies, and military organizations, according to ZDI.
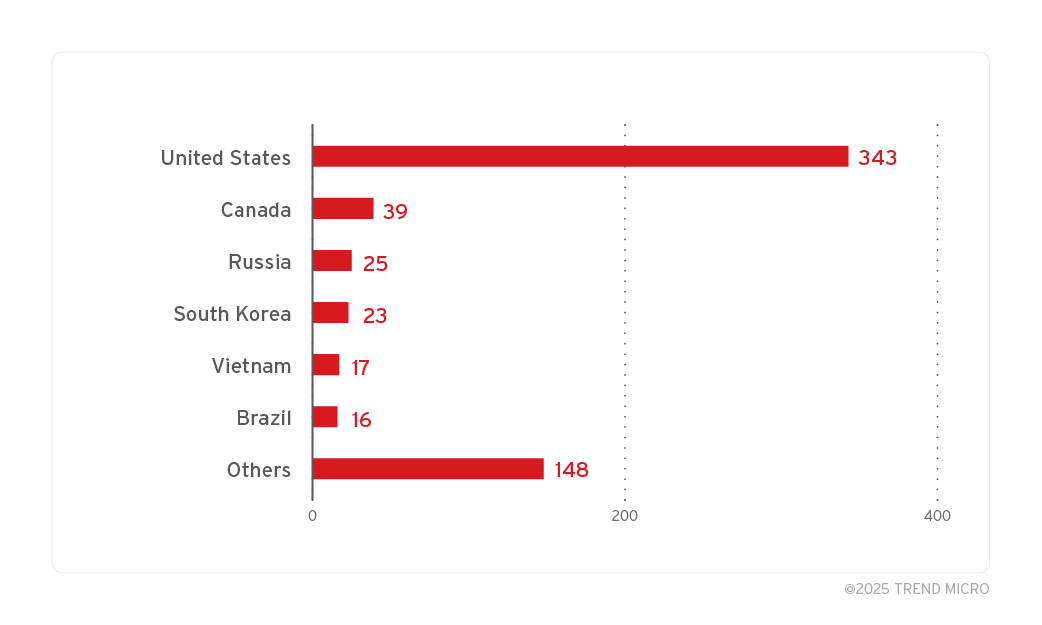
Most victims identified by ZDI, over 300, are in the U.S., with additional victims in Canada, Russia, South Korea, Vietnam, and Brazil. ZDI observed that North Korea’s APT37 and similar groups often employed large .lnk files filled with excess whitespace and irrelevant content to avoid detection.
A Microsoft spokesperson saying the company is considering to address the flaw in the future:
“We appreciate the work of ZDI in submitting this report under a coordinated vulnerability disclosure. Microsoft Defender has detections in place to detect and block this threat activity, and the Smart App Control provides an extra layer of protection by blocking malicious files from the Internet. As a security best practice, we encourage customers to exercise caution when downloading files from unknown sources as indicated in security warnings, which have been designed to recognize and warn users about potentially harmful files. While the UI experience described in the report does not meet the bar for immediate servicing under our severity classification guidelines, we will consider addressing it in a future feature release.”
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














