We all love snapping pics on our phones, right? They help us catch life’s fun, goofy, and sweet moments. But what if I told you that sometimes our phone cameras might see more than just smiles? I went on a snooping adventure online and found some stories that made me look at my phone camera differently.
First, I bumped into stories about apps like BeautyPlus and YouCam Perfect. They promise to make our selfies look snazzy, but guess what? Behind the scenes, they might be playing nosy Parker, peeking at our data. It’s like having a friend over for a movie night, only to catch them snooping in your snack cupboard when you’re not looking!
By infosecbulletin
/ Wednesday , September 24 2025
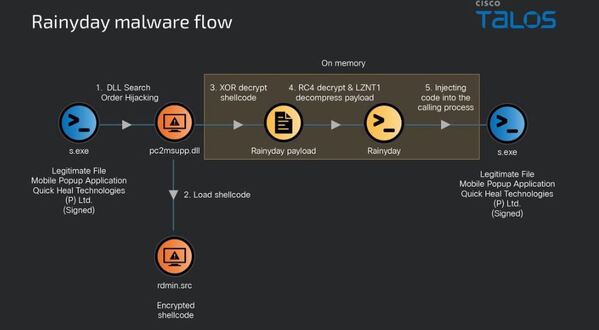
Cisco Talos researchers have discovered an ongoing espionage campaign since 2022, targeting telecom and manufacturing sectors in Central and South...
Read More
By infosecbulletin
/ Tuesday , September 23 2025
A submarine cable project will enhance the digital infrastructure of the Asia-Pacific region. Covering around 8,000 kilometers underwater, it's set...
Read More
By infosecbulletin
/ Tuesday , September 23 2025
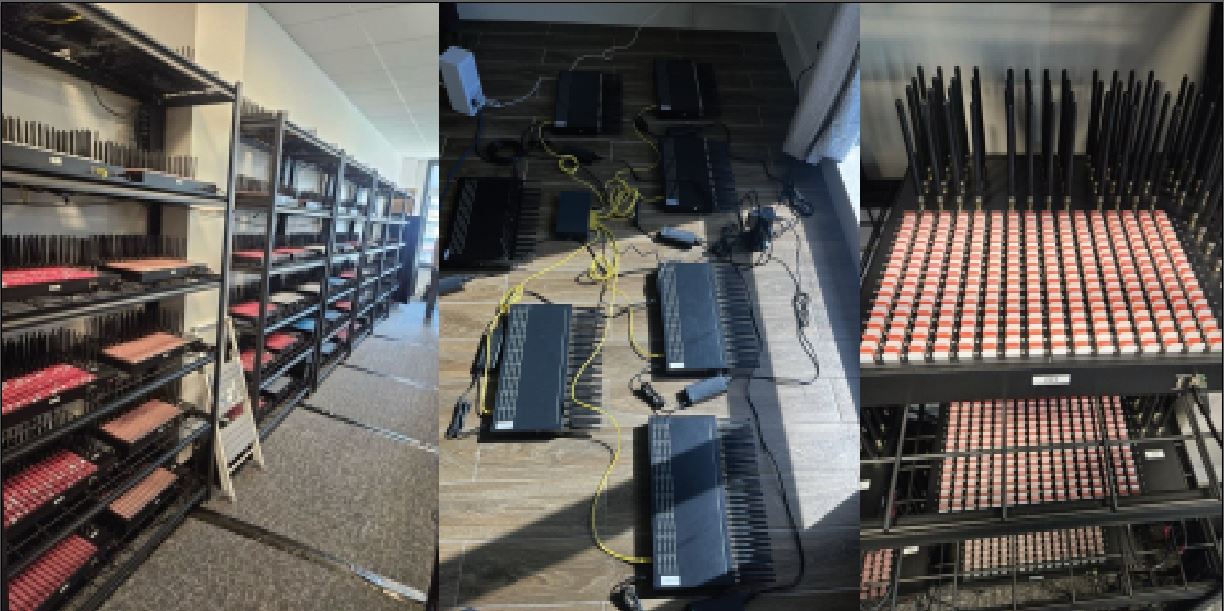
The U.S. Secret Service dismantled a network of electronic devices located throughout the New York tristate area that were used...
Read More
By infosecbulletin
/ Tuesday , September 23 2025
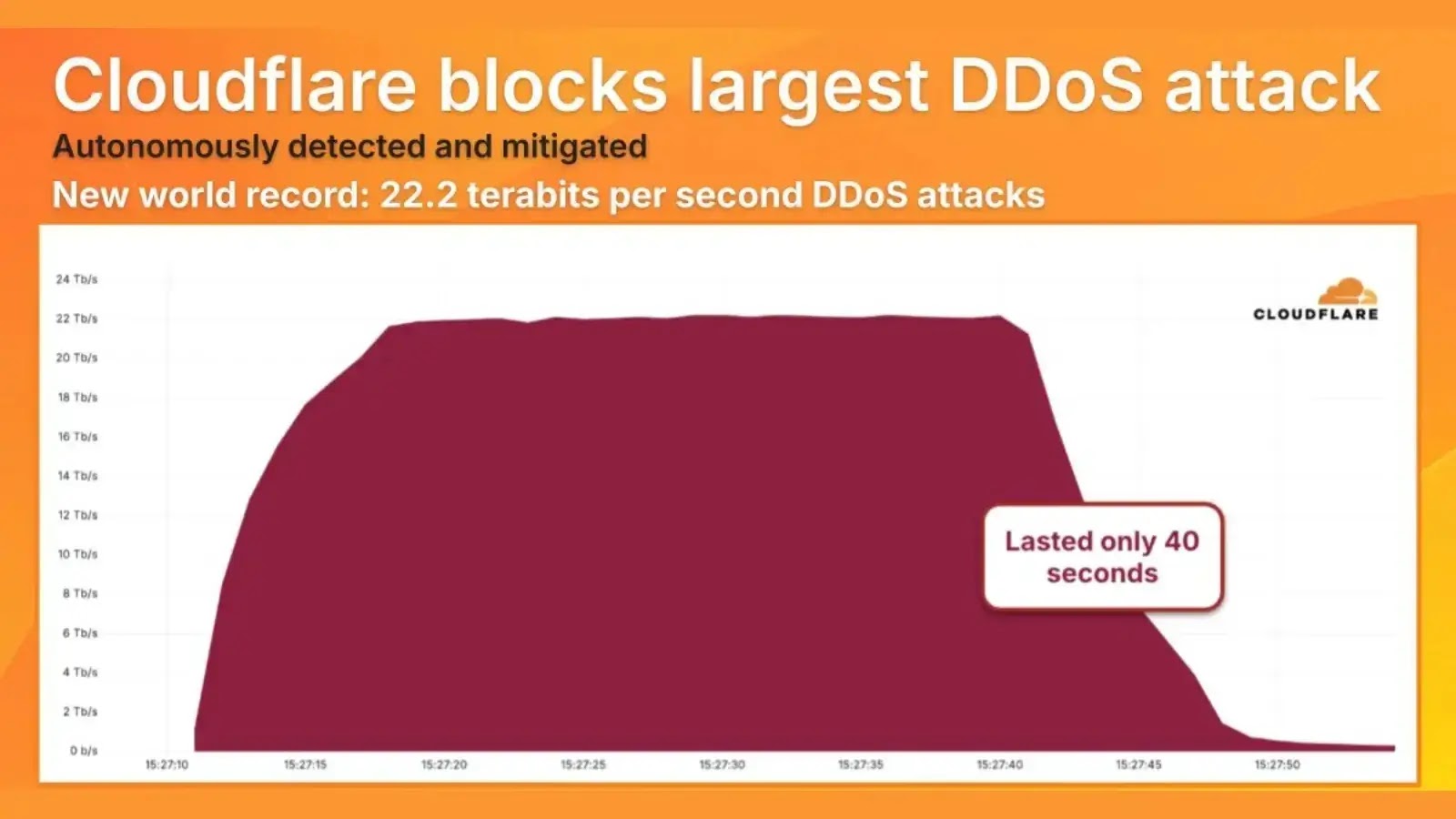
Cloudflare announced today that it has successfully defended against the largest recorded DDoS attack, which peaked at 22.2 terabits per...
Read More
By infosecbulletin
/ Tuesday , September 23 2025
Microsoft has announced a new $4 billion investment in Wisconsin for a second hyperscale AI data center. This adds to...
Read More
By infosecbulletin
/ Tuesday , September 23 2025
An organised racket has reportedly siphoned off lakhs from Standard Chartered Bangladesh's (SCB) credit card holders, raising serious cybersecurity concerns....
Read More
By infosecbulletin
/ Sunday , September 21 2025
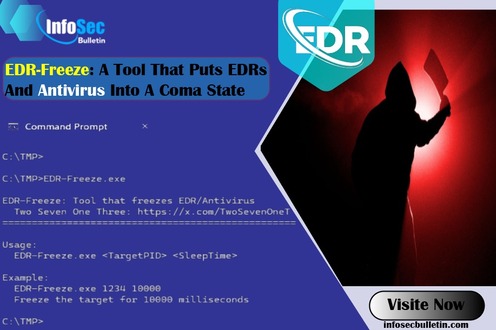
A new proof-of-concept tool named EDR-Freeze has been developed, capable of placing Endpoint Detection and Response (EDR) and antivirus solutions...
Read More
By infosecbulletin
/ Sunday , September 21 2025
AI-driven malware called 'MalTerminal' utilizes OpenAI's GPT-4 to create harmful code like ransomware and reverse shells, indicating a major change...
Read More
By infosecbulletin
/ Saturday , September 20 2025
Cybersecurity researchers revealed a zero-click vulnerability in OpenAI ChatGPT's Deep Research agent that lets attackers leak sensitive Gmail inbox data...
Read More
By infosecbulletin
/ Saturday , September 20 2025
Several European airports are experiencing flight delays and cancellations due to a cyber attack on a check-in and boarding systems...
Read More
Then, there’s this creepy part where the bad guys on the internet can turn our phone cameras into spying eyes. They sneak into our phones, and the camera is spying on you before you know it. It’s like having someone peeking through your window, watching your every move. And when you’re typing your bank details or personal messages, they collect all the juicy details.
Now, shifting gears to the work scene. Imagine you’re on a video call with your boss or a client, discussing the next big thing for your company. If your phone camera has been hijacked, it’s not just you and your boss in that meeting. The sneaky peepers are listening in, gathering all the company secrets they can grab. It’s like having a gossip-loving neighbor eavesdropping on your private chats and spreading the word.
So, what can we do to stop our phone cameras from becoming gossip mongers? Here are some easy-peasy tips:
Know Your Apps:
Only download apps from places you trust, like the official app store, and read the reviews to see if they play nice.
Check Permissions:
If an app wants to use your camera but doesn’t need to, say “No, thank you!” It’s like not letting someone into your house if they don’t have a good reason to be there.
Cover Up:
When you’re not using your camera, cover it up. A small sticker will do the trick. It’s like closing your curtains to keep peeping toms out.
Stay Updated:
Keep your phone and apps updated. It’s like making sure your locks are strong and working well.
Get the Experts:
If you’re unsure, ask someone who knows this techy stuff to check your phone. It’s like asking a friend who’s good with cars to check your engine.
With these simple tricks, you can keep the nosy parkers out of your phone, making sure your camera stays as your trusty selfie buddy and nothing else!
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind