Jeremiah Fowler, a security researcher, claimed to discover a major vulnerability in India’s data security. He found an unprotected database with a large amount of biometric data, such as fingerprints, facial scans, and other sensitive information, belonging to millions of Indian citizens.
Jeremiah Fowler published his findings on global planet. “a non-password-protected database that contained over 1.6 million documents belonging to an Indian leading provider of biometric authentication solutions, with offices in the USA and Australia.
The exposed records included the biometric identity information of members of the police, army, teachers, and railway workers. In parallel, it appeared that the data might have been for sale on a dark web related Telegram group” websiteplanet report reads.
It is estimated that the amount of exposed data 500GB, reportedly originated from two Indian firms, ThoughtGreen Technologies and Timing Technologies, both of which provide application development and biometric verification services. The leak included biometric data not only from police and military personnel but also from civilians, such as teachers and railway workers.
Websiteplanet post reads, “The records span from 2021-2024 and were actively updating in real time during my research. There were 284,535 documents marked as Physical Efficiency Test (PET) for police and law enforcement officers. The database also stored images of 143,173 signatures and a very large number of .PDF documents that contained the name, images, and fingerprints of multiple individuals. I saw numerous files featuring the biometric data of individuals who appeared to be high-ranking military personnel. The database also contained several mobile applications and installation files compressed in .zip format.”
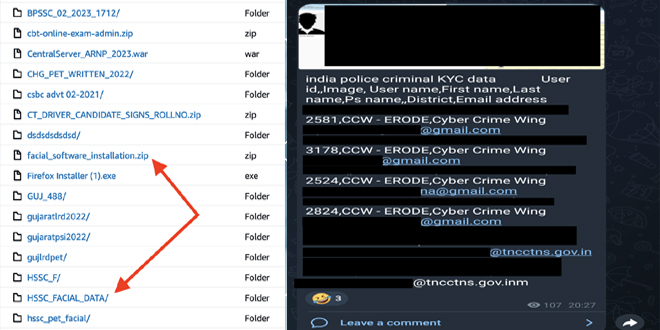
Hackread reported, “Fowler noted that this data might already be up for sale on a Telegram group, which could put millions at risk of a wide range of threats”.
Biometric data, like fingerprints, are unique identifiers linked to someone’s identity. They can’t be easily changed, which makes them ideal for malicious activities like impersonation and identity theft.
“We take data security very seriously, have taken immediate steps to secure the exposed data,” a member of ThoughtGreen Technologies wrote in an email to WIRED. “Due to the sensitivity of data, we cannot comment on specifics in an email. However, we can assure you that we are investigating this matter thoroughly to ensure such an incident does not occur again.” Wired reported.
Shivangi Narayan, an independent researcher in India, told to media that the country’s data protection law needs to be made more robust, and companies and organizations need to take greater care with how they handle people’s data. “A lot of data is collected in India, but nobody’s really bothered about how to store it properly,” Narayan says. Data breaches are happening so regularly that people have “lost that surprise shock factor,” Narayan says. In early May, one cybersecurity company said it had seen a face-recognition data breach connected to one Indian police force, including police and suspect information.
The incident highlights the urgent need for robust data security measures in India. Stringent regulations and data protection protocols are essential to safeguard sensitive information and prevent similar breaches in the future.
Source: Wired, CSO ONLINE, Hackread, Arabianpost, Websiteplanet,
(Media Disclaimer: This report is based on research conducted internally and externally using different ways. The information provided is for reference only, and users are responsible for relying on it. Infosecbulletin is not liable for the accuracy or consequences of using this information by any means)
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














