Simone Margaritelli has discovered a serious remote code execution (RCE) vulnerability in the Common Unix Printing System (CUPS), impacting all GNU/Linux systems.
Simone Margaritelli has revealed technical details about the unauthenticated RCE flaw affecting all GNU/Linux systems, which he previously reported.
The flaw, comprising four CVEs (CVE-2024-47176, CVE-2024-47076, CVE-2024-47175, CVE-2024-47177), enables unauthenticated attackers to execute arbitrary commands on vulnerable systems, threatening network security significantly.
“From a generic security point of view, a whole Linux system as it is nowadays is just an endless and hopeless mess of security holes waiting to be exploited.”
A security researcher found the vulnerability and explained it in detail in a write up. The researcher identified several critical issues in the CUPS system, including:
CVE-2024-47176: The cups-browsed service listens on UDP port 631 and allows requests to an attacker-controlled URL from any source.
CVE-2024-47076: This allows attackers to send unfiltered data to the CUPS system.
CVE-2024-47175: This vulnerability allows attackers to insert malicious data into a temporary PPD file created by the libppd library.
CVE-2024-47177: The cups-filters package lets attackers run any command through a specific setting.
Margaritelli showed how vulnerabilities can be exploited for remote code execution on an updated Ubuntu 24.04.1 LTS system using cups-browsed 2.0.1.
An unauthenticated remote attacker can replace existing printers’ IPP URLs with a malicious one, leading to arbitrary command execution when a print job begins.
Vulnerabilities can be exploited via the WAN/public internet by sending a UDP packet to port 631, or through the LAN by spoofing zeroconf/mDNS/DNS-SD advertisements.
Margaritelli scanned all public IPv4 addresses and found connections from hundreds of thousands of devices, showing that many systems are vulnerable.

Shodan reports that about 73,000 CUPS servers are exposed and accept custom packets from untrusted sources through UDP port 631.
The vulnerabilities affect most GNU/Linux distributions, some BSDs, Google Chromium/ChromeOS, Oracle Solaris, and possibly more systems where CUPS and specifically cups-browsed are packaged
Fixes have been reported, but the researcher expressed frustration with the disclosure process due to delays and dismissiveness from the developers.
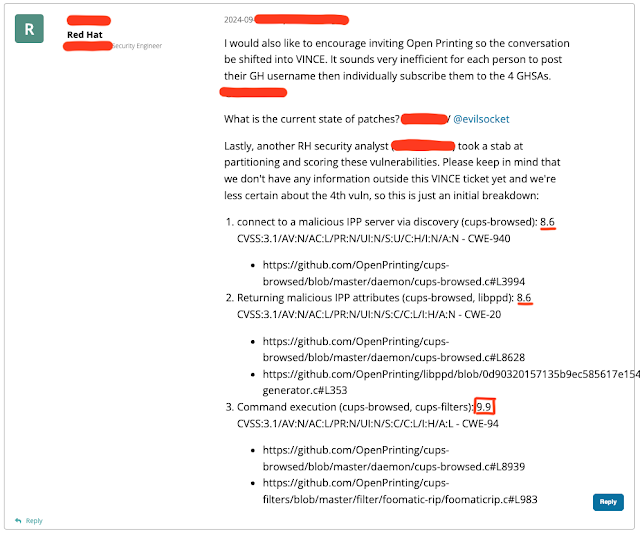
The severity of the vulnerability is underscored by the initial CVSS score of 9.9, estimated by a Red Hat engineer.
What you need to know for now, according to Margaritelli, is:
Disable and/or remove the cups-browsed service.
Update your CUPS installation to bring in security updates if or when available.
Block access to UDP port 631 and consider blocking off DNS-SD, too.
It affects “most” Linux distros, “some” BSDs, possibly Google ChromeOS, Oracle’s Solaris, and potentially others, as CUPS is bundled with various distributions to provide printing functionality.
To exploit this across the internet or LAN, a miscreant needs to reach your CUPS service on UDP port 631. Hopefully none of you have that facing the public internet. The miscreant also has to wait for you to start a print job.
If port 631 isn’t directly reachable, an attacker may be able to spoof zeroconf, mDNS, or DNS-SD advertisements to achieve exploitation. Details of that path will be disclosed later, we’re promised.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














