Ransomware attacks on schools spiked in June, reaching a new record high. On average, ransomware groups claimed more than one attack per day on educational institutions.
In June, there were 37 attacks on schools, which is more than the 24 attacks that occurred the month before. This information is from Recorded Future, who collected data from various sources such as extortion sites, government agencies, news reports, and hacking forums.
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
By infosecbulletin
/ Monday , June 16 2025
SafetyDetectives’ Cybersecurity Team discovered a public post on a clear web forum in which a threat actor claimed to have...
Read More
By infosecbulletin
/ Sunday , June 15 2025
WestJet, Canada's second-largest airline, is looking into a cyberattack that has affected some internal systems during its response to the...
Read More
By infosecbulletin
/ Saturday , June 14 2025
Resecurity found 7.4 million records of Paraguayan citizens' personal information leaked on the dark web today. Last week, cybercriminals attempted...
Read More
By infosecbulletin
/ Friday , June 13 2025
HashiCorp has revealed a critical vulnerability in its Nomad tool that may let attackers gain higher privileges by misusing the...
Read More
By infosecbulletin
/ Friday , June 13 2025
SoftBank has disclosed that personal information of more than 137,000 mobile subscribers—covering names, addresses, and phone numbers—might have been leaked...
Read More
By infosecbulletin
/ Friday , June 13 2025
Serious security vulnerabilities in Trend Micro Apex One could allow attackers to inject malicious code and elevate their privileges within...
Read More
The increase was mainly caused by the Clop ransomware group from Russia. They used vulnerability in the MOVEit file transfer tool to access computer networks globally. The attacks have targeted a wide range of organizations — including Shell, Siemens Energy, and the largest public pension fund in the U.S. — and hit the education sector especially hard.
ALSO READ:
The GPT-4 API Available To Everyone
“There was a significant impact on schools due to the Cl0P MOVEit attacks,” stated Allan Liska, a ransomware expert at Recorded Future who tracks attacks. “Cl0p was responsible for 12 attacks against schools in June — almost one-in-three — and propelled school ransomware attacks to their worst month ever.”
In contrast, Clop was only accountable for a single assault on educational institutions from January to May 2023.
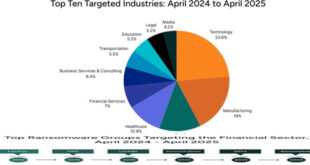
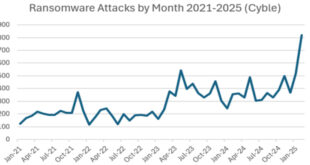
While Clop gained significant attention in June due to the MOVEit attacks, it is important to note that there were other active groups as well. In total, there were 408 victims posted to ransomware sites in June, compared to 414 the previous month and just 150 in June 2022.
LockBit is behind most of the recent attacks, which includes targeting a dental insurance provider, a water utility in Portugal, and the Royal Mail in the UK.
Liska said that while Clop is responsible for a lot of activity in June, ransomware attacks in general have been very alarming. “There are more groups going after more targets and it is a never ending barrage of attacks.”




Source: the record




 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind