The US Federal Bureau of Investigations (FBI) has taken down its second cybercriminal forum of the year. Known and used by hackers around the world – the notorious Genesis Market has met its end. Cybernews has all the details on the raid – and the infamous market.
Now, where the Genesis Market domain once lived, the FBI put up its calling card instead.
The FBI is calling the global sting Operation Cookie Monster.
“Genesis market’s domains have been seized by the FBI pursuant to a seizure warrant issued by the United States District Court for the Eastern District of Wisconsin,” the FBI replacement webpage states.
Genesis Market is known in the hacker community as an invitation-only, dark web forum, and has been in existence since March 2018, with users all over the world.
The market is estimated to have offered up over 1.5 million computers compromised around the world containing over 80 million account access credentials, the US Department of Justice (DOJ) said.
Operation Cookie documents released Thursday by the DOJ show that the FBI had been working the case dating back to December 2020.
The Takedown
The FBI’s Milwaukee Field Office led the complex international investigation, which involved 44 other FBI field offices, law enforcement organizations worldwide, including Europol, and private sector coordination.
The documents also show the FBI’s break in the ase was obtaining an forensic image of the server hosting the Genesis’ Backend #1 IP address.
That server contained “voluminous records” associated with the market’s operations, including its “customers” usernames, passwords, email accounts, Jabber accounts, search histories, purchase history, and even BTC addresses, according to the FBI documents.
“Today’s takedown of Genesis Market is a demonstration of the FBI’s commitment to disrupting and dismantling key services used by criminals to facilitate cybercrime,” said FBI Director Christopher Wray.
Besides the Genesis Market online site, the sting resulted in the seizure of 11 other domain names used to support the market’s infrastructure.
“The takedown is a warning shot over the bow of digital identity stealers,” said Matthew Gracey-McMinn, Head of Threat Research at Netacea, a UK-based bot software management firm.
“The Genesis Market was a large, well-known marketplace, and takedowns such as this may scare others operating in this space, encouraging them to slow down or cease their operations, especially if arrests are made,” Gracey-McMinn said.
Although the DOJ gave little detail about other arrests, British authorities said there were roughly 120 arrests, more than 200 searches conducted, and almost 100 pieces of “preventative activity.”
“This case is a great example of the FBI’s ability to leverage our technical capabilities and work shoulder-to-shoulder with our international partners to take away the tools cybercriminals rely on to victimize people all across the world,” FBI Chief Wray said.
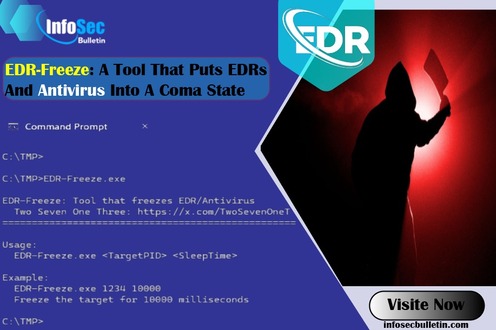
Like other darknet criminal forums – such as the recently shuttered BreachForums and the busted Russian-linked Hydra in 2022 – Genesis Market is a go-to dark market for cybercriminals to purchase all kinds of illegally obtained access credentials stolen from malware-infected computers around the world.
Gracey-McMinn said the takedown of the Market would most certainly “reduce the ease with which digital identity fraud can be conducted.”
Although Gracey-McMinn also pointed out that “the loss of this service will force less-skilled attackers to either give up or get better.”
Who is Genesis Market?
Besides credentials such as usernames and passwords for email, bank accounts, and social media, the site sold digital fingerprints, stealer malware, and web vulnerability kits – and as Initial access brokers (IABs), selling illegitimate access to corporate networks.
Digital fingerprints are “unique combinations of device identifiers and browser cookies that circumvent anti-fraud detection systems used by many websites,” allowing the purchaser to assume the full identity of a victim, the FBI explained.
The market was found selling the digital fingerprints of more than 2 million people, said UK officials.
Many of the IABs sold were proven to have been used in many global ransomware attacks, including those connected to the financial sector, critical infrastructure, and federal, state, and local government agencies, the DOJ said.

Gracey-McMinn explained that the marketplace looked a lot like any other online shopping catalog.
The user-friendly site allowed hackers to search for stolen credentials based on location and by specific type of account, such as, banking, social media, or email.
“For instance,” Gracey-McMinn said, “if you wanted access to a Canadian bank account, you could very easily set your search to look for a bot located in Canada and with access to financial details.
“Then you simply click either the “buy now” or “add to cart” options – just like a regular online retail site,” he said.
“Genesis Market had an incredibly responsive customer service team and were focused on making sure that the stolen identities used on their site could be used very easily; buyers’ issues were resolved promptly,” Gracey-McMinn said.
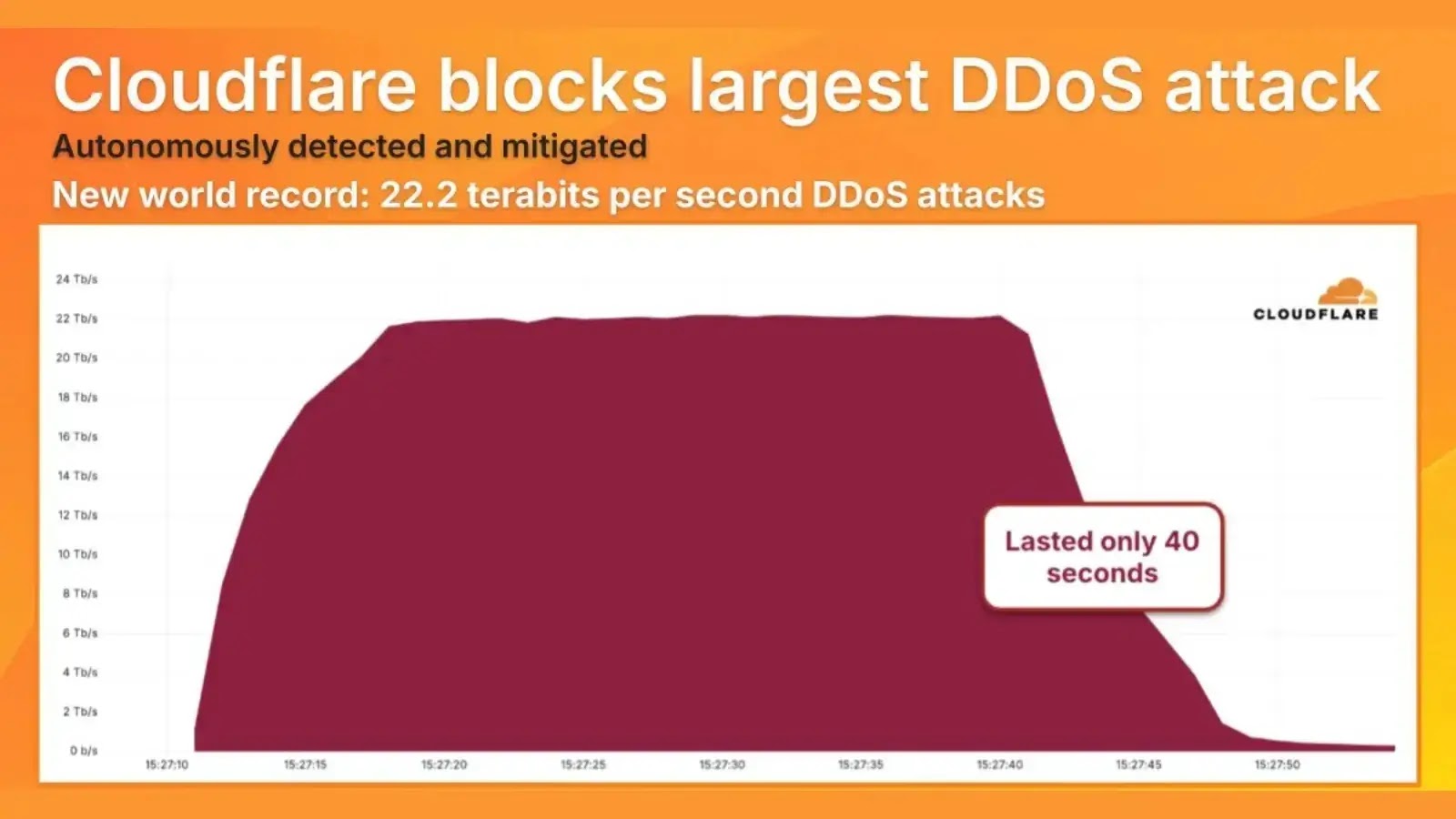
Genesis Market was also known as go-to spot for cybercriminals looking to purchase bots and/or botnets – commonly used to carry out large-scale distributed denial-of-service (DDoS) attacks.
But according to the Gracey-McMinn, Genesis Market bots were most often used for “large-scale infection of consumer devices to steal their fingerprints, cookies, saved logins and autofill form data,” using infostealer malware.
The bots also would steal “unique identifiers left behind by the victim’s devices and browsers, when visiting websites – for example, browser version, screen resolution, IP address or operating system,” said Cyril Noel-Tagoe, Principal Security Researcher at Netacea.
The combination of the stolen data – packaged up and put for sale on the Genesis Market – created the perfect storm for account access,
“Upon purchase, the criminals would be provided with a custom browser to load the data into and may browse the Internet masquerading as the hapless victim, all without any access to the original device,” said Gracey-McMinn.
What’s more, “the Genesis Market also kept its data up to date by continuing this data collection even after the bot had been purchased,” Noel-Tago said,
“This meant that even if the victim changed their passwords after realising their account on a site was compromised, the purchaser would gain access to the new passwords,” Noel-Tago said.
Hundred, if not thousands of these bots have been reported sold on the Genesis Market site, ranging from less than a US dollar to more than three hundred times that amount.
A 2022 UK survey by Netacea reported over 350,000 of the bots up for sale on the marketplace at any one time.
By March 2023, Netacea reported those numbers had grown to 450,000 bots available for sale on the marketplace.

Dark market aftermath
Earlier this month, the FBI arrested the administrator of the popular hacker site BreachForums.
The suspect, Conor Brian Fitzpatrick, a 20-year old hacker from New York, had been running the site since the seizure of yet another dark web marketplace in 2022, RaidForums.
Since the Breached takedown, multiple ‘replacement’ hacker forums have popped up on the web in recent weeks, leading to rumors in the underworld that the US feds have set the sites up to catch still-operating cybercriminals.
The last time we saw the feds take over an entire site was with the bust of the infamous Hive ransomware group.
Now that Genesis Market is officially defunct, Noel-Tagoe said we should “expect to see an exodus of sellers and customers to competitor marketplaces.”
“There are multiple other illicit marketplaces selling logs and credentials, although not on the scale of the Genesis Market.” Noel-Tagoe said
“Alternatively, if a significant core of the Genesis Market administrators evade law enforcement, they may splinter off and create a new version of the site,” he added.
Noel-Tagoe noted, “Genesis’ unique selling point was providing fingerprint data which could be loaded through a specialised chromium-based browser alongside their logs.”
“Any service looking to replicate the Genesis Market may look to include this functionality.” said Noel-Tagoe.
The intelligence agencies of more than a dozen nations were involved in the Genesis Market takedown, including France, Germany, Poland, Canada, Norway, Spain, Australia, and Sweden.
The DOJ release said all victim credentials recovered during the investigation have been handed over to the ‘Have I been Pwned’ website, which is a free resource accessible for the public to check if their personal data has been compromised.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind