Threatdown Managed Detection and Response (MDR) team has discovered the RansomHub ransomware gang using a new attack method wityh two tools: TDSKiller, to disable EDR system, and LaZagne, for stealing credentials.
Although both TDSSKiller and LaZagne have been used by attackers for years, this is the first record of RansomHub using them in its operations, with the TTPs not listed in CISA’s recently published advisory on RansomHub. The tools were deployed following initial reconnaissance and network probing through admin group enumeration, such as net1 group “Enterprise Admins” /do.
TDSSKiller:
RansomHub conducted reconnaissance and privilege enumeration, then tried to disable security services using
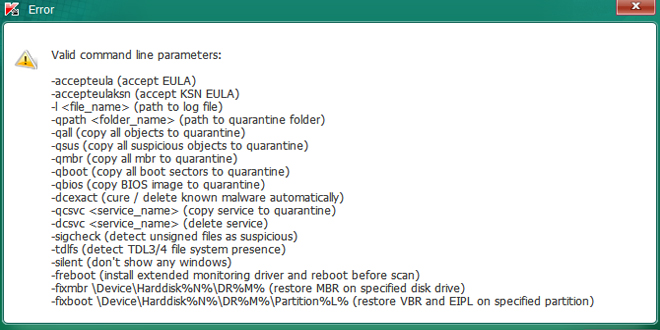
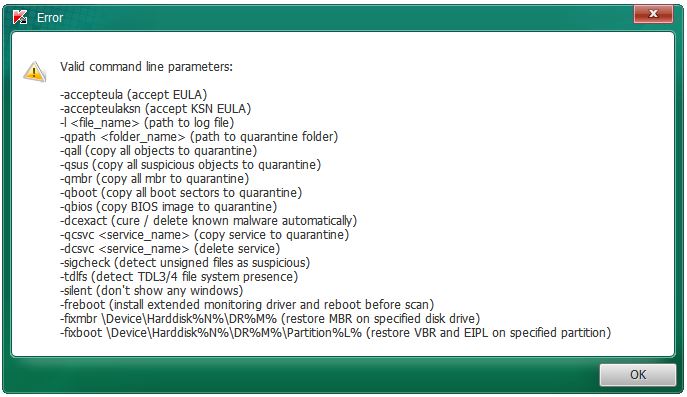
TDSKiller, a legitimate kaspersky tool for removing rootkits. It can also disable EDR software via a command line script or batch file.
RansomHub used TDAKiller to disable crucial security services like Malwarebytes. The attacker succedd because
they had admin priviliges, despite anti-tampering protections.
Command line details:
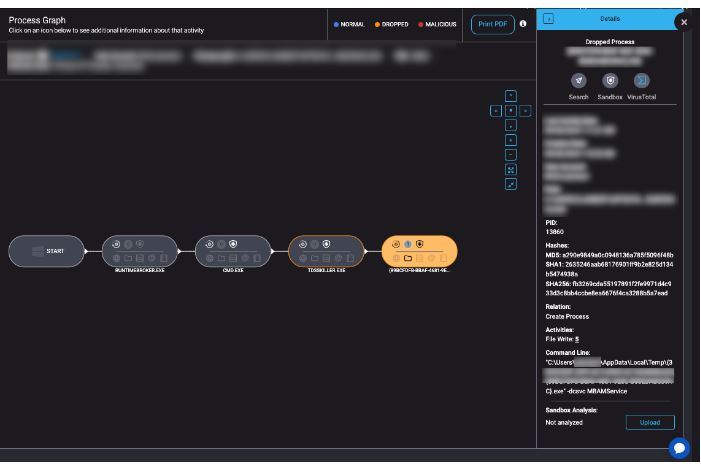
* Command line: tdsskiller.exe -dcsvc MBAMService
* The -dcsvc flag was used to target specific services. In this instance, attackers attempted to disable MBAMService.
*File path: The attackers attempted to run TDSSKiller from a temporary directory (C:\Users\<User>\AppData\Local\Temp\), with a dynamically generated filename like {89BCFDFB-BBAF-4631-9E8C-P98AB539AC}.exe.
IOCs
File Name: TDSSKiller.exe
SHA-256: 2d823c8b6076e932d696e8cb8a2c5c5df6d392526cba8e39b64c43635f683009
File Size: 4.82 MB
MD5: ff1eff0e0f1f2eabe1199ae71194e560
LaZagne:
RansomHub tried to use LaZagne, a tool for stealing credentials, to access stored login info from the compared
system. LaZagne helps attackers retrive credentials from various applications like browsers, email, and database
, enabling them to naviagate through the network more easily.
Command line details:
-
- Command line: LaZagne.exe database
* The attackers specifically targeted database credentials, a key asset in their broader plan to access critical infrastructure and escalate privileges. Database credentials can grant attackers control over sensitive data or administrative access to critical systems.
* File write and delete activity: LaZagne generated 60 file writes and 1 file deletion during its execution. These writes were likely logs of extracted credentials, while the deletion likely served to cover up traces of the credential-harvesting operation.IOCs
File Name: LaZagne.exeSHA-256: 467e49f1f795c1b08245ae621c59cdf06df630fc1631dc0059da9a032858a486
File Size: 9.66 MB
MD5: 5075f994390f9738e8e69f4de09debe6
(Source: Threatdown by Malwarebytes)
- Command line: LaZagne.exe database
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind