Ransomware attacks have increased a lot in the past year. Cybercriminals are using different tactics, so organizations need to monitor and investigate suspicious behaviors all the time.
According to a new report from Malwarebytes, “Ransomware gangs have time and motivation on their side. They constantly evolve to respond to the latest technologies chasing at their tails,” said Marcin Kleczynski, CEO, Malwarebytes. “We’ve seen this distinctly over the past year as the widespread adoption of technologies like EDR has helped identify attackers before they launch malware, pushing ransomware gangs to work more quickly and put more effort into hiding themselves. Organizations and MSPs need additional support and continuous coverage to outmaneuver criminals.”
Key findings:
* The US experienced a 63% increase in ransomware attacks, with the UK seeing an even greater rise of 67%.
- The share of gang attacks outside the top 15 increased from 25% to 31%, indicating that ransomware is becoming more accessible to a broader range of cybercriminals.
- The US accounts for 48% of all ransomware attacks worldwide but suffers 60% of the world’s attacks on education and 71% of attacks on healthcare.
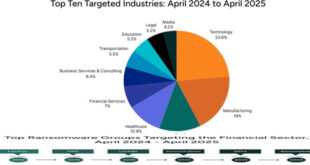
- The manufacturing sector saw a staggering 71% year-on-year increase in ransomware attacks, highlighting the need for robust cybersecurity measures in this digitizing industry.
Ransomware trends:
The report also features insights from the ThreatDown MDR team on three key shifts in the tactics and techniques of ransomware gangs:
Living off the Land () techniques:
Ransomware gangs are using more built-in system administration tools to carry out attacks.
Nighttime attacks:
Ransomware attacks on companies have increased in the past year. They are now more common during weekends and early morning hours when IT staff is not present. The majority of these attacks take place between 1 a.m. and 5 a.m.
Faster attack timelines:
Ransomware attacks are now happening much faster and require quicker detection and response capabilities.
“The question I ask organizations is do you have someone prepared to stop an attack at 2 a.m. on a Sunday with your existing technology stack and staff resources?” said Chris Kissel, Research Vice President, Security & Trust, IDC. “They may have a tool to pick up the alert on Monday morning but by then it will be too late. Threat actors are moving fast to compromise networks, download data and deploy ransomware. Having 24/7 coverage via a managed service will be key to keeping their organization safe while also tapping into the cost efficiency of an outsourced team.”) techniques: Ransomware gangs increasingly rely on built-in system administration tools to carry out their attacks, making detection and prevention more challenging for teams without a dedicated Security Operations Center (SOC).
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind