Microsoft has filed an amended complaint in recent civil litigation, naming the main developers of malicious tools that bypass the safeguards of generative AI services, including its Azure OpenAI Service. The legal action aims to stop their actions, dismantle their illegal operation, and deter others from misusing AI technology.
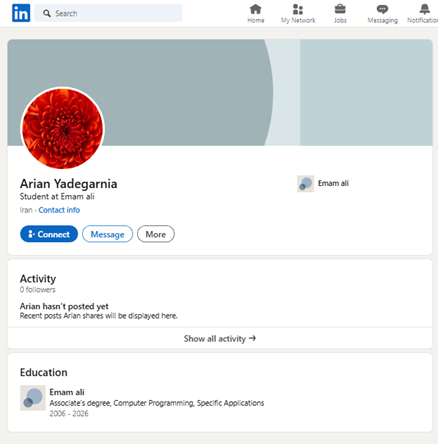
The individuals involved are: (1) Arian Yadegarnia (“Fiz”) from Iran, (2) Alan Krysiak (“Drago”) from the UK, (3) Ricky Yuen (“cg-dot”) from Hong Kong, and (4) Phát Phùng Tấn (“Asakuri”) from Vietnam. They are part of a global cybercrime network called Storm-2139, tracked by Microsoft. This group unlawfully accessed accounts of certain generative AI services by using exposed customer credentials. They then modified these services and resold access to others while providing instructions for generating harmful and illicit content, including non-consensual intimate images of celebrities.
This activity violates our generative AI services’ terms of use and involves intentionally bypassing our safeguards. We will not name specific celebrities to protect their privacy and have omitted synthetic images and prompts from our filings to prevent the spread of harmful content.
Storm-2139 is a global network of creators, providers, and end users. In December 2024, Microsoft’s Digital Crimes Unit (DCU) sued 10 unidentified individuals in Virginia for violating U.S. law and Microsoft’s policies. This lawsuit allowed us to learn more about the criminal operations involved.
Storm-2139 has three main categories: creators, providers, and users. Creators make the illegal tools for abusing AI services. Providers customize and distribute these tools to users, often with different service levels and payment options. Users then employ these tools to create harmful synthetic content, usually involving celebrities and sexual imagery.
Microsoft’s investigation has identified several personas, including four defendants. Two actors in the U.S., from Illinois and Florida, are known but their identities are kept confidential to protect ongoing criminal investigations. Microsoft is preparing to notify law enforcement in the U.S. and abroad.
Cybercriminals react to Microsoft’s website seizure and court filing.
The Court issued a temporary restraining order and preliminary injunction allowing Microsoft to seize a key website used in a criminal operation, disrupting the group’s services. The seizure and unsealing of legal documents in January prompted immediate reactions, leading some group members to blame each other. We noted discussions about the lawsuit on their monitored channels, speculating about the identities of the “John Does” and possible outcomes.
The discussion board features two posts. The first humorously claims that “fiz” leaked the name “Arian,” not “Arianna” or “Ariel.” The second post includes a LinkedIn URL containing “arian,” implying a link to the first post. Both are from an anonymous user with timestamps.

Screenshot of online chatter discussing “Fiz’s” real name.
Some members in these channels “doxed” Microsoft’s attorney by sharing their names, personal details, and photos. Doxing can lead to serious issues like identity theft and harassment.
The image features a discussion board post titled “DESU DEEP STRIKING INTO THIS THREAD.” An anonymous user shares a URL ending with “/offendants” and mentions having work profile images and contact information for attorneys from PDF documents. The post implies that they have enough information to create cards and suggest the attorneys are being monitored.
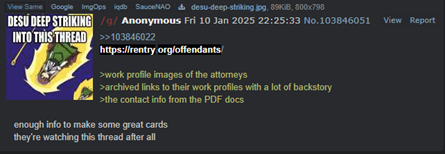
Screenshot from post on online channels providing information about the case lawyers.
Microsoft’s legal team received several emails, including ones from suspected Storm-2139 members trying to shift blame onto others in the group.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














