On November 26th, Microsoft patched four vulnerabilities detected in Dynamics 365 Sales, the Partner.Microsoft.Com portal, Microsoft Copilot Studio and Azure PolicyWatch.
Microsoft Copilot Studio, a platform for developers to create AI agents and speed up coding with automation, had a critical vulnerability rated 9.3 out of 10 (CVE-2024-49038). Microsoft has fully addressed this issue, and users do not need to take any action.
By infosecbulletin
/ Sunday , September 21 2025
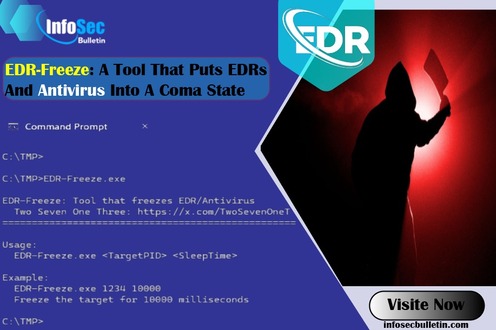
A new proof-of-concept tool named EDR-Freeze has been developed, capable of placing Endpoint Detection and Response (EDR) and antivirus solutions...
Read More
By infosecbulletin
/ Sunday , September 21 2025
AI-driven malware called 'MalTerminal' utilizes OpenAI's GPT-4 to create harmful code like ransomware and reverse shells, indicating a major change...
Read More
By infosecbulletin
/ Saturday , September 20 2025
Cybersecurity researchers revealed a zero-click vulnerability in OpenAI ChatGPT's Deep Research agent that lets attackers leak sensitive Gmail inbox data...
Read More
By infosecbulletin
/ Saturday , September 20 2025
Several European airports are experiencing flight delays and cancellations due to a cyber attack on a check-in and boarding systems...
Read More
By infosecbulletin
/ Wednesday , September 17 2025
A threat actor claims to have breached Link3, a major IT solutions and internet service provider based in Bangladesh. The...
Read More
By infosecbulletin
/ Wednesday , September 17 2025
Check point, a cyber security solutions provider hosts an event titled "securing the hyperconnected world in the AI era" at...
Read More
By infosecbulletin
/ Tuesday , September 16 2025
Cross-Site Scripting (XSS) is one of the oldest and most persistent vulnerabilities in modern applications. Despite being recognized for over...
Read More
By infosecbulletin
/ Monday , September 15 2025
Every day a lot of cyberattack happen around the world including ransomware, Malware attack, data breaches, website defacement and so...
Read More
By infosecbulletin
/ Monday , September 15 2025
A critical permission misconfiguration in the IBM QRadar Security Information and Event Management (SIEM) platform could allow local privileged users...
Read More
By infosecbulletin
/ Monday , September 15 2025
Australian banks are now using bots to combat scammers. These bots mimic potential victims to gather real-time information and drain...
Read More
Partner.Microsoft.Com, the official Microsoft partners’ portal, experienced a serious vulnerability (CVE-2024-49035) with a severity rating of 8.7/10, allowing for elevated privileges.
Microsoft has discovered that an improper access control flaw is being exploited. Unauthenticated attackers can use it to gain higher privileges on a network. No action is required from users as automatic patches are being released over the next few days.
Microsoft Azure PolicyWatch, a service for managing policies in Microsoft Azure, has a critical flaw rated 8.2/10 (CVE-2024-49052).
Microsoft confirmed that the vulnerability has been fully fixed, so users do not need to take any action.
Microsoft Dynamics 365 Sales, a cloud-based CRM solution, has a significant spoofing vulnerability rated 7.6 out of 10 (CVE-2024-49053).
Attackers could alter a vulnerable link to redirect victims to a malicious site, but they needed to be authenticated (not necessarily with admin privileges). Victims had to click a specially crafted URL to be at risk.
Microsoft said, “The vulnerability is in the web server, but the malicious scripts execute in the victim’s browser on their machine.”
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind