No vulnerabilities being exploited this month- Microsoft’s security update for February 2024. March’s Patch Tuesday is not as severe as previous months.
It addresses 60 vulnerabilities, with only two labeled as “critical.” In comparison, last month had over 70 security vulnerabilities. January and December had even fewer vulnerabilities, particularly when compared to 2023.
Two important vulnerabilities were fixed this month. They affect Windows Hyper-V and could allow an attacker to target a host machine from a virtual machine.
All other vulnerabilities Microsoft disclosed Tuesday are considered to be of “important” severity.
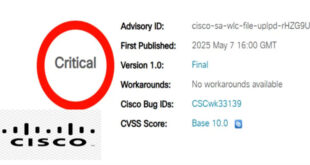
CVE-2024-21408 is a serious vulnerability in Windows Hyper-V that could be used to launch a denial-of-service attack from a virtual machine to the host machine. Despite being considered critical, it scored 5.5 out of 10 in the severity scoring system. Microsoft did not provide further details about how this attack could happen.
Another critical issue is CVE-2024-21407, which allows remote code execution in Hyper-V. An attacker in a VM could run code on the host machine by sending special file operation requests to hardware resources on the VM. However, the attacker would need to be authenticated in the VM and gather specific information about the environment to launch a successful attack.
Another remote code execution vulnerability — of which there are 19 in Tuesday’s release, CVE-2024-21334, exists in Open Management Infrastructure. A remote, unauthenticated attacker could exploit this vulnerability by accessing the OMI instance from the internet and sending specially crafted requests to trigger a use-after-free vulnerability.
CVE-2024-21334 is only considered by Microsoft to be “important,” though it has a CVSS score of 9.8 out of 10 — the highest of any vulnerability disclosed as part of March’s Patch Tuesday that affects a Microsoft product.
A complete list of all the other vulnerabilities Microsoft disclosed this month is available on its update page.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind