India is fast becoming one of the world’s largest connected nations – with over 80 Crore Indians (Digital Nagriks) presently connected and using the Internet and cyberspace – and with this number is expected to touch 120 Crores in the coming few years. The Digital Nagriks of the country are using the Internet for business, education, finance and various applications and services including Digital Government services. Internet provides growth and innovation and at the same time it has seen rise in cybercrimes, user harm and other challenges to online safety.
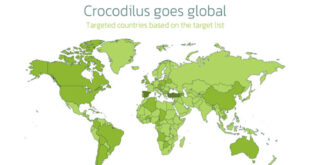
The policies of the Government are aimed at ensuring an Open, Safe & Trusted and Accountable Internet for its users. Government is fully cognizant and aware of the growing cyber security threats and attacks. It is the Government of India’s objective to ensure that Digital Nagriks experience a Safe & Trusted Internet. Along with ubiquitous applications of Information & Communication Technologies (ICT) in almost all facets of service delivery and operations, continuously evolving cyber threats have become a concern for the Government. Cyber-attacks can come in the form of malware, ransomware, phishing, data breach etc., that adversely affect an organisation’s information and systems.
Cyber threats leading to cyber-attacks or incidents can compromise the confidentiality, integrity, and availability of an organisation’s information and systems and can have far reaching impact on essential services and national interests. To protect against cyber threats, it is important for government entities to implement strong cybersecurity measures and follow best practices. As ICT infrastructure of the Government entities is one of the preferred targets of the malicious actors, responsibility of implementing good cyber security practices for protecting computers, servers, applications, electronic systems, networks, and data from digital attacks, also remain with the ICT assets’ owner i.e. Government entity.
“Indian Computer Emergency Response Team (CERT-In)” has been established and appointed as national agency in respect of cyber incidents and cyber security incidents in terms of the provisions of section 70B of Information Technology (IT) Act, 2000 (IT Act, 2000) to perform
The following functions in the area of cyber security: –
- a) collection, analysis and dissemination of information on cyber incidents;
- b) forecast and alerts of cyber security incidents;
- c) emergency measures for handling cyber security incidents;
- d) coordination of cyber incidents response activities;
- e) issue guidelines, advisories, vulnerability notes and whitepapers relating to information security practices, procedures, prevention, response and reporting of cyber incidents;
- f) such other functions relating to cyber security as may be prescribed.
Guidelines on Information Security Practices for Government Entities The Indian Computer Emergency Response Team(CERT-In) is satisfied that for the purposes of performing the aforesaid functions, it is necessary and expedient in the interest of cyber security that guidelines relating to information security practices, procedures, prevention and response be issued in exercise of the powers conferred by clause (e) of sub-section (4) of section 70B of the Information Technology Act, 2000 (21 of 2000) for all the Ministries, Departments, Secretariats and Offices specified in the First Schedule to the Government of India (Allocation of Business) Rules, 1961, their attached and subordinate offices, and all government institutions, public sector enterprises and other government agencies under their administrative purview (hereinafter collectively referred to as “government entities”); and it is expected that the said guidelines be carried out by all government entities by doing necessary acts and things required in this regard;
The purpose of these guidelines is to establish a prioritized baseline for cyber security measures and controls within government organizations and their associated organizations. The guideline shall assist security teams to implement baseline and essential controls and procedures to protect their Cyber infrastructure from prominent threats. These guidelines shall also act as a baseline document for administration and audit teams (internal, external/ Third-party auditors) to evaluate an organization’s security posture against cyber security baseline requirements. These guidelines cover best practices segregated in different security domains such as Network Security, Application Security, Data Security, Auditing, Third Party Outsourcing. Due to the ever-evolving threat landscape, this document is envisaged to be an organic document and would be updated as per changing threat landscape.
Click Here to download.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind