A threat actor likely operating out of India is relying on various cloud services to conduct cyberattacks against energy, defense, government, telecommunications, and technology entities of Bangladesh, Cloudflare reports.
Tracked as SloppyLemming, this group is linked to Outrider Tiger, a threat actor associated with India, previously Crowdstrike said, that uses emulation frameworks like Sliver and Cobalt Strike in its attacks.
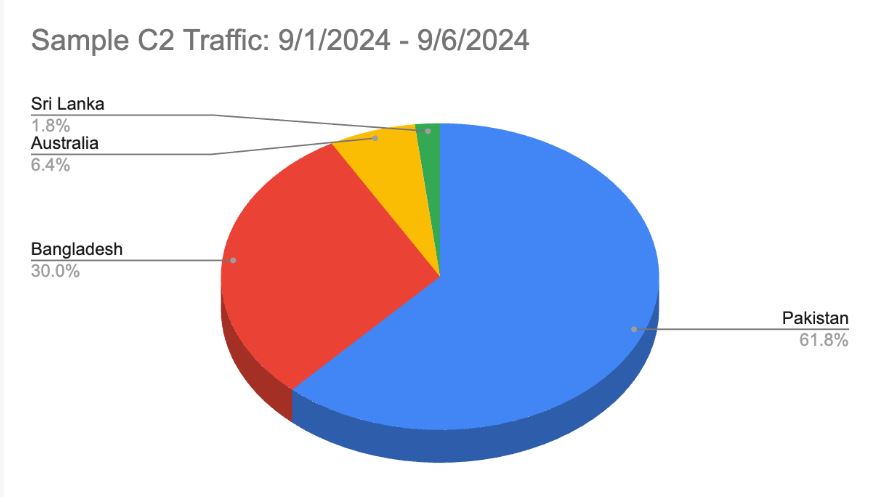
According to Cloudflare report, The bad actor conducts extensive operations targeting Pakistani, Sri Lanka, Bangladesh, and China. Industries targeted include government, law enforcement, energy, telecommunications, and technology entities.
“SloppyLemming extensively uses credential harvesting as a means to gain access to targeted email accounts within organizations that provide intelligence value to the actor,” Cloudflare notes.
The threat actor uses phishing emails to send malicious links to victims. They employ a custom tool called CloudPhish to create harmful Cloudflare Workers for stealing credentials and use scripts to gather important emails from victims’ accounts.
SloppyLemming tried to collect Google OAuth tokens during some attacks, sending them to the actor via Discord. The attacks involved malicious PDF files and Cloudflare Workers.
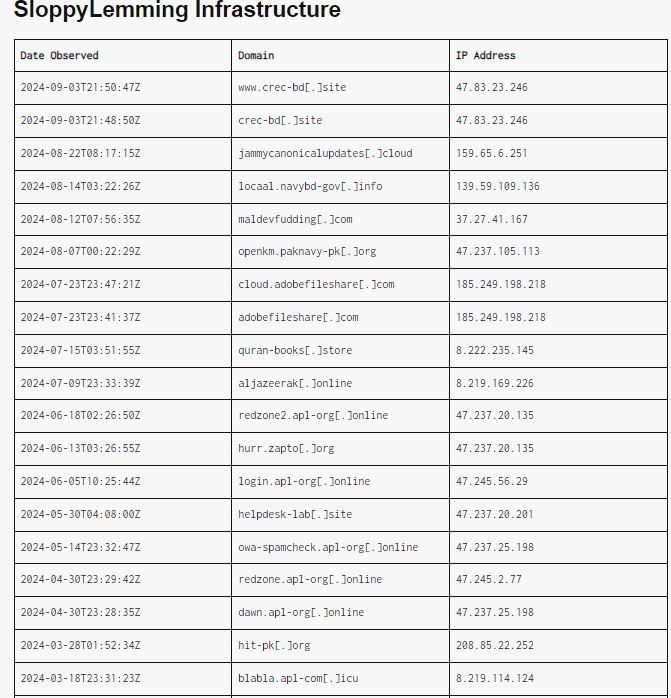
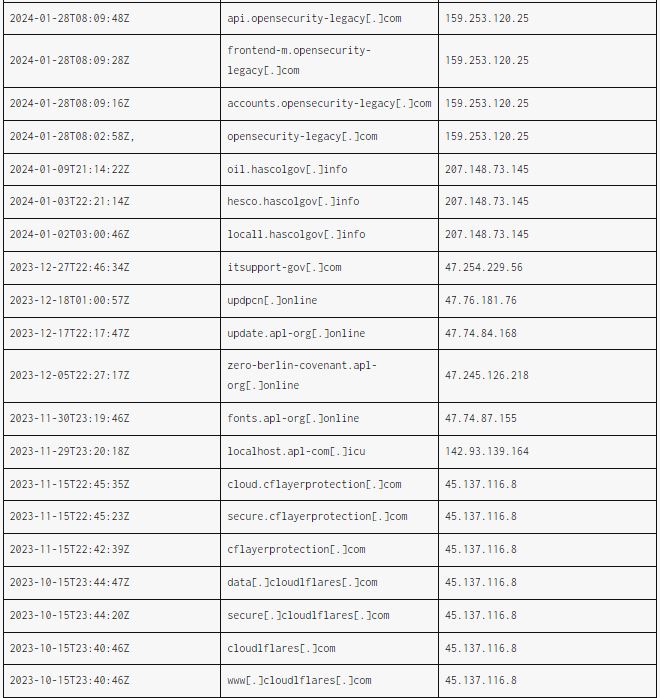
SloppyLemming was seen sending spear-phishing emails that use code from a GitHub repository controlled by the attacker. This code checks when a victim clicks the phishing link. The malware communicates with a Cloudflare Worker, which forwards requests to the attacker’s command-and-control server.
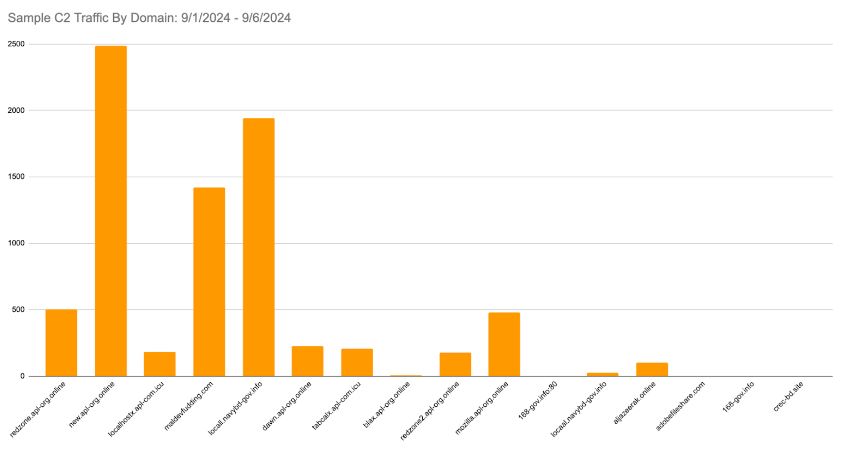
Cloudflare has found several C&C domains used by a threat actor, and their recent traffic suggests that SloppyLemming may intend to expand operations to Australia or other countries.
“Between late 2022 to present, SloppyLemming has routinely used Cloudflare Workers, likely as part of a broad espionage campaign targeting South and East Asian countries,” Cloudflare said in an analysis.
It’s worth mentioning here that cybersecurity company SEQRITE detailed an analogous campaign undertaken by the SideCopy actors last year targeting Indian government and defense sectors to distribute the Ares RAT using ZIP archives named “DocScanner_AUG_2023.zip” and “DocScanner-Oct.zip” that are engineered to trigger the same vulnerability.
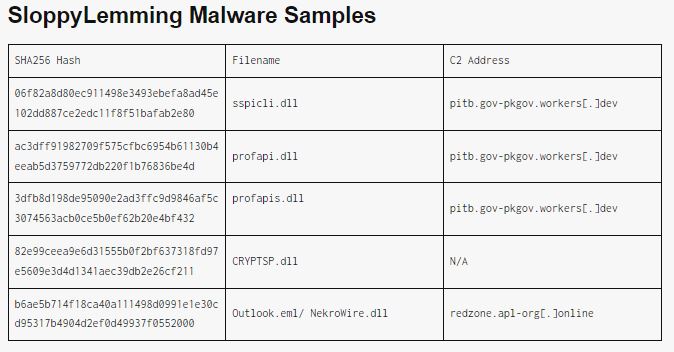
Indicators of Compromise:
Bangladesh Bank published draft “Cyber Security Framework” V.1.0
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














