Hackers target Bangladeshi many WordPress based e-commerce sites for their illegal activities. Getting access they are now offer to sell the taken access on the dark web. But, the alarming issue is that on those post not any specific site name has been mentioned. So, this is really difficult to realize which sites are actually been compromised.
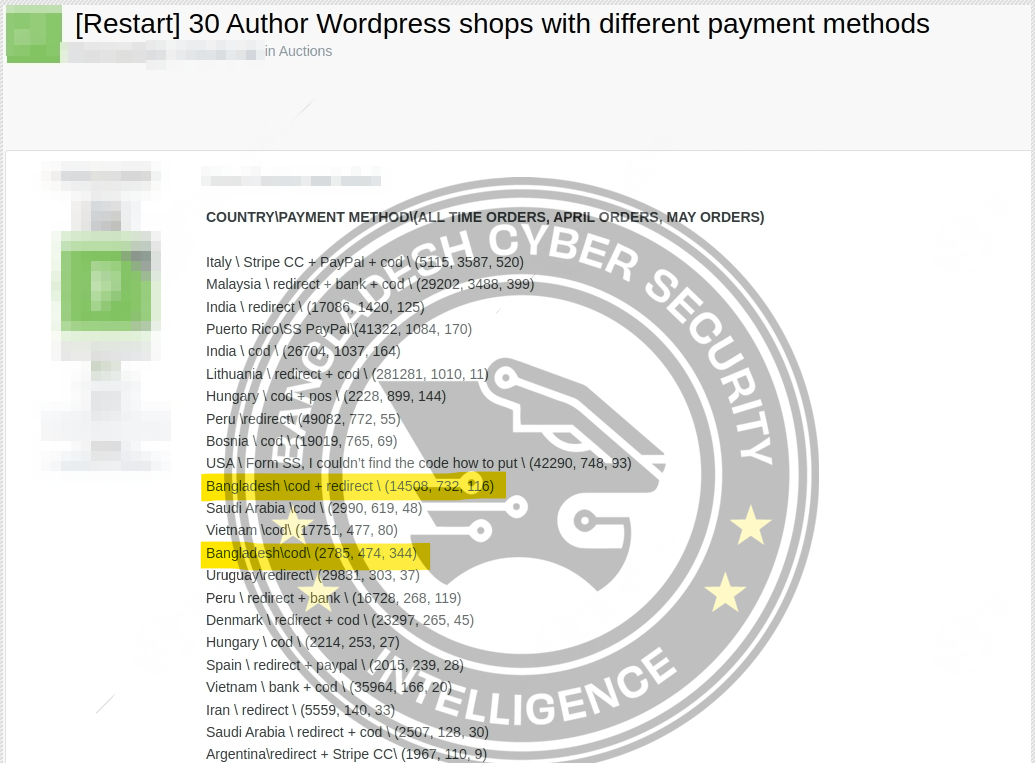
BCSI said, a close inspection of the data indicate that Bangladeshi Cash on delivery (COD) sites and Redirect payment methods are mostly targeted by the cyber criminal. With 17,293 all-time orders, 1,206 orders in April, and 460 orders in May, these shops are prime targets due to the volume of transactions and the potential value of the data involved.
The Threat Uncovered:
For various reasons like outdated plugins, weak passwords, or other security loopholes hackers to gain control the sites. When they got access, they put it up for auction. This could result in financial losses, reputational damage, and operational disruptions.
Potential Risks for Bangladeshi E-Commerce:
As Bangladeshi e-commerce industry is growing up, such unauthorized access incidents pose significant risks:
Customer Data Breach:
Unauthorized access may cause sensitive customer information to be leaked. This includes personal mobile numbers, delivery addresses, email addresses, and payment information. Such a breach can seriously impact customer privacy and trust.
Financial Losses:
Cybercriminals could conduct fraudulent transactions, steal funds, or demand ransom, leading to direct financial harm to the businesses.
Reputational Damage:
If customer data is exposed, they lose trust in the platform, which can hurt business and the brand’s reputation.
Operational Disruption:
Unauthorized access can cause significant problems for businesses operations.
Strengthening WordPress Security:
To combat these threats, BCSI suggested that Bangladeshi e-commerce businesses must enhance their security measures. Here are some essential steps:
Regular Updates:
Keep your WordPress core, themes, and plugins updated. These updates usually fix security issues.
Strong Passwords:
Create strong, unique passwords for each account you have. Consider using a password manager to safely keep track of these complex passwords.
Two-Factor Authentication (2FA):
Adding 2FA greatly enhances security by reducing unauthorized access risk.
Security Plugins:
Utilize security plugins for monitoring and site protection against potential threats.
Regular Backups:
Make sure to regularly back up your WordPress site. If there’s a security breach, having a recent backup can help you restore the site with minimal data loss.
Monitoring and Audits:
Regularly assess site performance and perform security checks to promptly discover and fix vulnerabilities.
Unauthorized WordPress access sales are a major issue for e-commerce businesses in Bangladesh. To protect themselves and their customers, businesses should understand the threat and take proactive security measures. It is important to stay updated on cybersecurity threats to maintain a safe online marketplace.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














