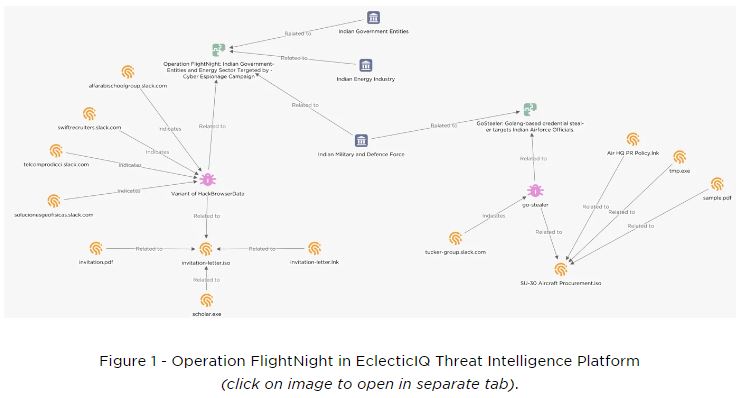
A new spying campaign has been discovered that targets Indian government agencies and the energy sector, using a modified open-source tool called HackBrowserData to steal browser credentials, cookies, and history.
Researchers from EclecticIQ, a Dutch cybersecurity firm, found a hacking campaign in early March. They didn’t identify the hackers but reported that 8.81 GB of data was stolen. This data could help further attacks on the Indian government’s infrastructure.
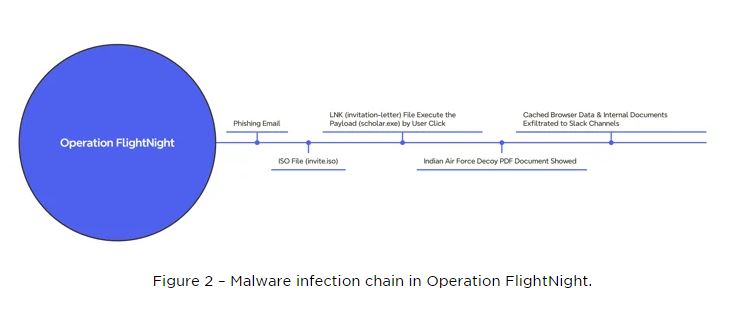
The information stealer spread through a fake invitation letter from the Indian Air Force, sent as a PDF through phishing. It’s believed that the PDF was originally taken in an earlier attack and reused by the cybercriminals.
The document contained a shortcut (LNK file) that led to malware. When activated, this malware started stealing documents, private emails, and web browser data from the victim’s device, sending this information through Slack.
Analysts from EclecticIQ named the campaign “Operation FlightNight” because the attackers named all their Slack channels “FlightNight.”
The malware targets specific file types like Microsoft Office documents, PDFs, and SQL database files on devices to speed up data theft during exfiltration.
Hackers targeted Indian government agencies in electronic communications, IT governance, and national defense, as well as private energy companies, stealing financial documents, employee personal details, and information on oil and gas drilling activities.
The hacker group responsible wasn’t named, but similarities in the malware and delivery techniques suggest a link to a previous attack targeting Indian Air Force officials with a malware called GoStealer.
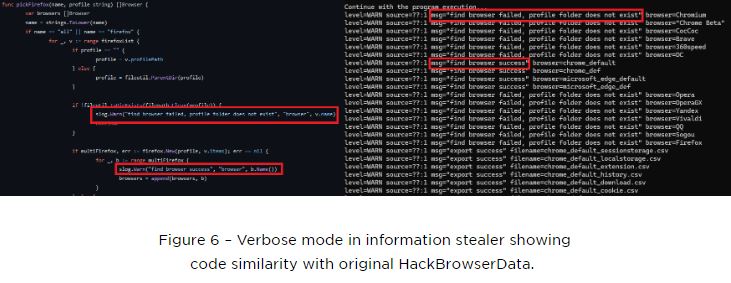
The malware used in the attack was a modified version of GoStealer, a type of malware available on GitHub. It attacked several browsers including Firefox, Chrome, Edge, and Brave, and stole data through Slack.
According to EclecticIQ, both campaigns are likely the work of the same threat actor targeting Indian government entities.
“Operation FlightNight and the Go-Stealer campaign highlight a simple yet effective approach by threat actors to use open-source tools for cyber espionage,” researchers said.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














