GitLab released patches for a critical flaw in Community and Enterprise Editions that could allow authentication bypass. The vulnerability in the ruby-saml library (CVE-2024-45409, CVSS score: 10.0) could let an attacker log in as any user in the affected system. It was fixed by the maintainers last week.
The issue arises from the library not verifying the SAML Response’s signature correctly. SAML, or Security Assertion Markup Language, is a protocol for single sign-on (SSO) and sharing authentication and authorization data between applications.
By infosecbulletin
/ Wednesday , September 10 2025
Microsoft has issued a new warning about a critical security vulnerability in Active Directory Domain Services, known as CVE-2025-21293. An...
Read More
By infosecbulletin
/ Wednesday , September 10 2025
Sophos fixed an authentication bypass vulnerability in its AP6 Series Wireless Access Points, preventing attackers from obtaining admin privileges. The...
Read More
By infosecbulletin
/ Wednesday , September 10 2025
Security researcher Jeremiah Fowler discovered a database containing sensitive information from gym customers and staff, including names, financial details, and...
Read More
By infosecbulletin
/ Wednesday , September 10 2025
Microsoft patched September 2025 Patch Tuesday 81 flaws, including two publicly disclosed zero-day vulnerabilities. This Patch Tuesday addresses nine critical...
Read More
By infosecbulletin
/ Tuesday , September 9 2025
Elastic reported a security incident caused by a breach at Salesloft Drift, leading to unauthorized access to an internal email...
Read More
By infosecbulletin
/ Tuesday , September 9 2025
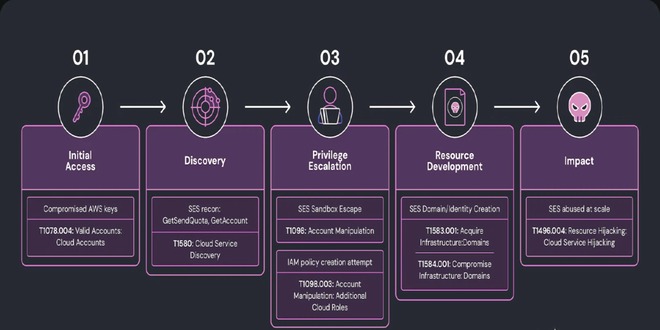
Researchers at Wiz discovered a complex phishing campaign using Amazon's Simple Email Service (SES) for large-scale attacks, showing how hacked...
Read More
By infosecbulletin
/ Monday , September 8 2025
The global ransomware landscape continues to shift in 2025, with SafePay rapidly emerging as one of the most active and...
Read More
By infosecbulletin
/ Sunday , September 7 2025
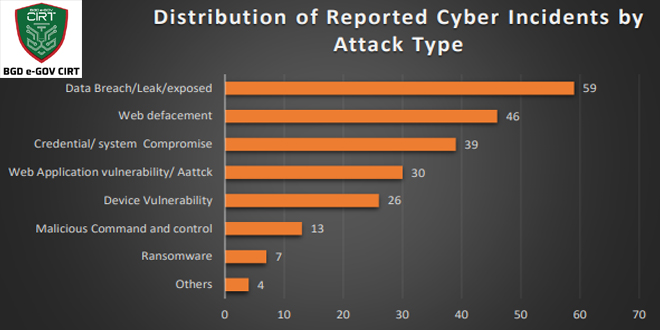
Bangladesh Cyber Threat Landscape 2024, by BGD e-GOV CIRT, reveals a sharp escalation in cyber threats across Bangladesh. The year...
Read More
By infosecbulletin
/ Sunday , September 7 2025
Investigations into the Nx "s1ngularity" NPM supply chain attack have unveiled a massive fallout, with thousands of account tokens and...
Read More
By infosecbulletin
/ Saturday , September 6 2025
ISC2 has launched a Threat Handling Foundations Certificate to assist cybersecurity experts in enhancing Digital Forensics and Incident Response (DFIR)...
Read More
“An unauthenticated attacker with access to any signed SAML document (by the IdP) can thus forge a SAML Response/Assertion with arbitrary contents, according to a security advisory. “This would allow the attacker to log in as arbitrary user within the vulnerable system.”
“The vulnerability also affects omniauth-saml, which has released its own update (version 2.2.1) to fix ruby-saml to version 1.17.” “The latest patch from GitLab is designed to update omniauth-saml to version 2.2.1 and ruby-saml to 1.17.0.”
GitLab is advising users to enable two-factor authentication (2FA) for all accounts and prevent the SAML two-factor bypass option.
“Successful exploitation attempts will trigger SAML related log events,” it said. “A successful exploitation attempt will log whatever extern_id value is set by the attacker attempting exploitation.”
“Unsuccessful exploitation attempts may generate a ValidationError from the RubySaml library. This could be for a variety of reasons related to the complexity of crafting a working exploit.”
“Recently, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added five new security flaws to its Known Exploited Vulnerabilities (KEV) catalog, including a serious bug affecting Apache HugeGraph-Server (CVE-2024-27348, CVSS score: 9.8), with evidence showing it is actively being exploited.”
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind