Researchers from VulnCheck have observed a campaign using real security researchers as bait for malware. The campaign goes to some lengths to appear genuine, using fake profiles, downloads, websites, and bogus GitHub profiles, to paint a convincing picture of security professionals offering up exploit code for popular programs.
The campaign included a network of fictitious Twitter accounts posing as employees of a firm called “High Sierra Cyber Security”. The Record notes that several photographs of real security researchers working at well known firms were misused in the campaign.
ALSO READ:
Microsoft says disruptions to Outlook, cloud platform, were cyberattacks
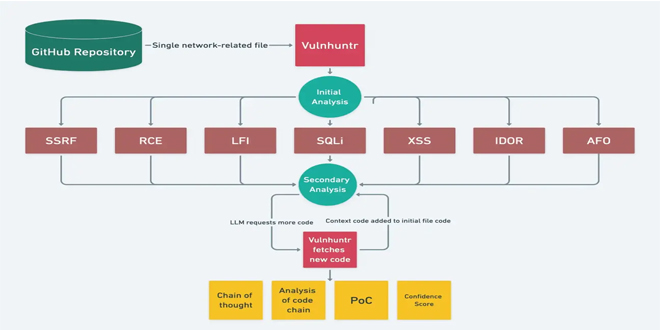
The tale begins in May of this year, with the discovery of a malicious GitHub repository claiming to be for a zero-day attack for the Signal messaging app. This bogus offering was taken down, but the group behind the page were determined to stick around.
New downloads were offered, but this time in the guise of the previously mentioned security entities. Every High Sierra Cyber Security account claiming to offer exploits for well known products was actually offering up malicious repositories harbouring malware. The supposedly exploitable products included Chrome, Discord, and Exchange. All popular programs, and guaranteed to grab the attention of anyone interested in the security space.
The people behind this leaned heavily into social media to make it all look real, promoting their “finds” on networks such as Twitter. This was a risky gambit for the creators of this malware scam. While it added legitimacy to the overall gameplan, it ran the risk of someone realising that one of the security researchers actually worked somewhere else. This is indeed exactly what happened, and more researchers were identified from the stolen images as the days went by.
The GitHub pages also leaned into social aspects, making use of popular tags like “discordapp”, “cve”, and “rce-exploits” to draw more potential victims in to look at the rogue pages. They must have known that using tags like that would guarantee actual security researchers taking a look and saying “Wait a minute…”
While the GitHub pages are all now offline, the fake Twitter accounts are still live. VulnCheck notes that if you’ve interacted with any of the GitHub pages and Twitter accounts listed on its advisory, you may have been compromised if you downloaded and executed the files.
The GitHub accounts and repositories discovered by VulnCheck are as follows:
GitHub Accounts
- github.com/AKuzmanHSCS
- github.com/RShahHSCS
- github.com/BAdithyaHSCS
- github.com/DLandonHSCS
- github.com/MHadzicHSCS
- github.com/GSandersonHSCS
- github.com/SSankkarHSCS
Malicious Repositories
- github.com/AKuzmanHSCS/Microsoft-Exchange-RCE
- github.com/MHadzicHSCS/Chrome-0-day
- github.com/GSandersonHSCS/discord-0-day-fix
- github.com/BAdithyaHSCS/Exchange-0-Day
- github.com/RShahHSCS/Discord-0-Day-Exploit
- github.com/DLandonHSCS/Discord-RCE
- github.com/SSankkarHSCS/Chromium-0-Day
If any of the above look familiar, and if you recognise any of the usernames from their matching Twitter accounts, it may well be time to run some security scans on your PC. It’s not unusual for security researchers themselves to be targeted by scams and attacks. If nothing else it’s a major win for malware authors and people up to no good, the bigger the target’s name the better.
However, it’s not quite as common to see security researchers themselves used as a way to infect others online. This is a valuable reminder to always check code you download before executing it. If in doubt, ask someone more familiar with whatever it is you’re trying to do. As a general rule, “download this cool exploit for popular program X” tends to not work out very well for the person or organization downloading it.
Source: Malwarebytes lab
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind